Configuration Security

Threats and Vulnerabilities
Manufacturing’s Ransomware Surge, Fueled by MFA Failures
Factories humming at full tilt, tied to global schedules and razor-thin margins, now face criminals who stopwatch downtime as leverage, turning every remote connection, legacy controller, and rushed change freeze into a bet the business cannot afford...
Industry Report Read More Threats and Vulnerabilities
Can Critical Infrastructure Shoot Down Rogue Drones Safely?
A surge of rogue quadcopters over substations is forcing security budgets to pivot from fences to firmware and training.
Market Analysis Read More Threats and Vulnerabilities
Are Sleeper VS Code Extensions the Next Supply-Chain Risk?
Subtle tremors across everyday coding sessions concealed a methodical shift in extension supply chains that let a single install seed multi‑stage malware, siphon credentials, and quietly reuse compromised accounts to publish look‑alikes before defend...
Timeline Article Read More Threats and Vulnerabilities
How Did Public PoCs Supercharge Defender EoP Exploits?
Headlines moved fast because code moved faster, and the gap between a public proof-of-concept and real-world abuse closed to a matter of days as Microsoft Defender’s CVE-2026-33825 turned a niche research find into a widely attempted elevation-of-pri...
Read More Threats and Vulnerabilities
Nozomi and Dragos: ZionSiphon Is Not a Functional OT Threat
Headlines raced ahead of reality as ZionSiphon was cast as plant-breaking malware long before seasoned OT engineers could show that it lacked the tools, the maps, and the physics to touch a single pump.
Feature Article Read More Human Factors in CyberSecurity
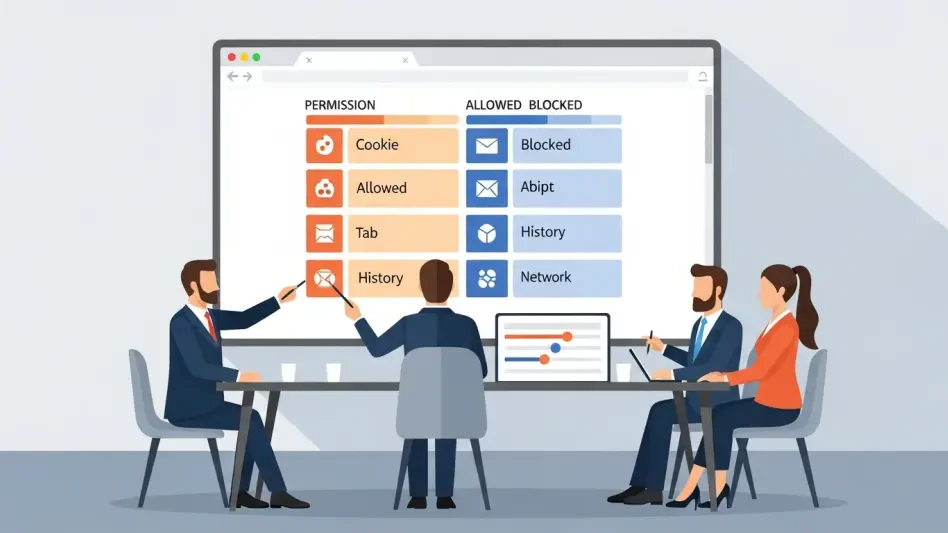
Are Your Browser Extensions Selling Your Data by Design?
The small conveniences added to browsers—faster video controls, cleaner pages, one-click productivity boosts—increasingly came with a price tag that looked nothing like a subscription, because it charged in behavioral traces, browsing patterns, and i...
Trending
Read More Incident Response and Forensics
Could BlackFile’s IT-Support Vishing Hit Your Execs Next?
A stranger on the phone sounds like IT, knows an executive’s nickname, and asks for a quick SSO reset that unlocks the whole cloud, turning a friendly favor into an entry point for theft, coercion, and seven‑figure demands.
Research Summary Read More Threats and Vulnerabilities
Tropic Trooper Abuses Trusted Tools to Target Chinese Users
Security teams kept staring at clean logs while an unseen hand rode trusted apps straight through the front door, hiding in plain sight behind PDFs, GitHub traffic, and developer tunnels.
FAQ Read More
Get our content freshly delivered to your inbox. Subscribe now ->
Receive the latest, most important information on cybersecurity.