The days of unpredictable ransomware spikes have surrendered to a more calculated and terrifyingly consistent operational baseline that defines the current digital economy. This shift represents a transition from a volatile era of sporadic digital extortion to a sustained “new normal” where the frequency of attacks remains perpetually high. Organizations can no longer view these events as anomalous storms to be weathered; instead, the data from the first quarter of 2026 suggests that the current level of threat activity is the permanent floor for global cyber risk. Establishing an understanding of this baseline is critical for any entity seeking to align its defensive investments with the reality of a professionalized criminal marketplace.
This stabilization of the modern threat landscape requires a fundamental realignment of how risk is perceived at the board level. The current trends indicate that while the volume of attacks may have plateaued, the internal mechanics of the cybercrime ecosystem are more dynamic than ever. This report examines the critical shifts occurring in geographical targeting, the emergence of sector-specific strategies, and the evolution of criminal tactics that now include the direct exploitation of artificial intelligence. By dissecting these developments, leadership teams can move beyond reactionary measures and toward a state of strategic resilience.
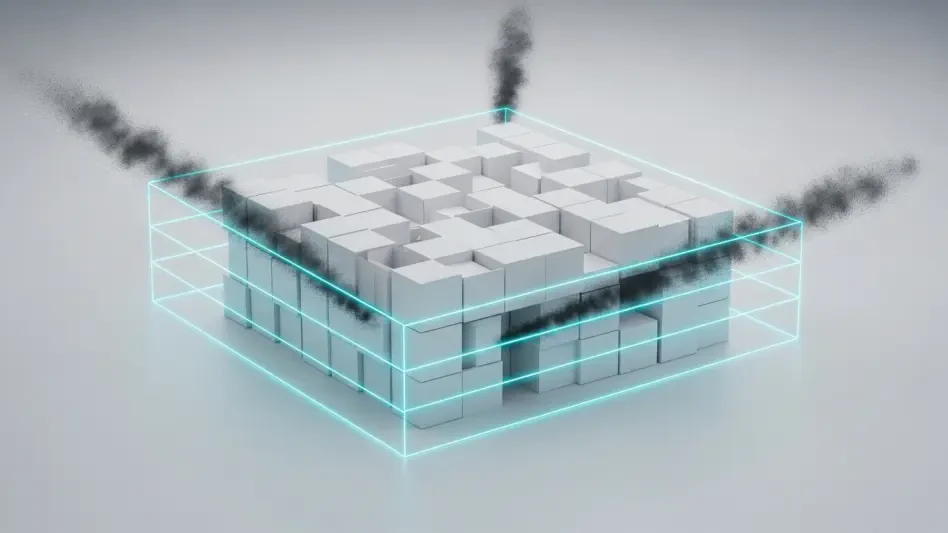
The Stabilization of the Modern Threat Landscape
The transition of ransomware activity into a sustained operational baseline marks the maturity of the “ransomware-as-a-service” business model. In previous years, the cybercrime market was characterized by dramatic surges followed by periods of relative quiet as groups reorganized or faced law enforcement pressure. However, the data from the start of 2026 reveals a market that has found its equilibrium, with attack volumes holding steady at levels that were once considered unprecedented. This plateauing effect suggests that the infrastructure of digital extortion is now robust enough to absorb individual group failures without a significant drop in total global activity.
Understanding these specific trends is vital for aligning global cybersecurity risk expectations because it removes the false hope of a return to a lower-threat environment. The consistency of attack volumes demonstrates that the supply side of the cybercrime economy—including initial access brokers, malware developers, and money launderers—has become fully institutionalized. Consequently, the threat is no longer a series of isolated incidents but a continuous pressure on the global supply chain. This reality necessitates a shift in defensive philosophy from “if an attack occurs” to “how often the organization must repel an attack.”
The key areas of concern in this new environment involve geographical shifts and the targeting of previously overlooked sectors. While the United States remains the primary focus of these groups, there is a visible expansion into emerging markets where digital transformation has outpaced the adoption of security protocols. Furthermore, the rise of AI-based risks introduces a layer of complexity that traditional malware detection often fails to address. These evolving tactics signify that while the total volume of attacks is stable, the methods used to achieve success are in a constant state of sophisticated flux.
Why Adapting to the New Baseline Is Essential
A plateau in attack volume often masks a more dangerous internal churn within the cybercrime ecosystem, where groups reorganize under new banners to evade scrutiny. When the market appears stable, it is usually because the “business as usual” of cybercrime has reached a state of maximum efficiency. This saturation indicates that threat actors have identified the most profitable paths and are now refining their execution. For a modern enterprise, failing to recognize this stability as a high-risk environment is a strategic error that invites catastrophe through complacency.
The benefits of proactive adaptation to this baseline include significantly reduced operational downtime and the preservation of brand reputation. Organizations that accept the high-frequency nature of the current threat landscape are more likely to invest in the redundancy and isolation required to survive a breach. Moreover, such adaptation results in significant cost savings over the long term, as the price of a comprehensive defensive posture is invariably lower than the combined cost of ransom payments, legal fees, and lost customer trust. Moving from a mindset of crisis management to one of strategic resilience is the only way to navigate a market defined by persistent aggression.
Recognizing that the ransomware market has reached “market saturation” allows organizations to allocate their resources more effectively. Instead of chasing every new threat variant, they can focus on the core vulnerabilities that fuel the entire ecosystem. This strategic pivot ensures that security teams are not constantly operating in a state of exhaustion, which is exactly what threat actors hope to exploit. By building defenses around the reality of a persistent threat, an organization ensures that its growth is not undermined by the inevitable attempts of consolidated groups to extract its value.
Actionable Defense Strategies for a High-Volume Risk Environment
Implementing a defensive strategy in the current climate requires a focus on the methodologies that are proving most effective for modern threat actors. Best practices are no longer about general security awareness but about the precise application of technical controls that disrupt the criminal supply chain. Based on the intelligence gathered throughout the early months of 2026, the focus must be on neutralizing the most common entry points and data exfiltration techniques used by established and emerging ransomware syndicates.
Practical implementation of these strategies involves a multi-layered approach that prioritizes visibility across the entire network. Organizations must move toward a model of continuous verification, where every user and device is treated as a potential vector for a breach. By focusing on the specific tactics utilized by groups like Qilin or the rapidly ascending Gentlemen, defenders can build specialized blocks that are more effective than generic security software. These strategies are designed to counter the sophistication of an economy that has moved past simple file locking into the realm of complex data extortion.
Strengthening Perimeter Defense and Vulnerability Management
Aggressive patching of perimeter infrastructure remains the most effective deterrent against the current wave of ransomware operations. Many of the most active groups in 2026 rely heavily on known vulnerabilities in virtual private networks and firewalls to gain their initial foothold. When an organization fails to update these critical gateways within hours of a patch release, they essentially leave the front door unlocked for automated scanning tools used by initial access brokers. Enforcing robust Multi-Factor Authentication (MFA) across all remote access points is the second half of this defensive equation, as it mitigates the risk posed by stolen credentials.
The dynamic nature of this threat is perfectly illustrated by the fluctuating activity of established groups based on the availability of exploits. For example, the decline of the Akira group earlier this year was directly tied to the exhaustion of unpatched SonicWall vulnerabilities that had previously fueled their operations. Once the global inventory of vulnerable systems was reduced through mass patching and the replacement of aging hardware, their ability to execute high-volume attacks diminished. This demonstrates that collective defensive action can effectively force even the most prominent groups into a period of reorganization or decline.
In contrast, the persistence of groups like NightSpire shows the danger of localized negligence in vulnerability management. While other groups struggled, NightSpire thrived by identifying and targeting unpatched FortiOS systems that organizations had failed to secure. Their success was not due to a new or revolutionary technology, but rather a disciplined focus on a specific, unaddressed weakness in the common enterprise perimeter. This contrast serves as a vital lesson for security leaders: the global “average” of security does not matter if your specific infrastructure remains behind the curve of available updates.
Addressing the Shift Toward Extortion-Only Models
A significant tactical shift has occurred where threat actors are increasingly abandoning encryption in favor of extortion-only models. This approach focuses entirely on the theft of sensitive data and the subsequent threat of public disclosure to force payment. To counter this, organizations must implement data-centric security measures that prioritize the monitoring of data exfiltration rather than just the integrity of files. Encryption of data at rest is no longer a sufficient defense if an attacker can gain access to the keys or view the data through a compromised administrative account.
The effectiveness of this model is particularly visible in the Construction industry, which saw a 44% year-over-year increase in attacks. This sector was targeted not because its files were easy to encrypt, but because its data—including proprietary blueprints, project timelines, and bid information—is incredibly time-sensitive and valuable. Attackers realized that they did not need to lock a construction company out of its systems to cause catastrophic damage; they only needed to threaten the release of confidential project data to competitors or regulatory bodies. This pivot demonstrates that any sector handling sensitive information is now a high-priority target for non-encryption-based attacks.
To mitigate this risk, security teams should deploy advanced monitoring tools that can detect unusual patterns of data movement within the network. Large-scale data transfers to unknown external IP addresses should trigger an immediate, automated response that isolates the affected systems. Furthermore, implementing granular access controls ensures that even if one account is compromised, the attacker cannot easily access the entire repository of the organization’s most sensitive assets. This shift from protecting the perimeter to protecting the data itself is the hallmark of a modern, resilient defense strategy.
Securing the Emerging AI Agent Supply Chain
The integration of agentic AI into enterprise workflows has created a new and poorly understood attack surface that is already being exploited. Securing the AI supply chain requires a security-first architecture that focuses on granular access controls for AI agents and the rigorous scanning of all third-party extensions or “skills.” Because AI agents often require high-level permissions to be useful, a single malicious instruction can lead to widespread system compromise. Organizations must treat AI integrations with the same level of scrutiny as they would a new third-party software vendor or a direct network connection.
The OpenClaw Marketplace breach served as a wake-up call for the industry regarding the vulnerability of agentic AI platforms. In this instance, attackers bypassed traditional malware detection by using instruction-based payloads rather than malicious code. These payloads were hidden within seemingly helpful AI “skills” that users downloaded to enhance their productivity. Once active, the instructions directed the AI agent to steal credentials and establish a persistent backdoor for the attackers. This event marked the first large-scale supply chain attack of its kind and proved that traditional security tools are currently ill-equipped to handle the nuances of AI-based threats.
To combat these risks, enterprises must establish a “walled garden” approach for their AI deployments. This involves creating isolated environments where AI agents can operate without direct access to the core network or sensitive databases unless explicitly authorized. Additionally, every instruction or skill added to an AI system should undergo a mandatory security review to check for hidden commands or suspicious logic. As AI becomes more central to business operations, the ability to secure these instruction-based systems will become a defining factor in an organization’s overall cyber resilience.
Strategic Outlook and Final Recommendations
The maturity of the ransomware economy suggests that the current high-volume environment will remain stable through the remainder of the year. There was a clear indication that threat actors have entered a phase of professionalization where they prioritize consistent results over flashy, disruptive events. The anticipated “summer slowdown” appeared to be a result of this professionalization, as criminal groups synchronized their operational cycles with the global business calendar. This predictability did not mean a decrease in danger, but rather a shift toward a more methodical and persistent threat that required a equally methodical defensive response.
Organizations operating in the United States and emerging markets like Thailand had to prioritize their defensive investments based on the specific tactics of the groups targeting them. In the US, the focus was on protecting large, complex attack surfaces from consolidation-minded groups like the Scattered LAPSUS$ Hunters. Meanwhile, in Thailand, the priority was on hardening infrastructure that had undergone rapid digitization without a corresponding increase in security maturity. The most successful organizations were those that realized their defensive posture had to be as tailored and sophisticated as the groups attempting to breach them.
In the final analysis, the necessity for evolving defensive strategies became undeniable as the lines between different cybercrime entities continued to blur. The transition toward extortion-only models and the exploitation of AI supply chains proved that the ransomware economy was capable of rapid innovation even within a stable volume of attacks. The organizations that thrived were those that viewed cybersecurity not as a project with a completion date, but as a continuous operational requirement. They understood that in a world where the threat has reached a new normal, only those who treated security as a core business function could truly protect their future.