The sophisticated breach of a supposedly air-gapped system remains one of the most chilling prospects for security administrators who believe their servers are safe simply because they are offline. Operation TrueChaos turned this confidence into a liability by proving that physical isolation is no match for a compromised trust chain. By transforming a routine software update into a digital Trojan horse, threat actors demonstrated that the most dangerous vulnerabilities are often the ones organizations intentionally invite past their firewalls.
The Illusion of the Air-Gapped Fortress
When a network is disconnected from the public internet, administrators often operate under a false sense of absolute security. This psychological safety net frequently leads to a relaxation of internal monitoring, as the “perimeter” is assumed to be impenetrable. Operation TrueChaos exploited this specific mindset by targeting the very tools designed to keep communication private, proving that a lack of external connectivity does not equate to immunity from sophisticated exploitation.
Why the TrueConf Vulnerability Redefined Insider Threats
Security-conscious organizations, including defense departments and government agencies in Southeast Asia, rely on TrueConf precisely because it functions on private LANs. This architecture keeps sensitive data away from global web traffic, yet this niche appeal created a high-concentration target for nation-state actors. The significance of this operation lies in the realization that “on-premises” does not inherently mean “secure” if the software internal verification logic is flawed.
Deconstructing the Anatomy of Operation TrueChaos
The infiltration was a multi-stage execution that prioritized stealth and the exploitation of administrative trust. By focusing on the internal update mechanism, the attackers ensured that their presence remained invisible to standard external defense layers.
The Zero-Day Gateway: CVE-2026-3502
The attack centered on a critical flaw in how the TrueConf client handled software updates. The system failed to verify the integrity or digital signatures of update packages fetched from the local server. This lack of authentication meant the client would blindly execute any file provided by the centralized on-premises server, assuming it was a legitimate patch from a trusted source.
Compromising the Internal Command Center
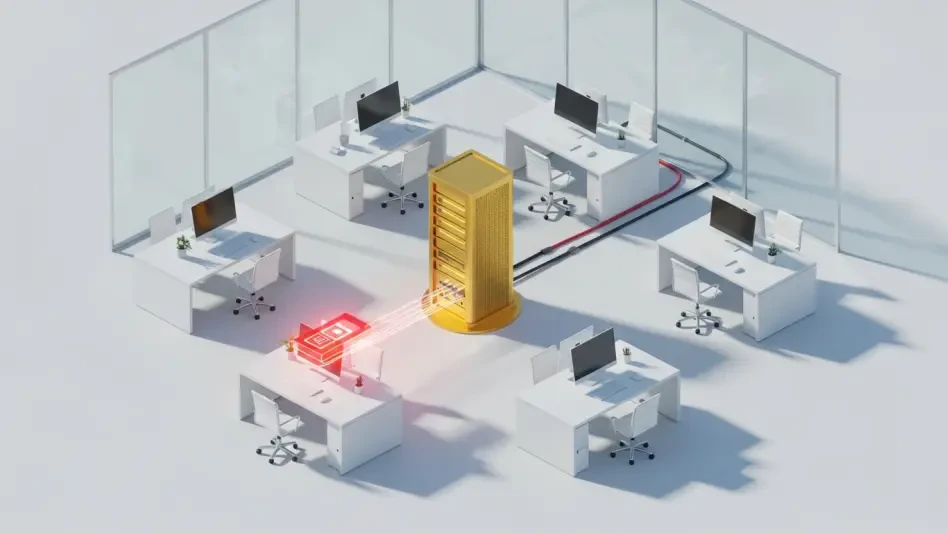
Before the end-users were affected, the suspected China-nexus actors had to gain control of the internal TrueConf servers. Once they established a foothold within the server environment, they replaced legitimate update binaries with weaponized payloads. This turned the server—the very heart of the secure communication network—into a distribution hub for malware that was distributed automatically to every connected workstation.
Bypassing Perimeter Defenses Through Trusted Channels
Because the malicious payload originated from an internal, trusted server, it bypassed traditional security layers like phishing filters and external firewalls. Users received a standard update prompt from an application they used daily. Upon clicking “install,” they unwittingly deployed the Havoc post-exploitation framework, granting the attackers deep access to their systems for reconnaissance and long-term persistence without triggering an alarm.
Expert Perspectives on the Evolution of Supply Chain Attacks
Cybersecurity researchers at Check Point highlight that Operation TrueChaos represents a shift in strategy for sophisticated threat actors. Rather than hammering at the digital front door, they are increasingly targeting the software supply chain from the inside out. Experts noted that the use of the Havoc framework allowed attackers to blend in with common red-team activities, making attribution and detection significantly more difficult for internal security teams.
Defensive Frameworks for Isolated Environments
Protecting a secure network required moving beyond the “perimeter” mindset and adopting a policy of continuous verification. Security teams had to accept that internal traffic is not inherently benign.
Immediate Remediation and Patch Management
The most critical step was the immediate transition to TrueConf Windows client version 8.5.3 or later. This version introduced the necessary integrity checks that were missing in previous iterations. Organizations learned to treat internal software updates with the same level of scrutiny as external downloads, ensuring that no executable runs without a verified cryptographic signature in the future.
Auditing and Behavioral Monitoring
Organizations conducted deep-dive audits of their internal update logs to identify historical anomalies or unauthorized file replacements. Furthermore, monitoring for unusual lateral movement or communication patterns helped detect post-exploitation frameworks like Havoc. Implementing a “Zero Trust” architecture within the local network ensured that even if one server was compromised, the damage remained contained and visible to administrators.