The fundamental reliability of the nation’s power grid and water supply now hinges on a system’s ability to survive a total digital blackout rather than merely deflecting individual hacking attempts. For decades, the philosophy of digital defense centered on building higher walls and deeper moats to keep intruders out of sensitive networks. However, as cyber threats evolve into persistent, state-sponsored campaigns aimed at societal disruption, the Cybersecurity and Infrastructure Security Agency (CISA) has acknowledged a difficult truth: the walls will eventually be breached. This recognition forms the core of CI Fortify, a program designed to redefine how the country protects its most vital assets by prioritizing survival over perfection.
Beyond Cyber Defense: Moving Toward Operational Continuity in an Era of Persistent Threats
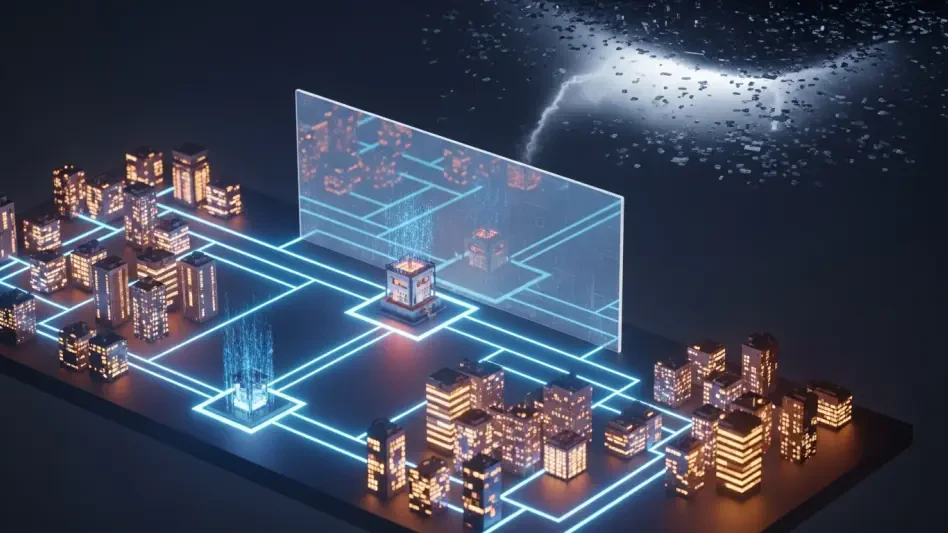
The traditional cybersecurity perimeter has become increasingly porous, making the total prevention of network breaches an unrealistic goal for modern critical infrastructure. For years, the security community focused on threat detection and perimeter defense, but the sheer complexity of interconnected systems has rendered these methods insufficient against a determined adversary. In response, CISA has introduced the “CI Fortify” initiative, a strategic pivot that prioritizes the ability to maintain essential services even when primary networks are compromised. This program marks a departure from the “zero-trust” buzzwords of the past, moving instead toward a practical “assumed-breach” architecture where the primary objective is to keep the lights on and the water flowing, regardless of the status of the business network.
The initiative recognizes that during peak geopolitical tensions, the success of national defense and public safety depends less on blocking every intrusion and more on the ability of systems to function in a degraded or isolated state. This means that infrastructure operators must begin treating their operational technology (OT) as independent lifeboats rather than extensions of the corporate office. The shift requires a fundamental reimagining of how technology serves the mission, emphasizing resilience as the capacity to absorb a shock and continue functioning. By focusing on “degraded-state operations,” CISA is guiding organizations to develop protocols that allow for manual control and local decision-making when the automated, internet-dependent systems they have grown to rely on are suddenly unavailable or untrustworthy.
Moving toward this model involves more than just software updates; it requires a cultural change within engineering and IT departments. Historically, efficiency drove the convergence of business and industrial networks, allowing for remote monitoring and predictive maintenance from anywhere in the world. While this connectivity brought economic benefits, it also created a massive attack surface that adversaries have learned to exploit. CI Fortify challenges this “always-on” mentality by asking operators to identify the absolute minimum requirements for service delivery. The goal is to ensure that even if the digital nervous system of an organization is paralyzed by ransomware or a state-sponsored attack, the physical heart of the operation continues to beat through pre-planned, localized workarounds.
The Geopolitical Catalyst: Why Infrastructure Resilience Requires a New Paradigm
The shift toward CI Fortify is driven by a sobering reality: adversaries are no longer just looking for data; they are positioning themselves to disrupt the digital foundations of society. Over the last several years, intelligence reports have highlighted a disturbing trend where foreign actors are not engaging in simple industrial espionage but are instead embedding themselves within critical systems to await a signal for activation. As global conflicts evolve, critical infrastructure—ranging from power grids to public health systems—is increasingly viewed as a primary target for disabling strikes. This new era of “pre-positioning” means that a breach in a third-party vendor or a business network can cascade into OT environments, potentially leading to catastrophic physical consequences during a time of international crisis.
The initiative addresses the vulnerability of “always-on” connectivity, where the convenience of the cloud has become a potential liability for national security. Many utilities and manufacturing plants now rely on remote telemetry and cloud-based analytics to manage day-to-day operations. While these tools improve performance, they also create a direct pathway for an attacker to travel from a phishing email in a marketing department to the control valves of a chemical plant. By preparing for “worst-case” scenarios, CISA aims to ensure that lifeline services remain steadfast regardless of the digital chaos occurring on the public internet. This proactive stance acknowledges that in a theater of modern conflict, the domestic front is the digital front, and the resilience of a local water district is just as vital as the readiness of a military base.
Furthermore, the interconnected nature of global supply chains has made it nearly impossible for any single entity to be completely secure. A vulnerability in a common piece of industrial software or a compromise at a managed service provider can have a ripple effect across thousands of organizations simultaneously. This systemic risk is what necessitates a new paradigm centered on isolation. By decoupling the critical functions of society from the volatile and often insecure public internet, the CI Fortify framework seeks to create a “firebreak” that prevents a digital wildfire from consuming the physical infrastructure. This strategy moves the focus away from the attacker’s capabilities and toward the defender’s endurance, making the disruption of American life an increasingly difficult and unrewarding task for any adversary.
The Operational Pillars of CI Fortify: Isolation and System Recovery
The initiative is anchored by two fundamental objectives designed to decouple critical services from vulnerable networks. The first pillar, Operational Isolation, focuses on the ability to disconnect OT networks from the internet and corporate environments without stopping service delivery. This is not merely about pulling a plug; it is an engineering challenge that requires organizations to identify “priority customers” and establish service delivery targets that can be met during a total communications blackout. Isolation requires a granular understanding of which systems are truly essential and which are merely convenient. For example, a power utility must be able to manage load and distribution using local manual controls if its centralized, internet-connected management system is compromised.
The second pillar, System Recovery, emphasizes the restoration of functions if isolation fails or if a breach occurs before defenses can be moved to an offline state. This involves maintaining secure, offline backups that are physically separated from the primary network to prevent them from being encrypted or deleted during a ransomware attack. However, recovery is more than just having a backup; it involves meticulously mapping “hidden” dependencies that could prevent a system from rebooting. Many modern industrial controllers require a “handshake” with an external licensing server or a cloud-based update service to function. If the internet is down or the vendor’s server is under attack, the system may refuse to start. CI Fortify encourages operators to work with vendors to eliminate these “kill switches” and ensure that systems can be restored using only local resources.
To make these pillars effective, organizations must engage in rigorous testing and validation of their manual transition plans. It is one thing to have a plan on paper; it is another to expect a workforce that has relied on automation for a decade to suddenly manage complex machinery via manual dials and local overrides. CISA’s framework stresses the importance of regular drills where teams practice operating in a “blind” environment. By simulating a total loss of digital visibility, operators can identify the gaps in their documentation and the weaknesses in their recovery tools. This level of preparation ensures that when a real crisis occurs, the response is a practiced routine rather than a frantic attempt to invent new procedures under the pressure of an active attack.
Ecosystem Responsibility and Expert Critiques of the Resilience Framework
Building a resilient infrastructure is a collective endeavor that extends beyond the operators themselves to include vendors, integrators, and security providers. CISA calls on industrial automation vendors to remove licensing barriers that hinder software functionality in an isolated state, as these digital locks can become points of failure during a national emergency. Managed service providers, who often hold the keys to the kingdom for small and medium-sized utilities, are tasked with supporting the engineering updates necessary for manual workarounds. The responsibility for resilience is thus distributed across the entire technology ecosystem, requiring a commitment from software developers to prioritize “resilience by design” over purely functional or aesthetic updates.
Industry experts have offered both praise and critical refinements to the CI Fortify vision. Xage Security CEO Duncan Greatwood has pointed out that while isolation is a critical goal, it must be paired with robust internal segmentation to prevent lateral movement from “trusted” connections. He argues that many attacks do not come from the “outside” in the traditional sense but instead exploit credentials or devices that are already inside the perimeter. Therefore, isolation from the internet must be accompanied by an internal architecture that treats every user and device as a potential threat. Furthermore, experts like Bill Moore of Xona Systems highlight the ongoing need for crisis-ready remote access. He suggests that in a crisis, engineers may still need to reach systems from a distance, but they must do so through precise, session-based control rather than the broad, risky network-level trust inherent in traditional VPNs.
The critique from the private sector underscores the tension between security and operational reality. Operators often resist isolation because it complicates maintenance and increases costs. However, the consensus among security leadership is that the cost of a catastrophic failure far outweighs the investment in resilience. CISA’s role is to act as a bridge between these two perspectives, providing the technical guidance and political support necessary to make hard choices. By engaging with industry leaders, the agency ensures that CI Fortify is not just a government mandate but a collaborative strategy that reflects the actual challenges faced by those who manage the nation’s pipelines, ports, and power plants. This dialogue is essential for refining the technical requirements of the program to ensure they are both effective and achievable.
A Practical Strategy for Transitioning to Degraded-State Operations
Infrastructure operators can implement the CI Fortify framework by adopting an “assumed breach” mentality and restructuring their engineering processes for maximum autonomy. The first step involves auditing all third-party and vendor connections to determine which are essential for core operations and which can be severed during a crisis without causing an immediate shutdown. This audit often reveals a surprising number of “invisible” connections, such as remote diagnostics tools or automated billing feeds, that create unnecessary risks. Once these connections are mapped, organizations can begin the work of creating “break-glass” procedures that allow for the rapid, orderly disconnection of the OT environment from the outside world when threat levels rise.
Organizations should then develop and test manual transition plans, ensuring the workforce is trained to manage local controls when automated systems are unavailable. This involves updating standard operating procedures to include “analog” steps that may have been forgotten in the rush toward digitalization. For instance, a water treatment facility might need to ensure it has enough physical staff on-site to manually adjust chemical levels if the automated dosing system is taken offline. Finally, operators must work with security vendors to shift monitoring efforts toward identifying “pre-disruptive” indicators. Instead of focusing solely on routine data theft, security teams should look for unauthorized changes to firmware or the creation of new administrative accounts on sensitive controllers, transforming the infrastructure into a landscape that is both harder to hit and significantly faster to recover.
Ultimately, the success of these strategies provided a roadmap for a more stable and secure industrial base. The implementation of the CI Fortify framework encouraged a fundamental shift where resilience was no longer viewed as an optional upgrade but as a core requirement of modern engineering. Organizations realized that the ability to operate in a disconnected state was a competitive advantage, protecting not only the public interest but also the long-term viability of the businesses themselves. As these practices became standardized, the nation’s critical systems began to exhibit a new kind of durability, characterized by a reduced dependence on fragile digital chains and an increased reliance on local expertise and robust, independent architecture. The path forward required a commitment to constant vigilance, but the results ensured that the essential services of society remained protected against the unpredictable storms of the digital age.