The stability of a modern superpower depends entirely on the invisible pulse of its energy grid, a complex web of technology that is currently facing the most sophisticated threats in human history. To address these vulnerabilities, the Office of Cybersecurity, Energy Security, and Emergency Response, known as CESER, has implemented a robust five-year strategic plan designed to shield the nation’s power and fuel systems from disruption. This initiative represents a foundational shift from reactive crisis management toward a model of preemptive fortification, ensuring that the lights stay on and the economy remains vibrant despite an increasingly hostile digital and physical environment.
Central to this mission is the transition of the American energy security apparatus into a proactive, technology-driven framework that prioritizes resilience above all else. The strategy addresses a critical question: how can the federal government effectively partner with the private sector—the primary owners of energy infrastructure—to harden systems against ransomware, physical sabotage, and natural disasters? By focusing on these core challenges, the research and planning efforts aim to guarantee that energy remains affordable, reliable, and secure for every citizen through the end of the decade.
Strengthening National Resilience: The Core Mission of the CESER Strategic Plan
The primary objective of this strategic roadmap is to build a “defense-in-depth” posture that protects the nation’s energy backbone from escalating threats. This mission is rooted in the philosophy of American energy dominance, which suggests that a country cannot be truly sovereign or economically competitive if its power supplies are vulnerable to foreign or domestic interference. Consequently, the research focuses on bridging the gap between high-level intelligence gathered by the government and the practical, daily operations of utility companies and fuel providers.
Addressing the convergence of digital and physical risks requires a holistic approach that moves beyond simple compliance. The plan seeks to answer how emerging technologies, such as advanced operational technology and real-time threat monitoring, can be integrated into aging infrastructure without causing service interruptions. By establishing clear benchmarks for success, the strategy provides a metric-driven path toward national security, emphasizing that resilience is not a static goal but a continuous process of adaptation and improvement.
Navigating a Volatile Landscape: The Origins of the 2026–2030 Strategy
This strategic direction emerged from a period of profound global instability where the energy sector became a primary target for geopolitical maneuvering. As operational technologies became more interconnected through digital networks, the surface area for cyberattacks expanded exponentially, leading to an environment where denial-of-service attacks and data exfiltration are constant concerns. This background of volatility necessitated a unified federal response that could keep pace with the speed of digital innovation and the persistence of state-sponsored actors.
Understanding the importance of this research requires acknowledging that energy security is the linchpin of all other critical infrastructure, from water treatment to healthcare and transportation. If the grid fails, every other sector follows, making the success of this strategy a matter of urgent societal relevance. By analyzing the failures and successes of previous years, the current strategy was formulated to provide a more synchronized and intelligence-led defense, moving the nation away from fragmented security patches toward a cohesive shield.
Research Methodology, Findings, and Implications
Methodology
The development of the current strategic framework utilized a collaborative and data-centric methodology that integrated insights from both public and private stakeholders. Researchers and policy experts conducted extensive risk assessments of existing energy supply chains, identifying specific vulnerabilities in hardware and software components. This involved the use of the Energy Threat Analysis Center, where government and industry experts collaborated to simulate various “degraded conditions” to see how systems would perform under duress.
Furthermore, the methodology relied on sensor-based monitoring through the Cybersecurity Risk Information Sharing Program to gather real-time data on anomalous network behavior. This evidence-based approach allowed the agency to move beyond theoretical models and focus on actual, observed threats. By combining these technical findings with feedback from Subsector Coordinating Councils, the strategy was tailored to meet the operational realities of those who manage the grid on the ground.
Findings
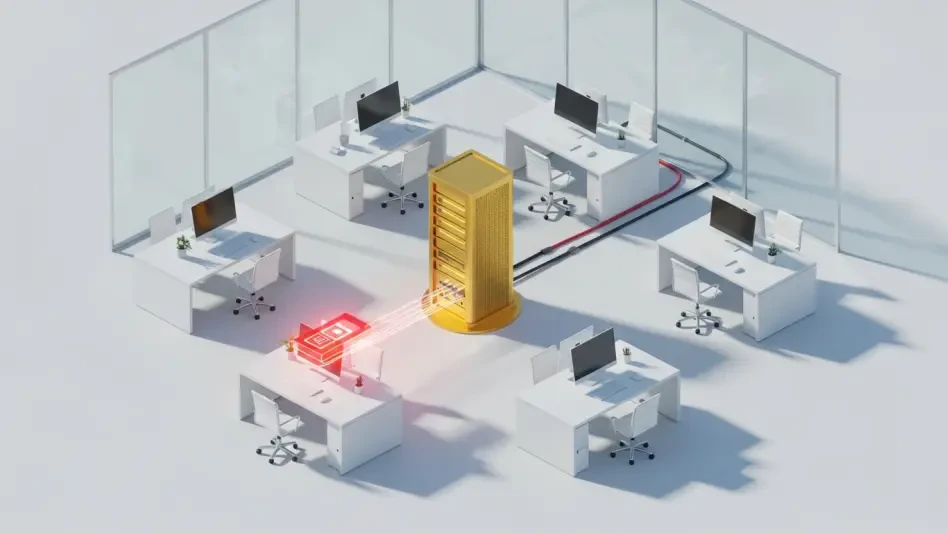
The investigation revealed that the most significant risks to the energy sector often stem from vulnerabilities deep within the global supply chain, where a single compromised component can lead to cascading failures. Findings highlighted that while large utilities often have robust defenses, smaller entities and local cooperatives frequently lack the resources to combat state-level cyber threats. This discovery prompted a shift in the strategic plan to focus on scalable, affordable security solutions that can be deployed across the entire industry regardless of a company’s size.
Moreover, the research identified that physical hardening—such as the deployment of counter-unmanned aircraft systems and reinforced facility structures—is just as vital as digital defense. The data showed that a multi-dimensional threat environment exists where physical attacks often coincide with digital disruptions to maximize chaos. Consequently, the strategy found that the most effective way to ensure grid reliability is to prioritize the hardening of “defense-critical” infrastructure that supports military and national security sites first.
Implications
The implications of these findings are far-reaching, suggesting that the era of passive infrastructure management is over. For industry leaders, this means a greater emphasis on “security by design,” where new technologies are tested for vulnerabilities before they are ever installed. This shift will likely lead to a more regulated but also more resilient marketplace, where vendors must meet higher standards of transparency regarding the origins and security of their products.
For the general public, the successful implementation of this strategy means a reduction in the likelihood of long-term power outages caused by malicious actors. The move toward actionable intelligence and rapid response frameworks implies that even when breaches occur, the systems will be capable of self-healing or operating in a limited capacity to maintain essential services. This creates a more stable economic environment, as businesses can operate with the confidence that the energy they rely on is protected by a sophisticated, multi-layered defense system.
Reflection and Future Directions
Reflection
Evaluating the progress made under this strategic vision reveals that the greatest challenge was not the lack of technology, but the difficulty of coordinating across thousands of independent entities. Overcoming the silos of information between the federal government and private corporations required a significant cultural shift toward mutual accountability. While the creation of intelligence hubs has greatly improved the speed of data sharing, the process of upgrading aging physical assets remains a labor-intensive and costly endeavor that requires sustained investment.
The research also highlighted the critical shortage of a skilled workforce capable of operating at the intersection of cybersecurity and energy engineering. While the technological solutions are being developed, the human element—training experts to recognize and respond to complex threats—was identified as an area that required more intensive focus than initially anticipated. Despite these hurdles, the unified approach has successfully created a baseline of security that did not exist in previous iterations of national planning.
Future Directions
Looking beyond the current benchmarks, future research must explore the security implications of a more decentralized grid, where residential solar and storage systems play a larger role in national energy production. As more “edge devices” connect to the primary grid, the potential for decentralized cyberattacks grows, necessitating new protocols for securing distributed energy resources. Scientists and policy makers should focus on developing automated, Al-driven defense mechanisms that can react to threats at millisecond speeds without human intervention.
Additionally, the global nature of supply chains means that international collaboration will become even more vital. Future efforts should aim to establish international standards for energy component security to ensure that hardware imported from abroad does not contain “backdoors” or other vulnerabilities. Exploring the integration of quantum-resistant encryption into industrial control systems is another essential frontier, as the rise of quantum computing could potentially render current security measures obsolete.
Toward American Energy Dominance: A Unified Vision for Grid Security
The comprehensive efforts spearheaded by CESER have successfully established a new standard for national infrastructure protection, moving the U.S. toward a future where energy security is an inherent feature rather than an afterthought. By integrating cutting-edge research with practical, real-world applications, the strategy demonstrated that a unified defense is the only way to safeguard the nation’s most critical assets. These findings reaffirmed that the resilience of the energy grid is not merely a technical challenge but a cornerstone of national sovereignty and economic health.
The implementation of these security measures provided a clear roadmap for navigating the complexities of a modern, interconnected world. The focus on defense-critical sites and the deployment of real-time monitoring tools significantly reduced the nation’s vulnerability to both digital and physical sabotage. Moving forward, the emphasis shifted toward ensuring that these advancements are sustained through continuous workforce development and the adoption of next-generation encryption. Ultimately, the work performed through 2030 laid the groundwork for a more secure and dominant American energy posture, providing the stability necessary for long-term national prosperity and technological leadership.