The digital landscape has fundamentally transformed into a primary theater of international conflict where state-sponsored cyber operations now serve as a standard instrument of national power. On March 11, 2026, the vulnerability of this interconnected world became undeniably clear when a Michigan-based medical device manufacturer, Stryker Corp, suffered a massive disruption attributed to the Iranian-linked hacking collective known as Handala. This specific breach did not just target a private entity; it effectively paralyzed essential manufacturing and shipping operations, demonstrating that the front lines of modern warfare have moved from distant borders to domestic servers. The incident proves that traditional military maneuvers in the Middle East are now consistently paired with aggressive virtual strikes that can reach across oceans to impact local economies. Organizations that once viewed themselves as geographically isolated from geopolitical tensions are discovering that digital connectivity creates a direct path for foreign adversaries to exert influence and signal strategic intent.
Redefining the Scope of Modern National Infrastructure
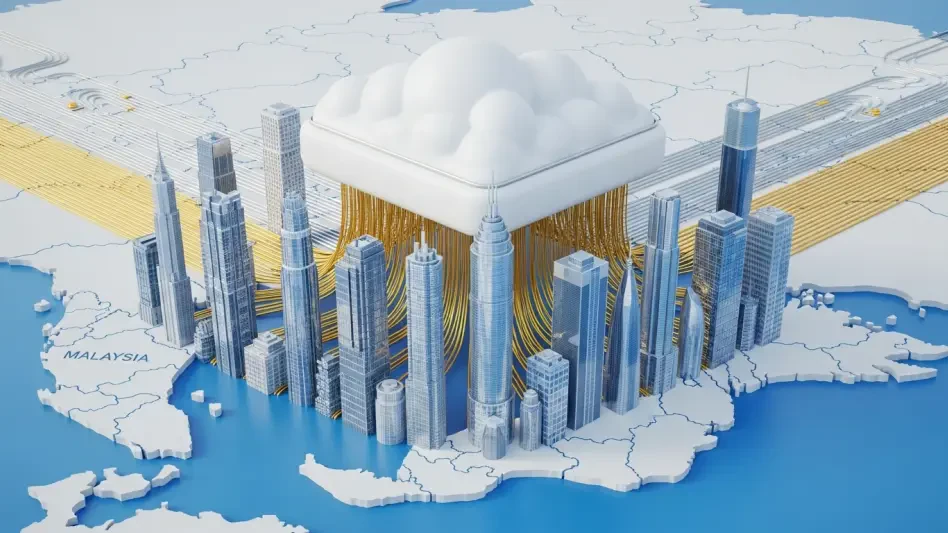
Modern critical infrastructure is no longer confined to the obvious targets that traditionally occupied the minds of national security experts, such as power grids or municipal water treatment facilities. The current definition has expanded significantly to include a vast, interconnected ecosystem composed of upstream suppliers, managed information technology service providers, and specialized parts manufacturers. When a niche supplier like a medical device firm is compromised, the ripple effects can jeopardize hospital operations and patient care across the entire country, effectively turning a private commercial entity into a critical national asset. This evolution has forced federal agencies to recognize that the security of a major utility is only as strong as the smallest vendor in its complex supply chain. Consequently, cybersecurity is no longer an isolated IT concern but a fundamental component of national stability that requires a broader perspective on what constitutes a vital target for foreign intelligence services.
In response to these systemic and pervasive risks, the Cybersecurity and Infrastructure Security Agency has actively championed a whole-of-society defensive posture through its high-profile Shields Up initiative. This strategic shift acknowledges a harsh reality where organizations that never considered themselves military targets are now stationed on the front lines of global friction between major world powers. By viewing the entire supply chain as an integral component of the nation’s critical infrastructure, the United States government aims to close the specific gaps that state-sponsored actors frequently exploit to bypass more hardened federal defenses. This approach necessitates a higher level of transparency and cooperation from private firms that handle sensitive data or manufacture essential components for larger systems. The goal is to ensure that a breach in one sector does not lead to a catastrophic failure across others, building a resilient network that can withstand the mounting pressure of state-led digital incursions.
The Strategic Logic of Long-Term Network Infiltration
A prevalent and dangerous misconception among many business leaders is that state-sponsored hacking aims primarily for immediate, catastrophic destruction or visible chaos within a network. However, the strategic logic governing Iranian cyber operations often prioritizes persistent access over overt disruption to maintain a position of long-term leverage against the West. By quietly infiltrating a corporate network and remaining undetected for months or even years, these actors can map internal dependencies and identify the most sensitive vulnerabilities within a specific industry. This dormant presence provides nation-states with a virtual master key that can be turned at a moment’s notice during a diplomatic crisis or a hot war to cause the maximum possible impact at the most opportune time. This shift toward long-term infiltration suggests that the true value of a successful hack is not the data stolen today, but the potential to paralyze an entire sector during a future period of heightened international tension.
To maintain this crucial leverage, attackers increasingly utilize sophisticated living-off-the-land techniques that involve using a system’s own legitimate administrative tools to perform malicious actions. This methodology allows Iranian-linked actors to blend in seamlessly with routine network traffic, making it exceptionally difficult for security teams to distinguish between a standard maintenance task and a foreign intrusion. By avoiding the use of custom malware that might trigger traditional antivirus signatures, these hackers can move laterally through a network with relative impunity while gathering intelligence or planting backdoors. The ultimate objective is to build an extensive library of strategic options, ensuring that they possess the capability to disrupt Western networks whenever it serves their broader political or military objectives. This tactical patience requires a corresponding shift in defense, focusing more on behavioral analysis and anomaly detection rather than simply relying on static blacklists of known threats.
The Anatomy of Modern Campaigns and Collaborative Security
Iranian-linked campaigns generally follow a standardized and repeatable four-stage sequence that allows them to scale their operations across a wide array of American industries simultaneously. The process begins with initial access gained through common but effective methods such as social engineering, phishing, or the exploitation of unpatched software vulnerabilities in remote-access systems. Once a foothold is established, the attackers transition to lateral movement and reconnaissance, identifying high-value data and mapping out the network’s architecture to understand its internal dependencies. The third stage involves the establishment of persistent backdoors to ensure that they are not easily evicted during routine security cleanups or system updates. Finally, the deployment of effects occurs, which can range from quiet intellectual property theft to the total destruction of hard drives, as seen in historical attacks against the global energy sector that resulted in massive operational outages and financial loss.
Because the vast majority of United States critical infrastructure is privately owned, the federal government cannot rely solely on top-down mandates for protection and must instead foster a collaborative ecosystem. Legislative frameworks such as the Cyber Incident Reporting for Critical Infrastructure Act of 2022 have become essential tools in this modern defense strategy by requiring companies to report significant breaches. These mandates ensure that the Joint Cyber Defense Collaborative can create an accurate, real-time battlefield map of ongoing threats, allowing the government to warn other potential targets before a campaign can spread. This level of information sharing is vital because it transforms individual corporate defenses into a unified national front against sophisticated state actors. By centralizing the collection of threat intelligence, federal agencies can identify patterns that would be invisible to a single organization, enabling a faster and more coordinated response to the evolving tactics used by foreign adversaries.
Strengthening Resilience Through Proactive Defense
The rising tide of Iranian cyber operations demonstrated that the protection of critical infrastructure required a paradigm shift toward active resilience and deeper public-private integration. Security experts recognized that the most effective response involved the immediate adoption of zero-trust architectures to limit the lateral movement of intruders once they breached a perimeter. Organizations across the healthcare and energy sectors prioritized the regular patching of legacy systems while increasing their investment in advanced threat-hunting capabilities to discover dormant threats before they were activated. The federal government successfully expanded the scope of reporting requirements, ensuring that even small-scale suppliers remained accountable for their security posture. These collective actions moved the defense beyond simple reaction, establishing a more robust framework that treated every network node as a potential point of conflict. By focusing on rapid information sharing and structural hardening, the nation established a deterrent against foreign interference in its domestic affairs.