Cyberсrime and Cyber Warfare

Cyberсrime and Cyber Warfare
Should Schools Pay Ransoms After the Canvas Data Breach?
The digital silence of a typical Monday morning was shattered when thousands of students and educators logged into Canvas only to find their learning dashboards replaced by chilling ultimatums from the notorious hacking collective known as ShinyHunte...
Feature Article Read More Cyberсrime and Cyber Warfare
Poisoned VS Code Extension Leads to Major GitHub Breach
The seamless integration of third-party tools within the modern software development lifecycle has created a double-edged sword for productivity and security.
Timeline Article Read More Cyberсrime and Cyber Warfare
AI Fuels the Rise of Zero-Day Hacks and Spyware
The seamless integration of high-performance large language models into the offensive workflows of modern cyberthreat actors has permanently altered the economics of vulnerability discovery and exploitation.
Read More Cyberсrime and Cyber Warfare
AI-Driven Cyber Warfare Reshapes National Security in 2026
The silent clicking of millions of automated processors across the globe now signals a more profound shift in international power dynamics than the movement of any conventional naval fleet or infantry division.
Read More Cyberсrime and Cyber Warfare
Grafana Labs Refuses Ransom Following Source Code Theft
When a sophisticated digital adversary manages to infiltrate the private inner sanctum of a major technology firm's repository, the ripple effects are felt across the entire global software supply chain.
Feature Article Read More Cyberсrime and Cyber Warfare
How Is Microsoft Fighting Upstream Cybercrime Services?
The digital world operates on an invisible foundation of trust that ensures the software people download is authentic, safe, and free from tampering by malicious actors.
Read More Cyberсrime and Cyber Warfare
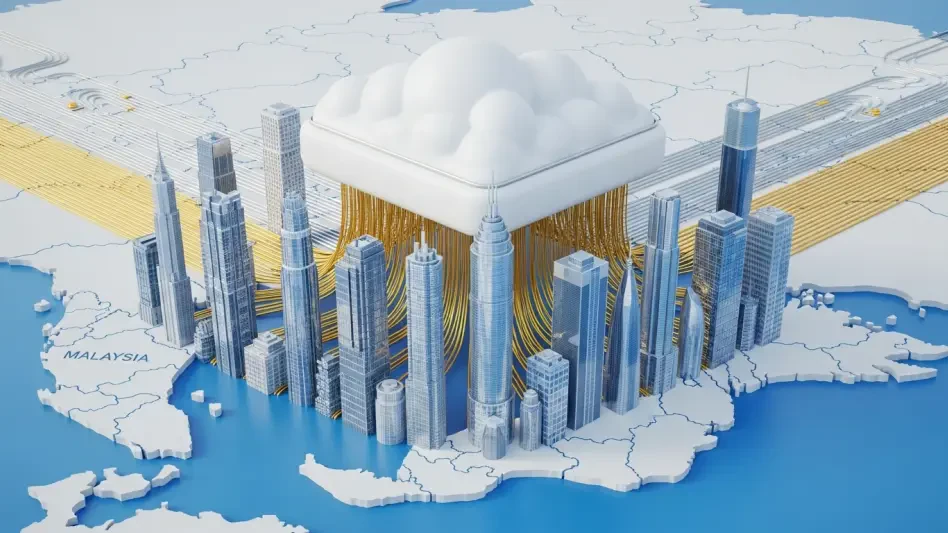
How Is Malaysia-Linked Espionage Hiding in the Cloud?
In the contemporary landscape of digital warfare, sophisticated state-sponsored threat actors are increasingly abandoning traditional server farms in favor of highly resilient cloud-based architectures that effectively blend malicious traffic with th...
Read More Cyberсrime and Cyber Warfare
Crete Police Dismantle Major Land Theft and Fraud Ring
The peaceful agricultural landscape of Crete has been shaken by the exposure of a sophisticated criminal network that utilized systematic violence and psychological warfare to dominate rural farming communities through illicit land acquisition and te...
Read More
Get our content freshly delivered to your inbox. Subscribe now ->
Receive the latest, most important information on cybersecurity.