Threats and Vulnerabilities

Threats and Vulnerabilities
Nozomi and Dragos: ZionSiphon Is Not a Functional OT Threat
Headlines raced ahead of reality as ZionSiphon was cast as plant-breaking malware long before seasoned OT engineers could show that it lacked the tools, the maps, and the physics to touch a single pump.
Feature Article Read More Threats and Vulnerabilities
Tropic Trooper Abuses Trusted Tools to Target Chinese Users
Security teams kept staring at clean logs while an unseen hand rode trusted apps straight through the front door, hiding in plain sight behind PDFs, GitHub traffic, and developer tunnels.
FAQ Read More Threats and Vulnerabilities
Fast16, a Pre-Stuxnet Lua Tool to Corrupt Calculations
Meticulous sabotage that concealed itself behind ordinary outputs rather than smoke and sparks challenged the assumption that cyberattacks must announce their presence, and its tradecraft foreshadowed a strategy built on quiet, cumulative harm rather...
Read More Threats and Vulnerabilities
Litecoin 13-Block Reorg Exposes MWEB Patch Gap and DoS
Thirteen blocks vanished and then reappeared on Litecoin as an orchestrated strike blended a Mimblewimble Extension Block consensus flaw with denial-of-service pressure on mining pools, forcing the network to unwind roughly half an hour of activity a...
Read More Threats and Vulnerabilities
Fortreum Acquires Kovr.ai to Unite AI Compliance and Audits
Compliance deadlines rarely slip, but budgets and engineering focus often do, and that mismatch has turned security certifications into a costly choke point just as agencies demand faster, safer software delivery. Fortreum’s purchase of Kovr.
Read More Threats and Vulnerabilities
Did Patch Gaps Enable Litecoin’s 13-Block MWEB Reorg?
Thirteen blocks vanished and reappeared on Litecoin late Friday into Saturday, compressing about thirty-two minutes of activity into a terse reminder that patch cadence and communication can shape the blast radius of faults as much as code itself.
Read More Threats and Vulnerabilities
TeamPCP Abuses Dependabot to Breach CI, Steal GitHub Secrets
A single bot click rippled across thousands of pipelines when a trusted update path quietly swapped security for speed, and the breach that followed revealed how CI now decides who holds the keys to modern software.
Industry Report Read More Threats and Vulnerabilities
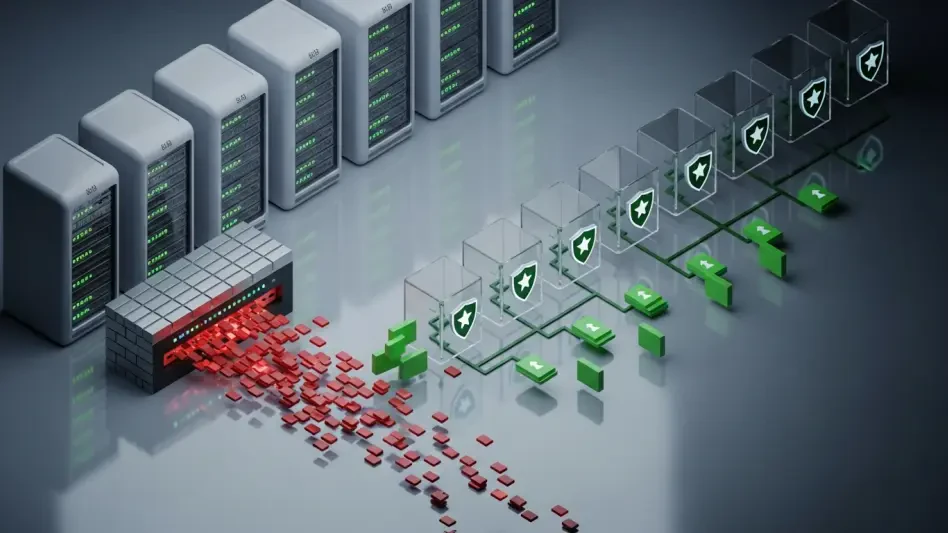
Can Defenders Outpace China's Covert SOHO Botnets?
Household routers and office gadgets now quietly double as stepping stones for state-backed hackers, turning familiar networks into cover for espionage at a scale few organizations are prepared to confront.
FAQ Read More
Get our content freshly delivered to your inbox. Subscribe now ->
Receive the latest, most important information on cybersecurity.