The realization that a trusted security scanner could serve as a trojan horse sent shockwaves through the DevOps community when the widely adopted Trivy Action repository was compromised. This incident represents a sophisticated escalation in supply-chain attacks, specifically targeting the continuous integration and delivery pipelines that modern software development relies upon so heavily. In this breach, the very tool designed to detect vulnerabilities was subverted to distribute a malicious infostealer, highlighting a systemic weakness in how GitHub Actions are consumed and trusted. Because the attack targeted existing version tags rather than introducing new ones, thousands of organizations unknowingly pulled malicious code during their routine automated builds. This event serves as a stark reminder that automated security layers are only as strong as the infrastructure that hosts them, and the trust placed in version numbering can be exploited with devastating precision. The impact is vast, affecting over ten thousand unique workflow files that rely on this specific action for safety.
Mechanisms of Pipeline Infiltration
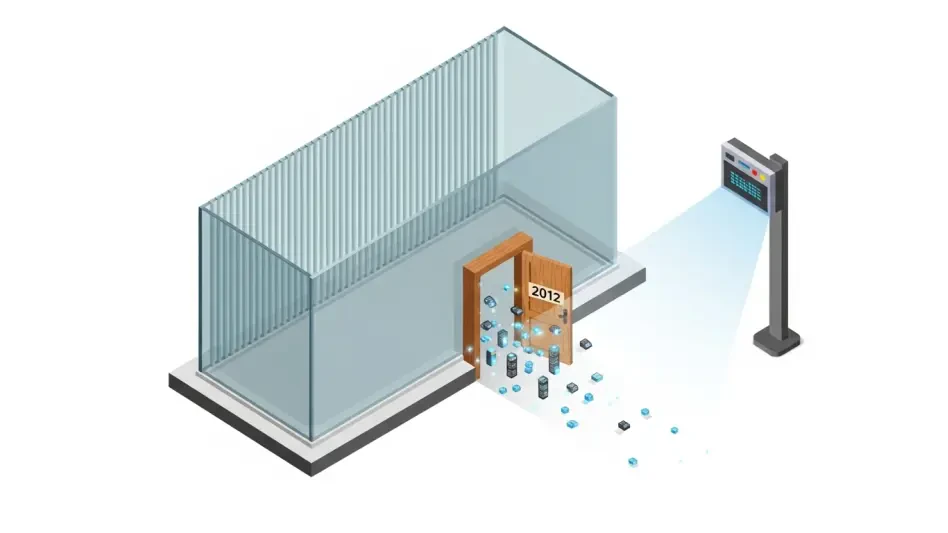
Tag Poisoning: The Art of Ghost Updates
The technical execution of the breach relied on a technique known as tag poisoning, which allowed the attacker to rewrite history without alerting the repository’s thousands of watchers. By utilizing residual credentials obtained from a previous security lapse, the threat actor managed to force-push malicious updates to nearly every existing version tag in the official repository, covering versions from the earliest releases up to the most recent iterations. This method was particularly effective because it did not trigger the standard notifications associated with a new release, which many security teams monitor as a primary defense. Instead, workflows configured to use a specific version, such as v0.34.2, began pulling the infected code immediately and silently. The breach essentially turned the repository’s versioning system against its users, transforming a tool meant for protection into a delivery system for malware that operated with the full authority of a verified developer.
To further obscure the presence of the malicious code, the attacker employed sophisticated spoofing techniques to manipulate the commit metadata within the repository. By altering the author names and timestamps associated with the malicious pushes, the threat actor made the git history appear as though the changes were legitimate maintenance performed by the actual maintainers of the project. This deceptive layering meant that even a developer who manually inspected the commit history might have been misled into believing the tags were unchanged or officially updated. The manipulation was so thorough that it bypassed the casual scrutiny often applied to small, incremental updates in dependency versions. This level of tradecraft illustrates a move toward more psychological tactics in supply-chain compromises, where the goal is to maintain the appearance of normalcy for as long as possible while harvesting data from the background of supposedly secure automated environments.
Orchestrating the TeamPCP Lifecycle
The malicious payload, identified by security researchers as the TeamPCP Cloud stealer, was designed to function as a silent auxiliary process that runs before the legitimate scanning occurs. When a GitHub workflow initiates the Trivy scan, the injected script executes first, establishing its presence in the runner environment while the actual vulnerability scan continues to run as expected. By allowing the legitimate tool to complete its task, the malware avoids raising flags that would otherwise be triggered by a failed build or a missing security report. This dual-track execution ensures that the developer remains focused on the scan results, unaware that a separate, unauthorized process is simultaneously raiding the environment for sensitive data. The script is optimized for speed and stealth, completing its primary collection tasks in a fraction of a second, which prevents it from significantly altering the overall execution time of the CI/CD pipeline.
The malware exhibits adaptive behavior based on the type of environment it encounters, ensuring maximum data yield regardless of the runner configuration. On standard GitHub-hosted runners, the script focuses on dumping process memory to extract environment variables and secrets that are often stored in memory during the build process. However, when it detects a self-hosted runner, the TeamPCP stealer expands its scope to perform a comprehensive scan of the local filesystem. In these scenarios, it actively hunts for a wide array of sensitive assets, including SSH keys, database connection strings, cloud provider configuration files, and even cryptocurrency wallets. This environmental awareness allows the attacker to pivot from simple credential harvesting to deep infrastructure access, as self-hosted runners often have broader permissions and persistent access to internal corporate networks that are not present in transient cloud-hosted environments.
Responding to Systemic Vulnerability
Sophisticated Data Theft and Concealment
Once the collection phase is complete, the TeamPCP malware employs high-grade cryptographic standards to protect the stolen data during its journey to the attacker’s infrastructure. The script utilizes AES-256-CBC encryption to wrap the harvested credentials, which is then further secured using an RSA-4096 public key wrapper. This double-encryption strategy ensures that even if the network traffic is intercepted by security monitoring tools, the contents remain unreadable to anyone without the attacker’s private key. By utilizing such robust encryption, the threat actor effectively neutralizes many traditional data loss prevention systems that rely on pattern matching or plaintext inspection to identify outbound leaks. This move highlights a professionalization of malware used in supply-chain attacks, where the focus is not just on the theft itself, but on ensuring the stolen assets remain viable and confidential for the attacker’s exclusive use.
The exfiltration phase of the attack is equally calculated, utilizing a typosquatted domain that mimics the official infrastructure of the service provider. By sending the encrypted data to a domain like scan[.]aquasecurtiy[.]org, the malware exploits the visual similarity to legitimate traffic, making it less likely to be flagged by automated firewall logs or human analysts. If this primary connection is blocked by more stringent network policies, the script is programmed to execute a clever fallback mechanism. It uses the victim’s own GitHub token to programmatically create a new, public repository under the victim’s organization or user account, often named tpcp-docs. The stolen data is then uploaded as a release asset to this new repository, allowing the attacker to simply download the files from a legitimate GitHub URL. This tactic not only facilitates exfiltration but also leaves the victim in a position where their own infrastructure is used to host and distribute their stolen secrets.
Strengthening Infrastructure Resilience
In the wake of this compromise, the primary recommendation for engineering teams is to move away from the use of mutable version tags entirely when referencing third-party GitHub Actions. While tags like v1 or v0.34 are convenient for maintaining compatibility, they are essentially just pointers that can be redirected by anyone with write access to a repository. The only way to ensure the integrity of the code being executed is to pin actions to a specific, immutable commit SHA. By referencing the long-form cryptographic hash of the code, organizations can guarantee that the version they have audited is the exact version that runs in their pipeline, regardless of any future changes made to the repository’s tags. This shift represents a fundamental change in DevOps culture, moving from a model of blind trust in maintainers to one of cryptographic verification where every dependency is treated as a potential risk that must be explicitly locked down.
Recovery from a breach of this nature requires more than just updating a configuration file; it necessitates a complete reset of the organization’s security posture. Because the compromised tags were active for an extended period, any pipeline that executed during the window of compromise must be considered a total breach. This realization requires the immediate and comprehensive rotation of all secrets that were accessible to the runner, including API tokens, cloud provider credentials, and private keys. Security teams should also implement automated monitoring for the creation of unauthorized repositories or unusual release activities within their GitHub organizations. Furthermore, adopting a policy of least privilege for CI/CD runners can limit the damage of future attacks; for instance, ensuring that runners only have the specific permissions required for their task rather than broad administrative access can prevent malware from creating fallback repositories or accessing sensitive cross-project data.
The response to the Trivy Action compromise focused on immediate remediation and the long-term hardening of supply-chain dependencies. Security teams prioritized the identification of all affected workflows, replacing compromised version tags with the verified v0.35.0 release or, more effectively, with specific commit SHAs. Organizations performed thorough audits of their GitHub environments to detect any instances of the unauthorized repositories used for data exfiltration. Furthermore, the incident prompted a broader transition toward using short-lived, identity-based credentials instead of long-lived secrets in CI/CD environments. By implementing these rigorous standards, the community moved toward a more resilient architecture that recognized the inherent risks of automated third-party integrations. This proactive approach ensured that while the breach was significant, it provided the necessary catalyst for systemic improvements in pipeline security and credential management practices.