The cybersecurity landscape is currently witnessing a paradoxical trend where the most sophisticated ransomware groups are not relying solely on cutting-edge exploits, but rather on “zombie” vulnerabilities that were patched years—sometimes over a decade—ago, yet remain active in the wild. The Cybersecurity and Infrastructure Security Agency recently underscored this crisis by updating its Known Exploited Vulnerabilities catalog, forcing a realization that the digital window of opportunity for attackers never truly closes as long as legacy code remains active. Understanding why these ancient bugs continue to fuel modern extortion campaigns is essential for shifting from a reactive to a proactive security posture. This timeline explores how decades-old mistakes continue to bypass modern defenses and why the “patch and forget” mentality is failing global infrastructure.
A Chronology of Persistent Threats and the Resurgence of Dead Bugs
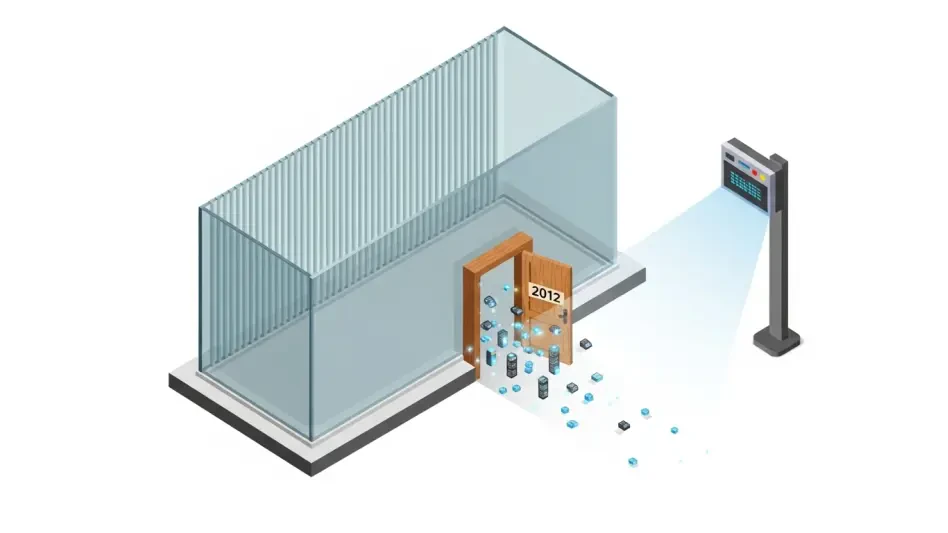
2012: The Origin of the Visual Basic Remote Code Execution Flaw
Long before the current ransomware boom, a critical vulnerability identified as CVE-2012-1854 was discovered within Microsoft Visual Basic for Applications. At the time, it represented a standard remote code execution risk, allowing attackers to take control of a system through compromised office documents. Although Microsoft released a patch fourteen years ago, the flaw never truly disappeared. Its recent reappearance in federal mandates highlights a disturbing reality: legacy software components often persist within modern enterprise environments, providing a “time travel” exploit path for attackers who know that internal systems frequently lack the same rigorous patching applied to external-facing servers.
2020: The Exploitation of Adobe Reader Use-After-Free Vulnerabilities
As the world shifted toward remote work, the reliance on digital documents increased, bringing older flaws like CVE-2020-9715 back into the spotlight. This specific “use-after-free” vulnerability in Adobe Acrobat and Reader allowed attackers to execute arbitrary code by manipulating how the software managed memory. While the security community moved on to newer threats, ransomware affiliates recognized that many organizations had stalled their update cycles during the chaos of the pandemic. This event marked a shift where attackers began systematically scanning for these specific, older memory corruption issues to gain a foothold in corporate networks.
2023: Microsoft Exchange and the Rise of Storm-1175
The narrative of ancient flaws evolved significantly with the discovery and subsequent exploitation of CVE-2023-21529 and CVE-2023-36424. These vulnerabilities in Microsoft Exchange Server and Windows components provided a potent combination for initial access and local privilege escalation. Specifically, the threat actor known as Storm-1175 began weaponizing these flaws to bypass security perimeters. By leveraging a known server-side vulnerability, the group demonstrated that even relatively recent “known” flaws can be just as devastating as zero-days if the window between disclosure and remediation is not aggressively managed. This period solidified the link between unpatched infrastructure and the deployment of the Medusa ransomware.
2024 and Beyond: The Zero-Day Transition and Remediation Mandates
The timeline reaches its peak with the emergence of CVE-2026-34621 and CVE-2025-60710, illustrating the overlap between long-exploited zero-days and the systemic failure to patch. CISA’s recent directive to remediate these flaws by April 2025 serves as a bookend to a decade of neglect. It confirms that the gap between a patch being available and a patch being applied is the primary breeding ground for ransomware. This era is defined not by the discovery of new bugs, but by the government-mandated cleanup of old ones, signaling that the industry is finally acknowledging that an unpatched bug from 2012 is just as dangerous as a fresh exploit discovered this morning.
Analyzing Turning Points and the Failure of Patch Management
The most significant turning point in this timeline is the realization that threat actors are economically motivated to use the path of least resistance. Rather than burning expensive, one-time-use zero-day exploits, ransomware groups are recycling “zombie” bugs because they are cost-effective and highly reliable against legacy systems. This pattern reveals a massive gap in visibility; many organizations are unaware that ancient libraries or sub-components, like those in Visual Basic, are still running deep within their tech stacks. The overarching theme is one of technical debt—where the speed of digital adoption has far outpaced the ability of IT departments to maintain basic hygiene. The shift from “novelty” to “utility” in exploit selection shows that as long as an entry point exists, its age is irrelevant to an extortionist.
Expert Perspectives on the Longevity of Software Exploits
Security experts argue that the persistence of these flaws is often due to the complexity of modern software dependencies. A vulnerability in a core component like Microsoft Exchange or Adobe Acrobat can have a “long tail” because these programs are often integrated into critical business workflows that administrators are afraid to disrupt with updates. Furthermore, regional differences in cybersecurity maturity mean that a flaw patched in North America might remain a viable target in other sectors for years, providing a global testing ground for ransomware affiliates. A common misconception is that a “critical” update loses its urgency over time. In reality, as the community of attackers shares scripts and automated scanning tools, the risk associated with an old, known flaw actually increases, making the remediation of historical vulnerabilities a foundational requirement for modern survival.
The industry shifted its focus toward automated asset discovery to identify hidden legacy components. Security teams implemented more aggressive internal scanning protocols to catch flaws that lingered beyond the network perimeter. Organizations prioritized technical debt reduction as a primary defensive strategy, moving away from the assumption that age equaled irrelevance. Future strategies focused on the “SBOM” or Software Bill of Materials to provide better visibility into embedded libraries. Experts suggested that further reading on the CISA KEV catalog and real-time threat intelligence feeds would be necessary for maintaining a hardened environment.