The sophisticated nature of modern cyber-espionage often relies on the clever exploitation of legitimate services that security teams trust implicitly to facilitate daily business operations. A specialized threat actor identified as UNC2814 has demonstrated this by transforming standard productivity tools into clandestine communication channels for state-sponsored surveillance activities. For nearly a decade, this group remained largely undetected by hiding its malicious traffic within the mundane data flows of cloud-based spreadsheets. By mimicking ordinary user behavior, the attackers managed to infiltrate critical infrastructure and government agencies across multiple continents. This case illustrates a growing trend where adversaries prioritize stealth and persistence over immediate disruption, using the very tools designed for collaboration to undermine global security. The discovery of this operation serves as a stark reminder that the boundaries between benign business applications and malicious infrastructure are increasingly blurred in the current landscape. Security researchers have noted that the prolific nature of this group stems from its ability to adapt to changing defense mechanisms while maintaining a low profile. By integrating their operations into the fabric of daily digital life, these actors have set a new standard for persistence.
Anatomy of a Cloud-Based Breach
The Hidden Logic: How GridTide Operates
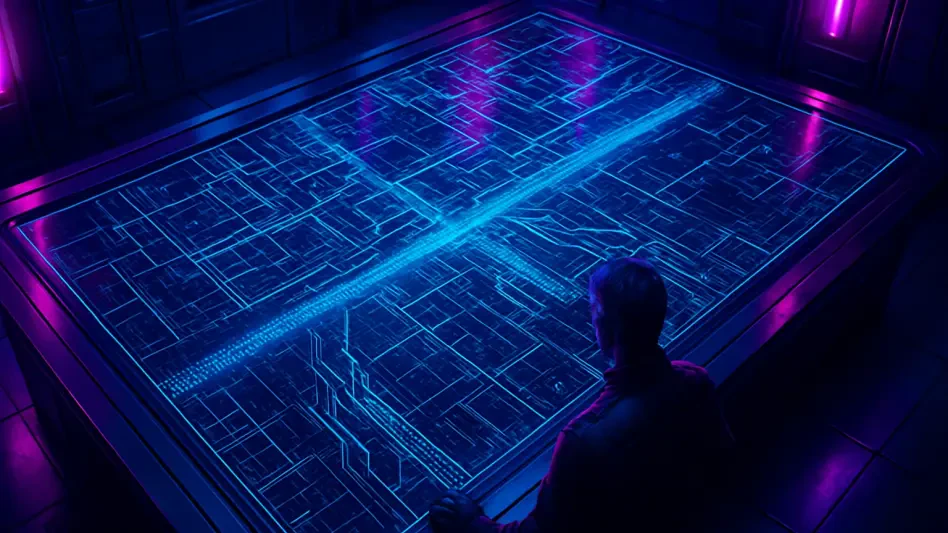
The primary tool utilized by UNC2814 was a sophisticated custom backdoor known as GridTide, which provided the threat actors with a versatile platform for deep system access. This malware was engineered to execute arbitrary shell commands and facilitate seamless file transfers between compromised hosts and the command-and-control infrastructure. What distinguished GridTide from traditional malware was its reliance on Google Sheets as the primary medium for data exchange. Instead of connecting to a suspicious external domain, the malware communicated with legitimate Google Cloud API endpoints to receive instructions and exfiltrate stolen data. This method allowed the group to bypass traditional signature-based detection systems and network firewalls that typically permit traffic to reputable cloud services. By treating a spreadsheet as a dynamic command console, the attackers could update their tactics in real-time while remaining hidden within the noise of standard enterprise traffic patterns. The use of raw data streams within these documents meant that even if a security administrator opened the file, the contents would appear as incomprehensible gibberish rather than obvious malicious code. This layer of obfuscation proved highly effective at maintaining long-term access to compromised systems.
Stealth through Legitimacy: Bypassing Network Defenses
Security professionals often struggle to identify threats that utilize trusted software-as-a-service platforms because the associated traffic appears identical to authorized administrative activity. UNC2814 capitalized on this inherent trust by routing their malicious data through standard API calls, effectively making their espionage efforts indistinguishable from routine data entry or synchronization tasks. This strategy of living off the cloud is particularly effective against organizations that rely heavily on integrated productivity suites for their core functions. The group’s ability to maintain persistence for several years without detection highlights the limitations of perimeter-centric security models that focus on blocking known bad IP addresses. Because the communication was directed toward a globally recognized and trusted service, internal monitoring tools rarely flagged the activity as anomalous. This innovative approach to command-and-control infrastructure represents a significant evolution in the tactical playbook of state-sponsored cyber actors. Furthermore, the reliance on legitimate APIs means that simple blocking is not an option, as it would disrupt essential business workflows. This forced a more nuanced response from defenders, who had to look deep into the metadata of these connections to find evidence of unauthorized behavior or data movement.
Strategic Implications and Remediation
Surveillance Objectives: Monitoring High-Value Targets
The scope of the UNC2814 campaign was expansive, affecting at least 53 confirmed victims across more than 40 different nations, with potential activity extending into dozens of other regions. The group primarily targeted telecommunications providers and government institutions, suggesting a strategic focus on long-term surveillance and intelligence gathering rather than immediate financial gain. By gaining a foothold within telecom networks, the attackers were able to monitor sensitive communications, including call data records and unencrypted SMS messages of specific individuals. These persons of interest often included activists, political dissidents, and foreign diplomats whose data could provide significant geopolitical leverage. While the exact entry point into these networks varied, evidence points toward the exploitation of vulnerable web servers and edge devices as the most likely path for initial compromise. This methodical targeting of critical communication hubs underscores the group’s commitment to maintaining a wide-reaching and influential monitoring network. The intelligence gathered was likely used to track movements and suppress opposition in various jurisdictions. This highlights how cyber tools are being utilized as an extension of state power to control information and monitor potential threats to political stability on a global scale.
Defensive Response: Disruption and Future Resilience
The resolution of this threat required a coordinated intervention that involved the systematic dismantling of the group’s digital assets and the revocation of their access to cloud-based resources. Security analysts identified the specific Google Cloud projects used for the operation and terminated them, effectively severing the link between the GridTide malware and its operators. This action disrupted the current espionage cycle, but the high level of sophistication observed suggested that similar actors would eventually adapt their techniques to utilize other legitimate services. Organizations were encouraged to implement more granular monitoring of API traffic and adopt zero-trust architectures that scrutinized all internal and external data flows regardless of the service’s reputation. Enhancing the visibility into encrypted traffic and monitoring for unusual patterns in cloud service usage became essential steps for preventing future recurrences of such stealthy intrusions. The collaboration between technology providers and international security agencies established a blueprint for addressing the persistent challenge of state-sponsored activity. Moving forward, the industry prioritized the development of behavioral analytics that could distinguish between human interaction with cloud tools and automated malware communication. These advancements aimed to close the gap that allowed UNC2814 to operate in the shadows for so long.