Hospitals kept humming, devices kept delivering therapy, and yet a silent trespass into Medtronic’s corporate systems redrew the map of what a “contained” breach really means. The company confirmed unauthorized access in parts of corporate IT, while emphasizing that products, patient safety, manufacturing, distribution, and customer connections stayed online.
That contrast—access without disruption—challenged a familiar yardstick. If care delivery is unaffected, is the crisis over, or is the real risk only beginning to surface?
Why This Story Mattered Now
Healthcare has become a premium target where critical infrastructure meets sensitive data and sprawling vendor ecosystems. Even with strong budgets, persistent gaps remain, making entry and quiet data collection more achievable than many assume.
This incident landed amid heightened geopolitical tension and a run of supplier-focused attacks. A group calling itself Handala claimed responsibility, the same name linked to the Stryker breach on March 11 that caused service disruptions, underscoring a trend: suppliers occupy a pressure point for the entire sector.
Inside the Breach, Beyond the Headlines
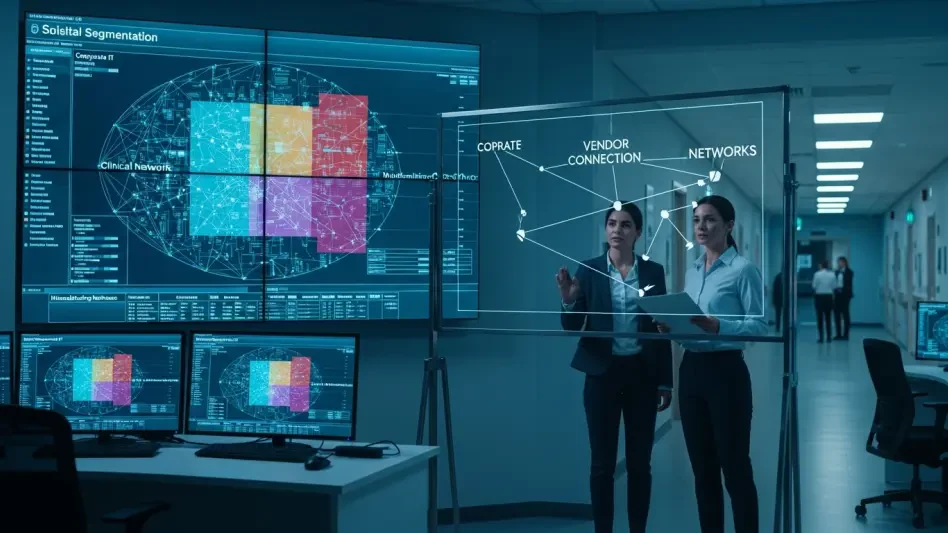
Medtronic described strict segmentation between corporate IT and its product and manufacturing networks, and stressed that hospital customer networks are managed by provider IT teams. That separation likely limited the blast radius, keeping life-critical services steady while the company investigated what data was accessed.
However, corporate IT often houses sensitive business intelligence: supplier contracts, R&D roadmaps, identity stores, and support records. Access there can fuel long-game extortion, targeted phishing, or competitive insight theft without tripping alarms that would shut down care.
What Experts Saw in the Attack Surface
“Entry and data access themselves are the signal,” said Amir Khayat of Vorlon. “Healthcare remains attractive because it is critical infrastructure with sprawling vendors, sensitive data, and lingering gaps. Focusing only on downtime misses the point.” His view reframed the episode as a sector mirror, not a one-off headline.
Agnidipta Sarkar of ColorTokens urged readiness for complexity and uncertainty: “Prioritize microsegmentation—preferably agentless—and tie it to EDR so policy follows identity and behavior.” In practice, that meant carving clear zones for corporate IT, clinical networks, and manufacturing, while using identity- and application-aware rules to break attack paths.
Where Defenders Went Next
The playbook that emerged depended on governance and telemetry as much as firewalls. Least privilege for admins and vendors, just-in-time access, and enforced MFA cut access sprawl; EDR/XDR linked to network controls helped contain lateral movement before it touched high-value systems like EHRs, device management platforms, or identity providers.
Supply-chain controls rose in urgency. Organizations tiered third parties by risk, mandated logging and segmentation, limited vendor paths, and set auto-expiring credentials. Teams practiced data-exposure tabletop drills, prebuilt decision trees for notification and regulators, and tracked metrics such as dwell time for lateral movement and segmentation coverage, validating controls through red teaming and attack-path modeling.
The Bottom Line
The Medtronic breach had reinforced a hard lesson: operational resilience did not cancel information risk, and supplier targeting had shifted the pressure to where healthcare could least afford complacency. The next move for defenders had been clear—treat corporate IT as a sensitive zone, invest in agentless microsegmentation tied to detection, tighten vendor access, and rehearse crisis playbooks for data exposure—because attackers already behaved as if the perimeter were gone.