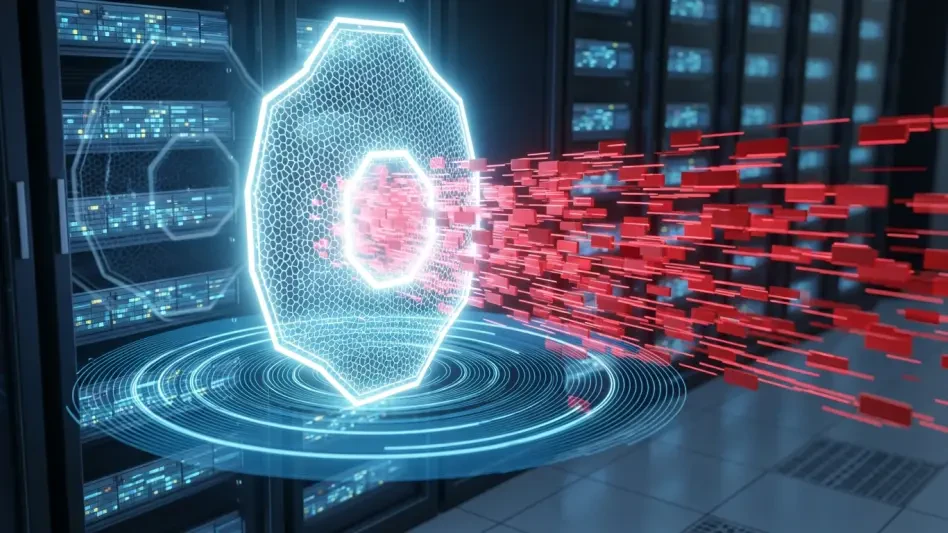
Is Basic Cyber Hygiene the Key to Stopping Salt Typhoon?
The persistent infiltration of American telecommunications infrastructure by the state-sponsored actor known as Salt Typhoon has exposed a staggering level of vulnerability within the digital backbone of the nation.