The traditional image of a lone hacker spending months to penetrate a single corporate network has been shattered by a new reality where 600 firewalls across dozens of countries can be compromised in mere weeks. Recent investigations into a Russian-speaking threat actor revealed a massive, synchronized campaign that bypassed traditional software exploits entirely. By utilizing commercial generative AI, this individual orchestrated a global assault that demonstrated how technical sophistication is no longer a barrier to entry for large-scale disruption. This transition signals the arrival of an automated factory model in the world of cybercrime, where a single operator can achieve results once limited to nation-states.
The End of the Boutique Cyberattack
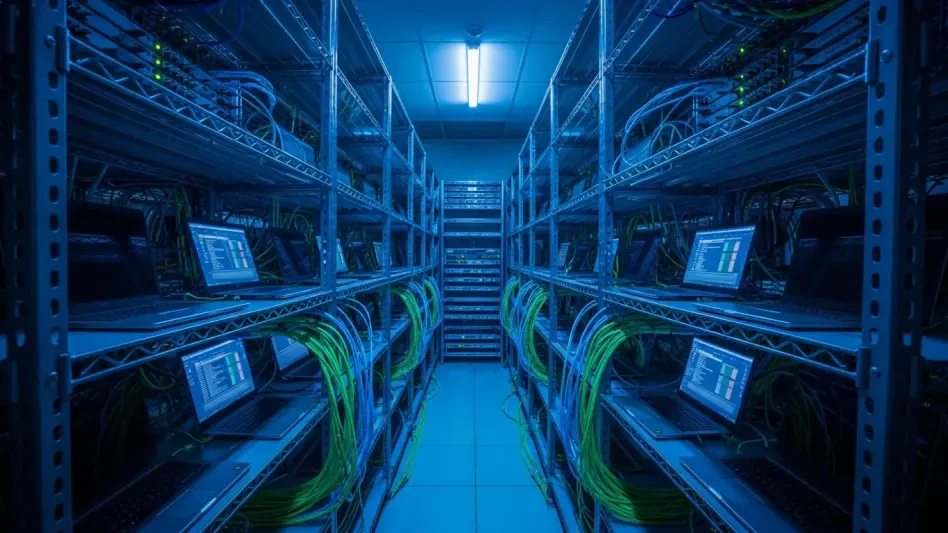
Cybersecurity has historically focused on a boutique model characterized by highly skilled individuals crafting unique tools for specific targets. However, the integration of Large Language Models has replaced this artisanal approach with a high-efficiency assembly line. Attackers no longer need to labor over a single breach for months; instead, they use AI to scan, target, and infiltrate hundreds of systems simultaneously.
This shift means that global disruption is now available for the price of a monthly subscription to a commercial AI service. The democratization of these tools allows even those with minimal coding knowledge to launch complex operations across different time zones. This accessibility has effectively ended the era of the lone wolf, ushering in a period where automated scripts handle the technical heavy lifting, allowing criminals to focus on scale rather than individual precision.
From Software Exploits to Scaled Human Error
While the industry often fixates on sophisticated zero-day vulnerabilities, the latest wave of attacks proves that fundamental security gaps remain the most profitable targets. Modern threats frequently ignore complex coding flaws in favor of exploiting basic human oversight, such as exposed management ports and the absence of multi-factor authentication. AI allows low-skilled actors to search for these “front doors” across the internet with industrial speed.
Rather than searching for a needle in a haystack, attackers now use AI to identify unpatched administrative interfaces at a volume that was previously impossible. The goal has shifted from finding a unique hole in a system to exploiting the universal failures in basic security hygiene that persist across global infrastructure. This methodology allows a single operator to brute-force credentials at a scale that overwhelms traditional defensive monitoring.
The Virtual Workforce: How GenAI Automates the Intrusion Lifecycle
The core of this new assembly line is the use of Large Language Models to act as a virtual security team for a single operator. A primary bottleneck in any cyberattack is the requirement for custom code to decrypt configuration files once initial access is gained. By leveraging AI to generate sophisticated Python and Go scripts, attackers move from infiltration to data extraction in a fraction of the time a human developer would require.
Furthermore, these AI-driven workflows allow for the management of simultaneous global intrusions. If an operator encounters a hard target with robust defenses, the AI allows them to instantly pivot to softer targets without losing operational momentum. This parallel processing capability ensures that the attack remains profitable and efficient, regardless of the defensive posture of any single organization.
Expert Perspectives on the AI-Driven Turning Point
Security leaders emphasize that we have reached a critical inflection point where commercial AI has permanently lowered the barrier to entry for cybercrime. Experts like C.J. Moses and Damon Small note that these tools provide a workforce that handles the most technical execution phases. This development transforms a solo criminal into a project manager overseeing an automated fleet of digital intruders.
Jacob Krell of Suzu Labs points out that while the methods—such as brute-forcing—are not new, the speed and volume provided by AI are unprecedented. This convergence suggests a systemic failure of perimeter security, as multiple threat actors are now seen targeting the same infrastructure through different paths. The challenge is no longer just the tools themselves, but the industrial efficiency with which they are applied to old vulnerabilities.
Securing the Perimeter Against Automated Threats
To defend against this automated assembly line, organizations returned to rigorous security hygiene that eliminated the low-hanging fruit AI relied upon. Enforcing non-negotiable multi-factor authentication served as the most effective shield against credential-based attacks. By removing the possibility of single-factor access, a primary point of entry for AI-driven scripts was effectively sealed.
Hardening administrative access and management ports was prioritized, as internet-accessible interfaces remained the easiest targets for discovery scripts. Organizations audited their infrastructure, ensuring no management ports were exposed to the public. Finally, transitioning to identity-centric defense models became essential to restrict lateral movement. These proactive measures ensured that even if a script gained entry, its ability to cause widespread damage was strictly limited.