Password Forensics & Identity Compromise Recovery

Threats and Vulnerabilities
Iranian Cyber Campaigns Turn Destructive Against U.S. OT
Pumps slowed, screens flickered, and credentials worked a little too well—signals that a familiar adversary had moved beyond spying to tampering with the machinery of daily life and the systems that keep it running safely and on time.
Read More Human Factors in CyberSecurity
Are Your Passwords Leaving New Jersey Open to Attack?
Rattling off the same easy password for streaming, shopping, and banking felt like a time-saver until that shortcut began acting like a neon “open” sign for automated break-ins that never sleep and rarely miss.
Read More Incident Response and Forensics
Could BlackFile’s IT-Support Vishing Hit Your Execs Next?
A stranger on the phone sounds like IT, knows an executive’s nickname, and asks for a quick SSO reset that unlocks the whole cloud, turning a friendly favor into an entry point for theft, coercion, and seven‑figure demands.
Research Summary Read More Incident Response and Forensics
How Does the Vercel Breach Impact Your Cloud Security?
When a developer discovers that their highly secure cloud environment was accessed through a seemingly benign third-party productivity tool, the illusion of perimeter security evaporates instantly.
Read More Human Factors in CyberSecurity
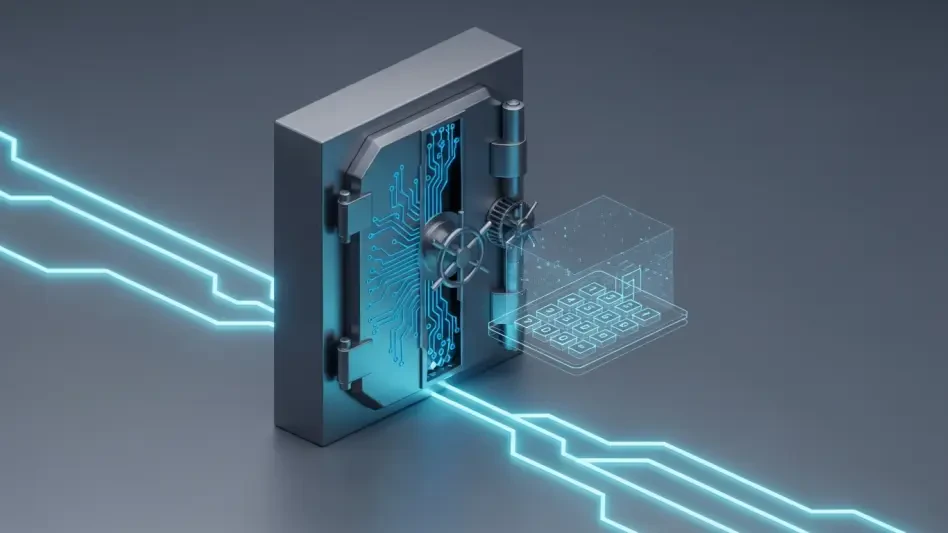
PiNetDEX Enhances Security With New Two-Factor Authentication
Digital asset management has reached a critical juncture where the convenience of mobile interfaces must harmonize with the unyielding security requirements of blockchain technology to protect global users.
Read More Cyberсrime and Cyber Warfare
CAC Enforces Password Reset and 2FA on Registration Portal
The recent wave of sophisticated cyberattacks targeting national digital infrastructure has forced a paradigm shift in how government agencies protect sensitive corporate data and user information.
Read More Human Factors in CyberSecurity
How Did Scattered Spider Steal $8 Million in Crypto?
The realization that a small group of young, native English-speaking hackers could systematically dismantle the security of multi-billion dollar corporations serves as a stark reminder of the inherent vulnerabilities in modern digital infrastructure.
Trending
Read More Cyberсrime and Cyber Warfare
How Is the Vect Syndicate Industrializing Ransomware?
The traditional model of isolated cybercriminals operating from dark corners has vanished, replaced by a streamlined, multi-organizational machine that treats digital extortion as a legitimate global business venture.
FAQ Read More
Get our content freshly delivered to your inbox. Subscribe now ->
Receive the latest, most important information on cybersecurity.