Security landscapes often shift when the very tools designed to protect sensitive communications are transformed into vehicles for state-sponsored digital espionage. Operation TrueChaos represents a sophisticated cyber-espionage campaign identified in early 2026 that specifically targeted high-value government entities across Southeast Asia. The operation is defined by its exploitation of a critical zero-day vulnerability, tracked as CVE-2026-3502, within the TrueConf video conferencing client. With a CVSS score of 7.8, this flaw highlights a significant breakdown in the trust-based relationship between enterprise servers and their connected endpoints, allowing for the widespread distribution of malware. The significance of this threat lies in its subversion of a “trusted update” mechanism, effectively turning a legitimate productivity tool into a delivery vector. By compromising a central server, attackers were able to push malicious payloads to all users within a network. Security researchers have linked this operation with moderate confidence to Chinese-nexus threat actors, who utilized the initial access to deploy advanced post-exploitation frameworks for long-term reconnaissance and persistence within sensitive governmental systems.
Understanding the Zero-Day Flaw
The Mechanics: CVE-2026-3502 and Update Validation
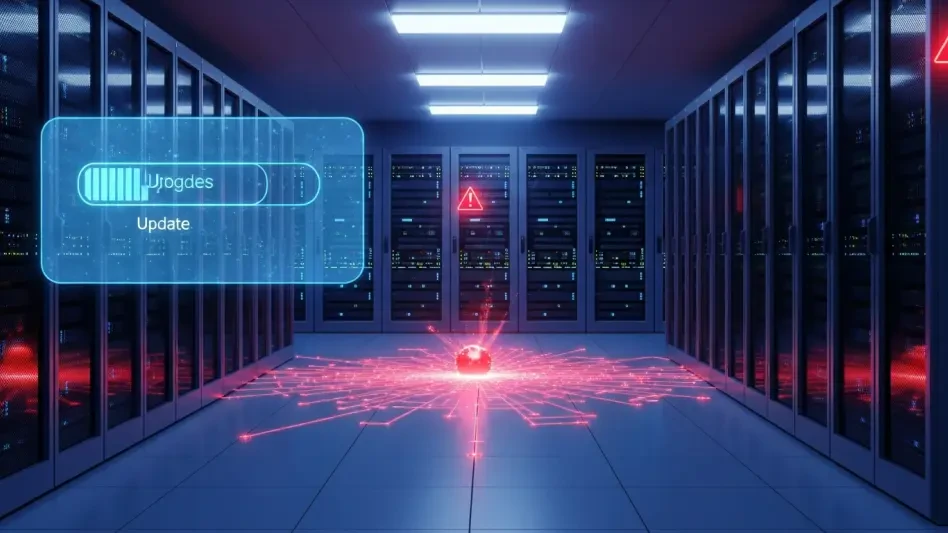
The core of the TrueChaos operation involves a total lack of integrity and authenticity checks during the TrueConf client-side update process. In a typical enterprise environment, the TrueConf client connects to an on-premises server to compare software versions and ensure all participants are on the same build for compatibility. If the server indicates a newer version is available, the client automatically prompts the user to download an executable from a specific internal directory. Because the software fails to verify digital signatures or cryptographic hashes of the incoming file, the client treats the server as an infallible source of truth. This architectural oversight creates a situation where the software trusts the source of the file based solely on its network origin rather than the content of the file itself. Consequently, any file placed in the expected directory on the server is treated as a legitimate update, regardless of whether it was actually authored by the software vendor or a malicious actor who has gained unauthorized access to the server infrastructure.
This lack of validation creates a “blind trust” scenario that is particularly dangerous in highly secured or air-gapped environments. When an attacker gains administrative control over the TrueConf server, they can replace legitimate update files with weaponized versions without triggering any internal security warnings from the application. When a user accepts the routine update prompt, they unwittingly execute arbitrary code with the same privileges as the application itself. This exploit is particularly effective because it leverages the user’s existing habits of maintaining software hygiene. In government and military sectors that rely on TrueConf for its ability to operate in air-gapped, on-premises environments, this vulnerability is devastating. These sectors often prioritize on-premises solutions specifically to avoid the risks of cloud-based data leaks, yet the very architecture meant to ensure data privacy serves as the catalyst for a deep-seated compromise that traditional perimeter security measures are not equipped to detect or prevent.
Impact on Secure Enterprise Architectures
Beyond the immediate technical failure, CVE-2026-3502 exposes a broader systemic vulnerability in how private networks handle localized software distribution. In many high-security configurations, the assumption is that if a server is physically or logically located within the organization’s firewall, its outputs are inherently safe. This “inside-out” trust model is what the TrueChaos actors exploited to such great effect. By focusing on a niche but critical communication tool, the attackers bypassed the scrutiny typically applied to more common applications like web browsers or office suites. This strategy allowed the malware to propagate through internal update channels that are often exempt from heavy-duty inspection by endpoint detection and response (EDR) tools, as these tools are frequently configured to trust administrative software updates to prevent operational disruptions. The result is a highly efficient infection vector that requires zero interaction with the public internet at the moment of compromise, making it an ideal choice for targeting isolated networks.
The exploitation of this flaw also highlights the limitations of traditional patch management in the face of compromised local infrastructure. Even if an organization has a policy of only installing verified software, the TrueConf client’s automated check-and-prompt mechanism circumvents these manual reviews. The malicious payload is delivered under the guise of the application’s own update routine, which many users are trained to click through without second thought. This psychological and technical alignment makes the vulnerability a potent weapon for persistent threat actors who aim to infiltrate and remain within a network for extended periods. As organizations increasingly move toward on-premises solutions to reclaim control over their data, they must also grapple with the reality that being “offline” or “private” does not equate to being secure if the internal update mechanisms remain as fragile and unverified as the one identified in this campaign.
Strategic Targeting and Execution
Strategic Value: Why TrueConf Became the Target
TrueConf is a prime target for state-sponsored espionage due to its popularity among organizations that avoid cloud-based solutions like Microsoft Teams or Zoom for sensitive discussions. While it maintains a global presence, its heavy use in Russia and East Asia makes it a high-value gateway for adversaries looking to infiltrate secure or remote environments. By compromising the central server of such a tool, a threat actor gains a foothold in infrastructure that is often insulated from the public internet, providing a rare bridge into supposedly “secure” zones. The platform is specifically marketed to organizations that cannot rely on cloud services due to strict regulatory requirements, making it an attractive target for those seeking high-value intelligence. For a state-sponsored actor, the ability to turn a secure communication hub into a listening post is the ultimate strategic advantage, as it places the adversary directly in the middle of the victim’s most confidential digital exchanges and operational planning sessions.
The lifecycle of Operation TrueChaos followed a precise, multi-stage attack chain designed to maintain a low profile and avoid the “noisy” signatures of less sophisticated campaigns. After gaining control of a government-managed server through separate, initial entry methods, the attackers replaced the legitimate update package with a malicious one built using Inno Setup. This custom-built “update” was designed to perform a dual function: it successfully upgraded the software version to 8.5.2 to satisfy the client’s version check and avoid suspicion, while simultaneously dropping malicious components into the background. This was followed by DLL side-loading, where a benign, signed executable was used to load a malicious library. By utilizing a legitimate file to load the malware, the attackers effectively bypassed standard security filters that prioritize scanning unsigned or unrecognized executables. This methodical approach allowed the campaign to persist within government networks for months before being detected, showcasing a high degree of operational security.
Escalation and the Deployment of Havoc
A technical highlight of this campaign was the clever use of the Microsoft iSCSI Initiator Control Panel tool to bypass User Account Control (UAC). By modifying the system’s environment variables and placing a malicious library in a controlled directory, the attackers exploited a DLL search-order hijacking vulnerability. Because the system tool is designed to auto-elevate, the attackers gained high-integrity privileges without alerting the user, effectively granting them administrative control over the infected workstation. This maneuver is indicative of a sophisticated adversary who understands the nuances of the Windows operating system and knows how to use its built-in features against the user. Once elevated privileges were secured, the attackers established permanent residency on the victim’s machine through registry modifications, ensuring that their tools would automatically restart and continue functioning even if the system was rebooted or the user logged out.
The final stage of the operation involved the deployment of the Havoc post-exploitation framework, a choice that reflects a broader trend in modern cyber-espionage. Havoc is an advanced, open-source command-and-control (C2) infrastructure that allows attackers to manage “demons” or implants capable of executing shellcode, managing local files, and pivoting through internal networks. The shift toward using powerful open-source tools like Havoc, rather than custom-coded backdoors, makes attribution more difficult for defenders, as these frameworks are widely available to various threat groups and do not carry the unique code signatures of a single entity. By using a modular framework, the TrueChaos actors could customize their toolkit on the fly, adapting to the specific defenses they encountered within different government departments. This flexibility allowed them to perform deep reconnaissance, identifying sensitive documents and communication patterns while remaining hidden beneath the noise of legitimate network traffic and standard administrative activities.
Attribution and Defensive Response
Geopolitical Context: The Shadow of State Actors
Researchers attribute Operation TrueChaos to Chinese-nexus actors based on several distinct pillars of evidence, including the infrastructure used to host the operation’s command-and-control servers. The use of Alibaba and Tencent cloud services is a common trait among China-aligned groups, providing them with a layer of domestic infrastructure that is often more difficult for Western security firms to monitor or take down. Furthermore, the tactics, techniques, and procedures observed during the campaign—such as the specific implementation of DLL side-loading and the specialized UAC bypass methods—align perfectly with the historical playbooks of known Chinese espionage groups. The targeting of Southeast Asian government entities also provides a strong geopolitical motive, as this region remains a focal point for economic and territorial competition. Infiltrating the digital infrastructure of these nations allows a state actor to gain insights into regional policy shifts, trade negotiations, and maritime strategies that directly impact their national interests.
The overlap in tooling across different campaigns provides further evidence for this attribution and points toward a coordinated espionage effort. In several instances, victims of Operation TrueChaos were simultaneously targeted by the ShadowPad framework, a highly modular backdoor frequently shared among multiple Chinese Advanced Persistent Threat (APT) units. ShadowPad is often used as a primary tool for long-term intelligence gathering, and its presence alongside the TrueConf exploit suggests a multi-pronged attack strategy. This could indicate either a shared pool of access where different units capitalize on the same initial compromise or a collaborative operation where different teams handle different stages of the intrusion. Regardless of the internal structure, the result is a formidable threat capable of maintaining persistent access across a wide array of government agencies, highlighting the importance of regional cooperation and information sharing among the targeted nations to defend against such well-resourced adversaries.
Mitigation: Securing the Update Pipeline
Upon discovery of the vulnerability, the vendor acted by releasing a critical security patch in March 2026. Organizations using TrueConf are urged to upgrade to version 8.5.3 or later to ensure their update validation mechanism is no longer susceptible to server-side manipulation. This fix introduces the cryptographic validation of update files that was missing in previous iterations, preventing the client from executing unverified code even if the server is compromised. It is critical for security teams in government and critical infrastructure sectors to verify their version numbers immediately, as any version prior to 8.5.3 remains vulnerable to this specific attack vector. Beyond simply updating the software, organizations should also review their on-premises server security, ensuring that administrative access to the TrueConf server is restricted and monitored for any unauthorized changes to the update directories or configuration files.
To assist in remediation and ongoing threat hunting, security professionals should look for specific artifacts that indicate a past or present infection. This includes searching for unauthorized files in the PowerISO or Adobe directories, which the attackers used as staging grounds for their malicious DLLs. Monitoring for unusual process chains, such as the TrueConf client spawning unexpected child executables like cmd.exe or curl.exe, can provide an early warning of an active compromise. Additionally, network defenders should block known communication paths to identified C2 IP addresses and inspect registry keys for unauthorized persistence mechanisms that point to suspicious directories. Implementing a policy of “least privilege” for all communication and productivity software can also limit the potential damage, ensuring that even if an application is compromised, the attacker’s ability to move laterally or escalate privileges is significantly hindered by existing system-level restrictions.
Future Considerations: Toward a Zero-Trust Model
Operation TrueChaos serves as a vital reminder that “trusted” on-premises software is not inherently secure and requires the same level of scrutiny as any external service. The assumption that internal network traffic is safer than external traffic is a recurring vulnerability that state actors continue to exploit with great success. By targeting the very mechanism used to keep software secure—the update process—the attackers demonstrated how a single zero-day can compromise an entire governmental infrastructure from the inside out. This highlights a fundamental flaw in the perimeter-based security model and reinforces the need for a shift toward zero-trust principles. In a zero-trust environment, no connection or update is trusted by default, regardless of whether it originates from a local server or a remote cloud. Every transaction must be verified through cryptographic proof and strict identity management before execution.
Moving forward, organizations must prioritize the integrity of their internal software supply chains as much as their external ones. This involves deploying advanced endpoint monitoring that can detect anomalous behavior within trusted applications and moving away from blanket trust for administrative tools. The adoption of robust application control and code integrity policies can prevent the execution of unauthorized libraries, effectively neutralizing the DLL side-loading techniques used in this campaign. As threat actors increasingly adopt flexible, open-source frameworks and exploit the architectural trust of air-gapped solutions, the ability to analyze routine execution techniques for subtle anomalies becomes a fundamental requirement for cybersecurity resilience. The lesson of Operation TrueChaos is clear: security is not a static state achieved by being “offline,” but a continuous process of verification and vigilance that must extend to every corner of the digital infrastructure. In light of these developments, organizations should conduct comprehensive audits of all on-premises software that utilizes internal update mechanisms to ensure they are not hosting the next silent gateway for a state-sponsored intrusion.