Global Cyberattacks & Response
Cyberсrime and Cyber Warfare
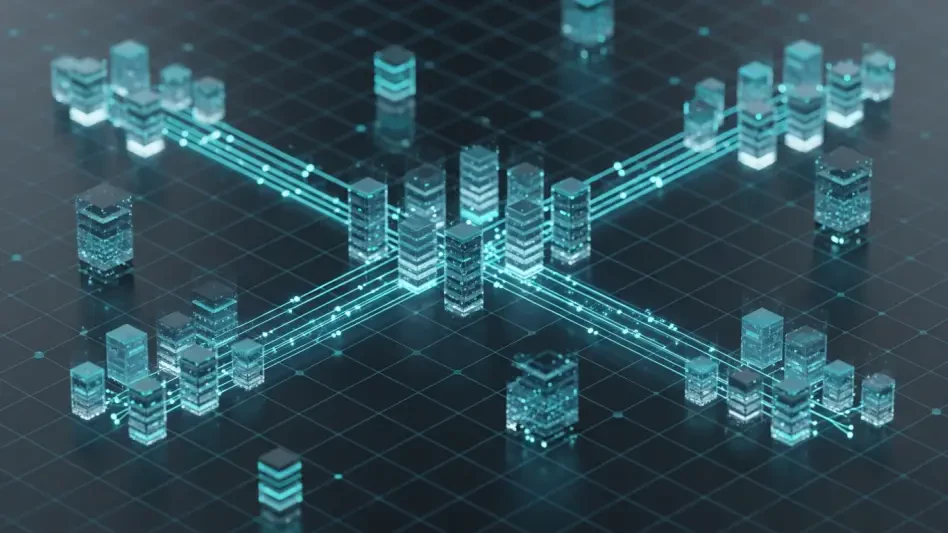
Massive DDoS Attack Uses 1.2 Million IPs to Evade Detection
The digital landscape witnessed a profound escalation in cyber warfare recently as a major user-generated content platform faced a relentless assault consisting of 2.45 billion malicious requests over a short five-hour window.
Read More Human Factors in CyberSecurity
Microsoft Detects Massive Phishing Attack Bypassing MFA
The cybersecurity landscape recently witnessed a profound escalation in complexity as a massive phishing campaign successfully infiltrated over 13,000 organizations across the globe within a single forty-eight-hour window in April 2026.
Read More Cyberсrime and Cyber Warfare
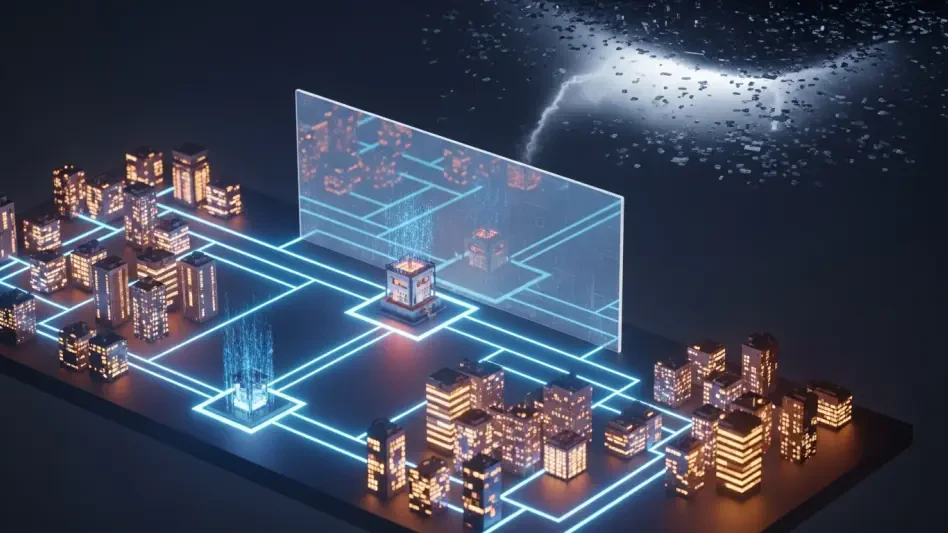
CISA Launches CI Fortify to Boost Infrastructure Resilience
The fundamental reliability of the nation’s power grid and water supply now hinges on a system's ability to survive a total digital blackout rather than merely deflecting individual hacking attempts.
Feature Article Read More Human Factors in CyberSecurity
WEF Outlines Strategic Framework for AI in Cybersecurity
The flickering glow of a security operations center monitor no longer reveals a simple struggle between a lone hacker and a diligent defender, but rather a silent, invisible collision between two complex algorithms operating at speeds far beyond huma...
Feature Article Read More Cyberсrime and Cyber Warfare
Who Is the Shadowy Group Targeting Global Infrastructure?
The silent infiltration of national power grids and governmental communication channels has become a recurring nightmare for security researchers monitoring a sophisticated entity known as SHADOW-EARTH-053.
Read More Threats and Vulnerabilities
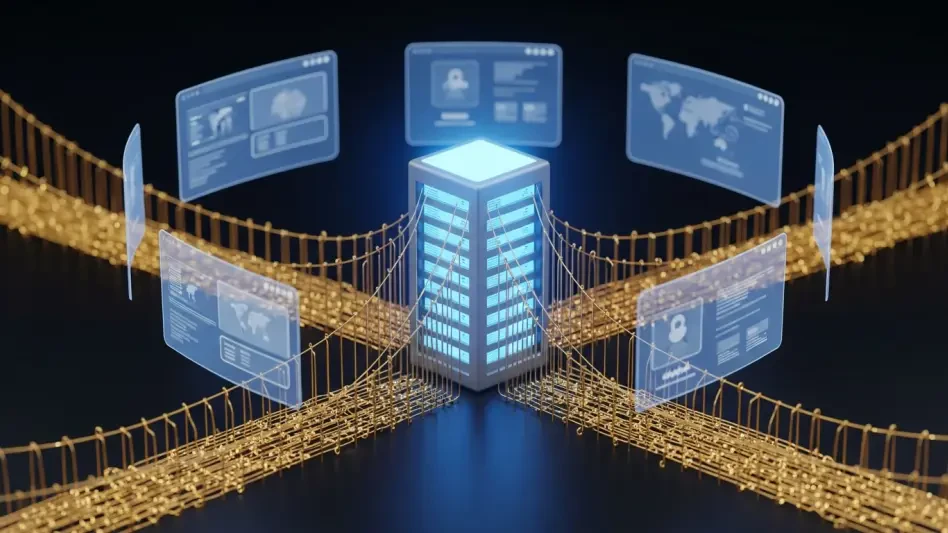
How Will Claude Security Change Enterprise Cyber Defense?
The relentless acceleration of software development cycles has historically forced a trade-off between the speed of deployment and the rigor of security audits, leaving many organizations vulnerable to sophisticated zero-day exploits.
Read More Cyberсrime and Cyber Warfare
How Did the Versus Project Dark Web Empire Collapse?
The sudden extradition of a thirty-seven-year-old German national from the coastal town of Taganga, Colombia, to a federal courtroom in New Jersey marks the definitive end of one of the most prolific dark web operations in recent history.
Read More Cyberсrime and Cyber Warfare
FEMITBOT Operation Exploits Telegram Mini Apps for Fraud
The emergence of sophisticated fraudulent ecosystems within popular messaging platforms has fundamentally altered the digital threat landscape for millions of mobile users globally.
Trending
Read More 
Get our content freshly delivered to your inbox. Subscribe now ->
Receive the latest, most important information on cybersecurity.