How Did UNC3886 Breach Singapore's Telecoms?
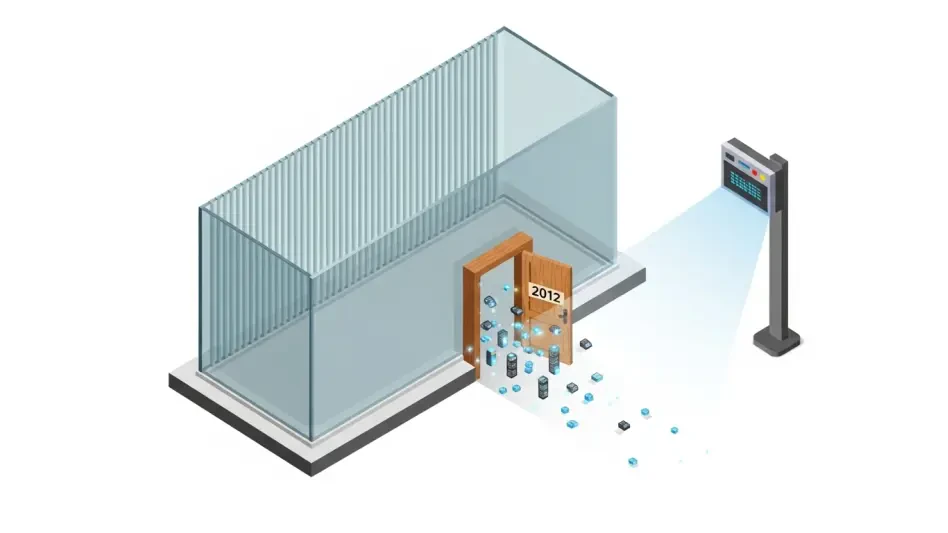
A highly sophisticated cyber espionage campaign, which remained undetected for nearly a full year, successfully infiltrated the core of Singapore's telecommunications sector by exploiting a series of previously unknown vulnerabilities in widely used...
Read More