Exploitation Techniques

Threats and Vulnerabilities
Enterprise AI GPUs vs. Consumer Gaming GPUs: A Comparative Analysis
While the price tag of a $30,000 data center processor might suggest unmatched speed across every possible computing task, the reality of modern silicon engineering tells a far more nuanced story of specialization.
Comparison Article Read More Threats and Vulnerabilities
Microsoft Patches 165 Flaws in Massive April Security Update
The sheer scale of the modern vulnerability landscape was recently put on full display as Microsoft deployed a monumental security update to address 165 new vulnerabilities.
Roundup Article Read More Cyberсrime and Cyber Warfare
ViperTunnel Python Backdoor – Review
The silent infiltration of corporate networks has reached a new level of sophistication as ViperTunnel demonstrates how a script-based backdoor can outmaneuver traditional perimeter defenses.
Technology Review Read More Cyberсrime and Cyber Warfare
How Does ViperTunnel Secure Persistent Corporate Access?
Modern enterprise security is currently facing a silent crisis as sophisticated interpreter-based backdoors begin to bypass traditional defensive perimeters with alarming regularity and precision.
Roundup Article Read More Threats and Vulnerabilities
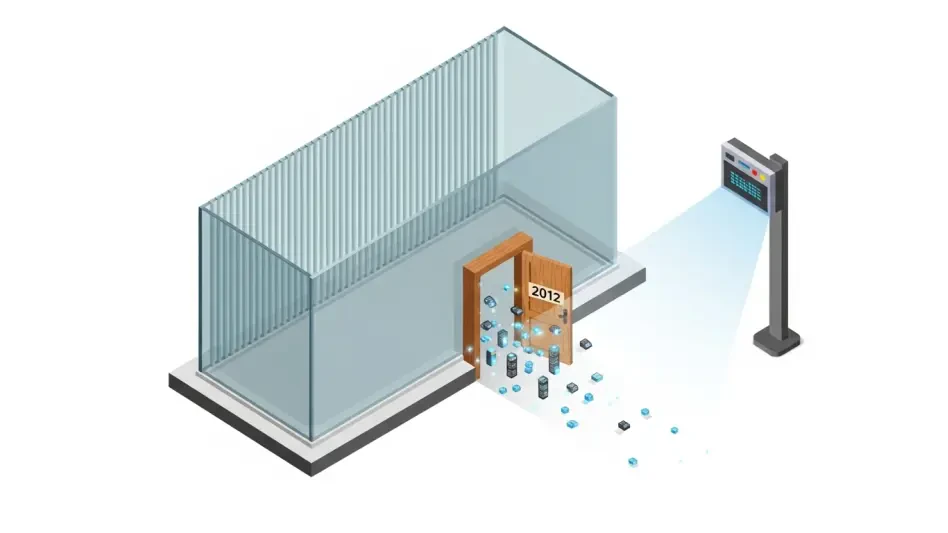
Why Are Ancient Security Flaws Still Fueling Ransomware?
The cybersecurity landscape is currently witnessing a paradoxical trend where the most sophisticated ransomware groups are not relying solely on cutting-edge exploits, but rather on "zombie" vulnerabilities that were patched years—sometimes over a de...
Timeline Article Read More Threats and Vulnerabilities
Will Project Glasswing Redefine Global Cybersecurity?
The announcement of Project Glasswing on April 10, 2026, by Anthropic signifies a fundamental shift in how the international community approaches the mounting pressure of digital warfare and infrastructure protection.
Read More Threats and Vulnerabilities
Is Our Critical Infrastructure Safe From Cyberattacks?
The silent hum of a power station or the rhythmic clatter of a freight train often masks a fragile digital reality where critical components remain tethered to an increasingly hostile public internet.
Trending
Read More Threats and Vulnerabilities
Trend Analysis: Building Management System Security
The modernization of smart buildings has reached a critical crossroads where operational convenience meets unprecedented digital risk, often leaving physical safety in the balance.
Trend Analysis Read More
Get our content freshly delivered to your inbox. Subscribe now ->
Receive the latest, most important information on cybersecurity.