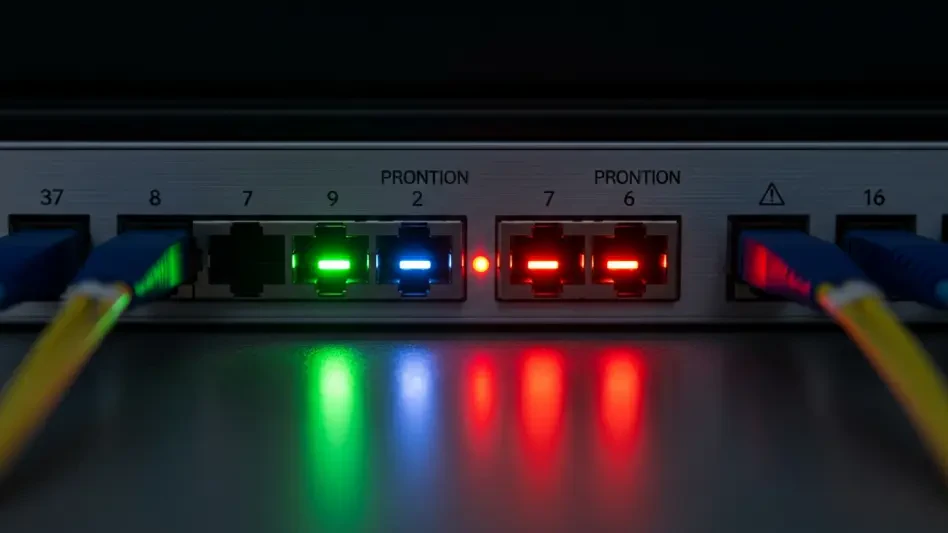
In the high-stakes theater of global cybersecurity, the speed of digital exploitation is no longer measured in weeks but in the frantic seconds it takes for a newly discovered vulnerability to be cataloged, analyzed, and weaponized by sophisticated threat actors. As the European Union Agency for Cybersecurity (ENISA) formalizes its operational status as a “Root” for the Common Vulnerabilities and Exposures (CVE) Program, the agency is not merely expanding an administrative list. It is fundamentally recalibrating how the continent identifies and neutralizes critical security flaws before they can be leveraged by adversaries.
This strategic evolution reflects a broader necessity to synchronize defense mechanisms across a diverse technological landscape. By establishing a centralized authority, the agency ensures that the identification of software bugs occurs within a framework that respects both global standards and regional operational requirements. The goal is to move away from reactive patching toward a model of predictive resilience, where the time between the discovery of a flaw and the implementation of a fix is minimized through superior coordination.
Redefining Vulnerability Management Across the European Union
The current era of hyper-connectivity demands a management strategy that is as dynamic as the threats it seeks to mitigate. ENISA has stepped into its role as a CVE Root to serve as a cornerstone for this new defensive architecture, providing the oversight necessary to maintain the integrity of the vulnerability lifecycle. This transition allows for a more granular approach to security, ensuring that European specificities in infrastructure and governance are reflected in how flaws are prioritized and reported.
By establishing this specialized hub, the agency has created a mechanism that bridges the gap between private sector research and public sector defense. This coordination ensures that no critical flaw falls through the cracks of a fragmented reporting system. Instead, every identified vulnerability is channeled through a standardized process that facilitates rapid disclosure and remediation, effectively hardening the digital borders of the entire union against exploitation.
The Critical Significance: The CVE Root Transition
For decades, the global cybersecurity community has relied on the standardized language of CVE Records to communicate threats across borders and industries. By transitioning from a mere participant to a central coordination hub, the agency addresses a growing demand for a localized yet globally integrated vulnerability backbone. This shift matters because it centralizes the oversight of authorities based within the member states, ensuring that the documentation of software flaws is handled with specific regulatory nuances in mind.
This structural change also enhances the trust between various stakeholders within the ecosystem. When national authorities and private entities know there is a dedicated regional Root, the efficiency of information sharing increases significantly. This centralized model provides a clear hierarchy and a reliable point of truth, which is essential when responding to large-scale cyber incidents that require immediate and coordinated action across multiple jurisdictions.
Scaling the European Ecosystem: Onboarding and Integration
The recent operational milestone marks a dual-track expansion of the capacity to manage the vulnerability lifecycle effectively. The agency successfully trained and onboarded four new organizations, empowering them as CVE Numbering Authorities (CNAs) with the power to assign unique identifiers to newly discovered security flaws. This expansion decentralizes the workload of discovery while maintaining a strict standard of quality and accuracy across all new records.
Furthermore, seven existing European CNAs were transitioned from the MITRE Root to the ENISA Root, a migration that streamlined reporting lines and regional coordination. This consolidation created a primary point of contact for the EU CSIRTs network and national authorities, reducing administrative friction and improving the overall accuracy of the global database. Despite this regional focus, a unified front was maintained with the U.S. Cybersecurity and Infrastructure Security Agency (CISA) to ensure the system remained a singular, global standard.
Combatting the “Frontier AI” Threat and Legislative Evolution
The push for a more robust Root role was driven largely by the emergence of “frontier AI” models, which drastically shortened the window between vulnerability discovery and active exploitation. Advanced artificial intelligence is now being used to automate the search for software bugs at a scale previously unimaginable. This technological shift necessitated a human-led infrastructure that could keep pace with machine-speed threats, ensuring that defensive measures evolved as quickly as the tools used by attackers.
Regulatory reinforcement also played a pivotal role in this transition. Proposed updates to the Cybersecurity Act provided the legislative mandate and resources required to scale these operations across all Member States. Cybersecurity leaders emphasized that as the volume of IT vulnerabilities grew, the sustainability of the global identifier system depended on these decentralized but highly coordinated regional roots. This legislative backing ensured that the agency had the necessary teeth to enforce standards and maintain operational continuity.
Framework for Effective Vulnerability Coordination
To maintain a high level of operational integrity, the newly onboarded authorities followed a structured approach to vulnerability handling that prioritized transparency and speed. Every participant adhered to strict global guidelines to ensure that CVE Records remained consistent, descriptive, and actionable for IT professionals worldwide. This systematic adherence helped prevent the duplication of efforts and ensured that the global security community received clear, non-conflicting information regarding emerging threats.
The collaborative remediation process facilitated better communication between independent researchers and software vendors, ensuring that patches were developed in tandem with public disclosure. Organizations looking to participate in the program were encouraged to align their internal security disclosures with the new reporting structure to improve the speed of global updates. Ultimately, these strategic steps consolidated the regional defense posture, providing a clear roadmap for future authorities to join the collective effort in securing the global digital infrastructure.