Cyberсrime and Cyber Warfare

Cyberсrime and Cyber Warfare
How Is Iranian Cyber Warfare Reshaping Global Security?
The rapid transformation of Iranian cyber operations from localized digital disruptions into a cohesive instrument of global power projection has fundamentally altered the calculus of modern international security.
Industry ReportTrending
Read More Cyberсrime and Cyber Warfare
Iranian State Actors Target Stryker in Major Cyberattack
The vulnerability of the global healthcare supply chain became painfully evident this week as Stryker, a titan in the medical technology sector, grappled with a sophisticated cyberattack that disrupted critical life-saving operations across several c...
Read More Cyberсrime and Cyber Warfare
Is the Stryker Hack a New Era of Global Cyber Warfare?
The sudden, synchronized failure of thousands of medical workstations across several continents signals a profound shift in how modern geopolitical conflicts penetrate the corporate digital fabric.
Feature Article Read More Cyberсrime and Cyber Warfare
Is the Global Fight Against Commercial Spyware Faltering?
The global market for high-end digital surveillance has reached a volatile equilibrium where state-sanctioned crackdowns and lucrative private acquisitions are simultaneously reshaping the industry's future.
Market Analysis Read More Cyberсrime and Cyber Warfare
Is Your Business Prepared for a Total Digital Wipeout?
The flickering glow of a single smartphone screen became the only source of light for thousands of employees as their workstations simultaneously dissolved into blackness during a coordinated digital execution.
Feature Article Read More Cyberсrime and Cyber Warfare
Operation Lightning Dismantles Massive SocksEscort Botnet
Digital invisibility has long served as the primary currency for cybercriminals who exploit residential connections to mask their malicious footprints from the watchful eyes of global security agencies.
Research Summary Read More Cyberсrime and Cyber Warfare
Ransomware Negotiator Charged in $75 Million Double-Agent Scheme
The federal prosecution of Angelo John Martino III has sent shockwaves through the cybersecurity industry, uncovering a sophisticated double-agent operation that redefined corporate betrayal by targeting the very victims he was paid to protect.
Read More Cyberсrime and Cyber Warfare
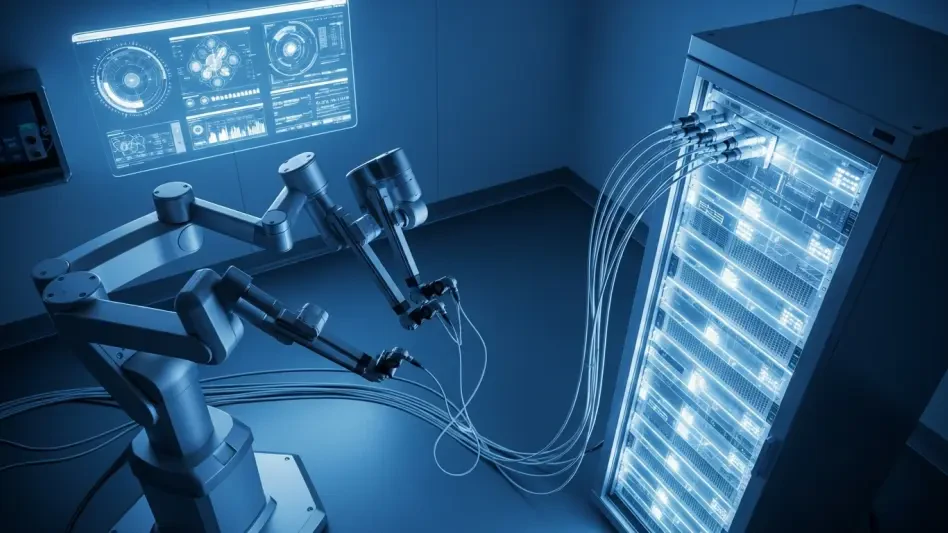
Medical Technology Cybersecurity – Review
The systematic dismantling of a global medical giant’s digital footprint within hours has redefined the stakes of digital safety in the healthcare sector.
Technology Review Read More
Get our content freshly delivered to your inbox. Subscribe now ->
Receive the latest, most important information on cybersecurity.