Cyberсrime and Cyber Warfare

Cyberсrime and Cyber Warfare
Is Russia’s Hybrid War Undermining CEE Democracies?
RelentlessinformationpressurehasbecomethenormacrossCentralandEasternEuropeasKremlin-linkednetworksbraiddisinformation,covertinfluence,andcyberattacksintocampaignsdesignedtonudgeelections,polarizepublics,andpitregionalgovernmentsagainstNATOandtheEU.
Read More Cyberсrime and Cyber Warfare
Malaysia Leads ASEAN to Secure the New Telecom Frontline
Rising intrusions into telecom networks, mobile devices, and messaging layers have turned everyday communications into a live battlespace where metadata, routing, and user behavior yield strategic advantage faster than any breached inbox could.
Read More Cyberсrime and Cyber Warfare
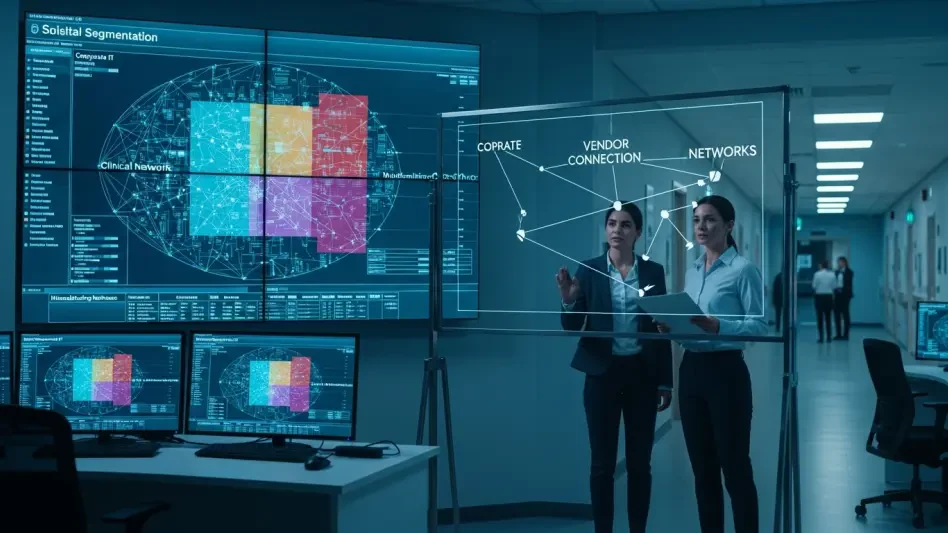
What Does the Medtronic Hack Reveal About Health Cyber Risk?
Hospitals kept humming, devices kept delivering therapy, and yet a silent trespass into Medtronic’s corporate systems redrew the map of what a “contained” breach really means.
Feature Article Read More Cyberсrime and Cyber Warfare
U.S. Sanctions Cambodian Senator in SE Asia Scam Crackdown
A sprawling online grift that siphoned nearly $21 billion from Americans in 2025 collided with reports of forced labor in Myanmar and Cambodia, turning a crime problem into a human-rights and national security fight overnight. The result was a U.S.
Roundup Article Read More Cyberсrime and Cyber Warfare
From Checklists to Control: Cyber Sovereignty in OT
A routine vendor patch that fanned out across turbines, substations, and treatment plants before sunrise forced a sharper question than any audit checklist ever had the nerve to ask: who truly owns the off switch when code crosses borders and remote...
Feature ArticleTrending
Read More Cyberсrime and Cyber Warfare
How Did Indonesia's Police Dismantle a Global Phishing Hub?
Phishingoperationsonceburrowedintotinycornersofthewebbutretooledintocommercialserviceswithbrandedstores, scripted toolkits, and instant bots that promised plug‑and‑play access to stolen credentials for a paying crowd.
Read More Cyberсrime and Cyber Warfare
Inside the Zero-Day Economy: From State Secrets to Crimeware
A quiet marketplace now sets the tempo of digital conflict by turning obscure software flaws into time-sensitive leverage, where a single zero-click iPhone chain can fetch millions precisely because it offers covert access before a patch closes the d...
Trending
Read More Cyberсrime and Cyber Warfare
Why Is Pay2Key Shifting From Profit to Pure Disruption?
A sudden silence often follows a digital breach, but when a United States healthcare provider recently found its entire network frozen with no demand for data, the quiet signaled a fundamental shift in the cybercrime landscape.
Feature Article Read More
Get our content freshly delivered to your inbox. Subscribe now ->
Receive the latest, most important information on cybersecurity.