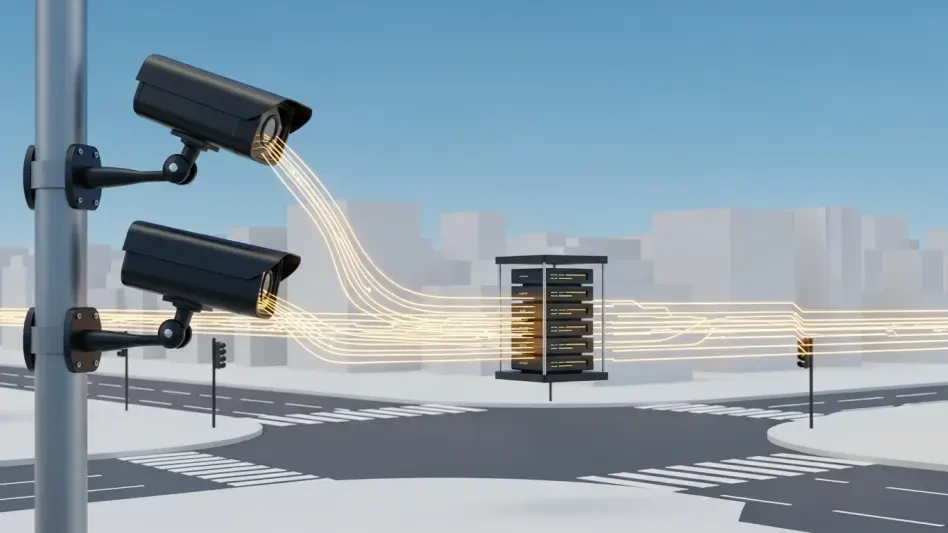
The digital eyes staring down from the dusty brickwork of Tehran’s administrative district were never meant to protect the men who authorized their installation. In a profound historical irony, the massive network of high-definition cameras and sensors deployed to suppress internal dissent and enforce ideological purity became the very instrument of the regime’s greatest existential threat. For years, the Iranian state invested billions in sophisticated monitoring technology to ensure that no citizen could move without being tracked, yet this obsession with total visibility inadvertently offered a clear, unblocked view to the intelligence agencies of its most formidable adversary. The infrastructure of oppression was repurposed into a sophisticated targeting system, proving that in the digital age, a ruler’s most powerful shield can easily be sharpened into a lethal sword by those with the technical prowess to seize its controls.
The Irony of Total Visibility: How Tehran’s Security Net Became a Death Trap
The very cameras installed to crush domestic dissent in Iran have become the eyes of its greatest adversary. In a stunning reversal of roles, the massive surveillance apparatus designed to monitor every street corner in Tehran served as the primary intelligence source for the operation targeting Supreme Leader Ayatollah Ali Khamenei. This intersection of digital espionage and kinetic warfare marks a pivotal moment in history where a regime’s tools of internal control were successfully repurposed into instruments of its own decapitation. The irony is palpable: the leadership in Tehran, seeking to eliminate any blind spots where a revolutionary thought might take root, created a world where they themselves had nowhere to hide. Every lens focused on a public square or a government corridor became a permanent, high-fidelity window for foreign analysts.
To maintain power and enforce strict social codes, the Iranian government flooded its urban centers with tens of thousands of internet-connected cameras. While these devices were effective at identifying women without hijabs or tracking the organizers of student protests, they also broadcasted the movements of the state’s inner circle in real time. Intelligence agencies did not need to place physical spies on every corner when the Iranian government had already done the work for them. By compromising the central nodes of this network, adversaries were able to watch the guardians of the revolution with the same granular detail that those guardians used to watch the public. This transformation from a domestic security net to an external death trap illustrates the inherent danger of centralized surveillance in an era of borderless cyber capabilities.
The Despot’s DilemmWhy High-Tech Control Creates Strategic Fragility
For authoritarian regimes, the pursuit of absolute domestic security often births a catastrophic external vulnerability. To maintain power and enforce strict social codes—such as the mandatory hijab laws—Iran flooded its cities with tens of thousands of internet-connected cameras. However, this “security” infrastructure created a digital roadmap for foreign intelligence agencies. As global security shifts toward the integration of AI and the Internet of Things (IoT), the more a state monitors its own citizens, the more visible its leadership becomes to those seeking to eliminate them from afar. This “despot’s dilemma” forces a choice between controlling the populace and protecting the state from sophisticated digital incursions. When everything is connected to facilitate control, everything becomes a potential entry point for a hostile actor.
The reliance on high-tech surveillance systems creates a centralized point of failure that is often overlooked in the rush to modernize. In a democratic society, decentralized systems and privacy protections provide a natural buffer against mass data exfiltration. In contrast, an authoritarian state demands that all data flow toward a central authority, making that single stream an incredibly valuable target for foreign espionage. As Iran attempted to build a “smart” security state, it inadvertently built a fragile one. The vast amount of data generated by millions of sensors across Tehran provided more than just faces and license plates; it provided the metadata of the regime’s daily operations. This digital footprint revealed the invisible rhythms of the state, turning the government’s strength into a glaring strategic weakness.
Inside the Operation: Mapping the Digital Infiltration of Iranian State Security
The reported tracking of the Supreme Leader on February 28 was not a fluke, but the result of a meticulously executed long-term infiltration. For years, Israeli intelligence maintained deep access to Tehran’s municipal camera feeds, rerouting data to external servers without alerting the local administrators. This persistent network compromise allowed analysts to observe the city’s security protocols as they evolved, identifying the lag times in response and the specific blind spots that were manually ignored by local operators. The infiltration was so deep that the hackers were essentially “ghost users” on the Iranian state security network, watching the watchers and learning the nuances of their digital habits. This level of access transformed a static map of the city into a living, breathing theater of intelligence.
Tactical camera positioning played a crucial role in the specific operation targeting the leadership. Specific hacked cameras near the leadership compound provided a bird’s-eye view of high-ranking officials and their protection details. By analyzing months of movement data, intelligence officers identified the specific habits and routes used by the regime’s inner circle. They noticed which vehicles were used for decoys and which ones actually carried high-value targets. The power of AI confirmation finally allowed for real-time facial recognition, identifying Khamenei’s presence with a high degree of certainty and providing the definitive green light for the strike. Advanced algorithms processed the video feeds to filter out the noise of the city, focusing exclusively on the specific signatures of the Supreme Leader’s motorcade and personal security detail.
Expert Perspectives on the Evolution of Kinetic Cyberwarfare
Intelligence officials and cybersecurity experts, including Bruce Schneier, highlight that we have entered an era where “more eyes” do not equate to “more safety.” Experts note that AI has removed the barrier of human error, allowing for “keyword searches” within live video feeds to find targets instantly. This means that a person’s face effectively becomes a searchable term across a city-wide database. When a target enters the field of vision of any compromised camera, the system triggers an automatic alert, eliminating the need for thousands of analysts to watch monitors around the clock. This automation has accelerated the kill chain from hours or days to mere seconds, making the environment for high-level officials increasingly hostile.
This phenomenon of camera hijacking is mirrored in other global conflicts, suggesting a broader trend in the evolution of modern warfare. From Hamas monitoring Israeli patrols on October 7 to Russian hackers targeting Ukrainian infrastructure, the battle for control over local video feeds has become a standard tactical objective. The psychological impact of exposure cannot be overstated; Iranian officials have publicly admitted that their every movement is tracked, creating a sense of total vulnerability within their own borders. This realization erodes the confidence of the ruling class, as they must assume that their most private discussions and movements are being broadcasted to their enemies. This state of constant visibility creates a paralyzing effect on leadership, as the very tools they use to project power are the ones that remind them of their own mortality.
Securing the Lens: Identifying and Mitigating Infrastructure Vulnerabilities
The ease with which surveillance systems are compromised suggests a systemic failure in how modern security hardware is deployed and maintained. Hardening hardware standards is the first step toward reclaiming some semblance of security. This involves moving beyond “plug-and-play” devices by enforcing mandatory password changes and frequent firmware updates to close the backdoors that are often left open by manufacturers. Many of the cameras used in the Iranian network were found to have default administrative credentials that were never changed, allowing even moderately skilled hackers to gain entry. Furthermore, the lack of end-to-end encryption meant that once the network was breached, the data was easily intercepted and understood by the intruders.
Reducing reliance on pirated software is another critical factor in securing national infrastructure. Sanctioned nations often use unauthorized software that is impossible to patch, making it “fish in a barrel” for sophisticated hackers. Without regular security updates from the original developers, these systems remain vulnerable to exploits that have been long since fixed in the rest of the world. Additionally, the myth of the “air-gap” must be dispelled; recognizing that even disconnected networks are vulnerable to physical breaches or internal turncoats who can provide credentials is vital. Ultimately, governments must weigh the benefits of domestic monitoring against the risk of creating a 24/7 intelligence stream for adversaries. The more comprehensive the surveillance of the citizenry, the more comprehensive the intelligence gathered by those who wish to destabilize the state.
The rapid weaponization of domestic security infrastructure forced a radical reassessment of how modern states balanced control with survival. It became clear that the pursuit of a transparent society for the purpose of policing created a transparent leadership for the purpose of assassination. The technological advancements that allowed for the tracking of individuals through vast urban landscapes eventually demanded a price that the Iranian regime was unprepared to pay. As security experts looked toward the future of urban defense, they realized that the era of the all-seeing state had reached its logical and dangerous conclusion. The digital footprints left by the powerful were no less visible than those of the common citizen, and in the high-stakes game of international espionage, those footprints led directly to the doorstep of the most guarded compounds.
Security analysts proposed a shift toward “data minimalism,” arguing that the collection of excessive information was a strategic liability rather than an asset. They recommended that vital infrastructure be decentralized and that the use of biometric tracking be limited to highly secured zones rather than being blanketed over entire cities. This approach aimed to reduce the “attack surface” available to foreign hackers and restore a level of operational security that had been lost in the rush toward total digital awareness. The global community watched as the very concept of a “smart city” was re-evaluated, not just as a tool for efficiency or control, but as a potential Trojan horse for kinetic conflict. The lesson was learned through a series of high-stakes breaches that redefined the boundaries between cyber defense and physical protection.
Ultimately, the events surrounding the infiltration of Iran’s surveillance network served as a sobering reminder that technology is neutral, but its application is not. The tools built to ensure the permanence of a regime were the same tools that accelerated its vulnerability. Moving forward, the focus shifted toward building resilient, opaque systems that prioritized the protection of information over the collection of it. This paradigm shift was not just a technical necessity but a survival strategy for a world where the lens of a camera could be as deadly as a guided missile. The once-celebrated visibility of the modern state was replaced by a renewed respect for the shadows, as leaders everywhere realized that being seen was the first step toward being eliminated.