Zero-Day Vulnerabilities

Threats and Vulnerabilities
Is Our Critical Infrastructure Safe From Cyberattacks?
The silent hum of a power station or the rhythmic clatter of a freight train often masks a fragile digital reality where critical components remain tethered to an increasingly hostile public internet.
Trending
Read More Threats and Vulnerabilities
Trend Analysis: AI-Powered Cyberattacks in Government Systems
A lone operator recently demonstrated the terrifying capability to dismantle the digital foundations of multiple federal infrastructures in just a few weeks.
Trend Analysis Read More Threats and Vulnerabilities
Is Claude Mythos Preview Too Dangerous for the Public?
The recent disclosure of Anthropic’s Claude Mythos Preview marks a fundamental shift in the artificial intelligence landscape, signaling the end of the era defined by simple chatbots and the beginning of a period dominated by autonomous expert system...
Read More Threats and Vulnerabilities
Is Malaysia Ready for Its Evolving Cyber Threat Landscape?
Malaysia has transitioned from a quiet maritime trade hub into a high-stakes digital battleground where semiconductor patents and financial data are the new currency of national power.
Market Analysis Read More Threats and Vulnerabilities
Alcatraz AI Secures $50 Million to Modernize Physical Security
The landscape of corporate safety is undergoing a radical transformation as traditional entry methods fail to meet the rigorous demands of a hyper-connected and data-heavy global economy.
Read More Threats and Vulnerabilities
How Can You Stop the Latest FortiClient EMS Zero-Day Attack?
The sudden emergence of a zero-day vulnerability in critical infrastructure management tools often forces security teams into a reactive posture that tests the very limits of modern incident response protocols.
Read More Threats and Vulnerabilities
How Secure Is Chrome Against the Fourth Zero-Day of 2026?
The sudden discovery of a fourth major zero-day exploit within the first few months of 2026 has sent a clear shockwave through the global cybersecurity community. With CVE-2026-5281 now threatening the digital safety of over 3.
How-To Guide Read More Threats and Vulnerabilities
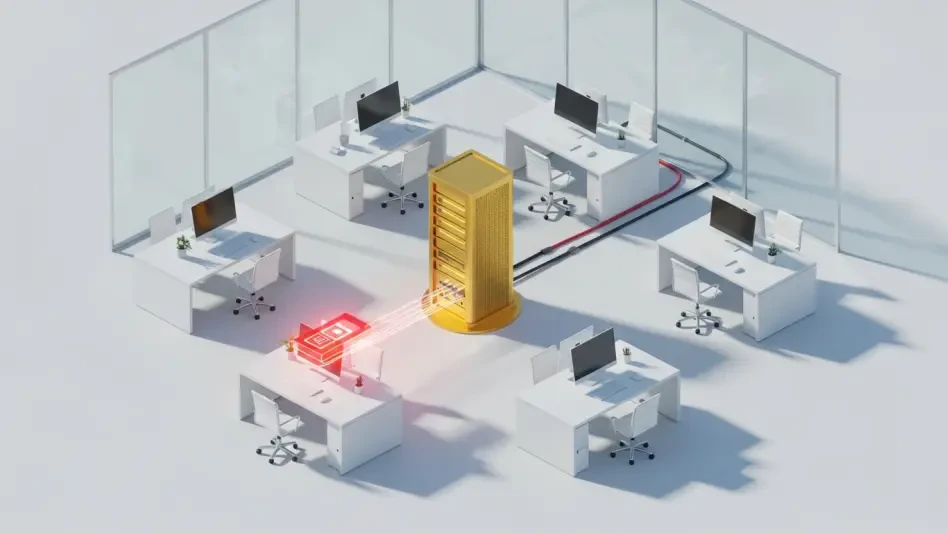
How Did Operation TrueChaos Infiltrate Secure Networks?
The sophisticated breach of a supposedly air-gapped system remains one of the most chilling prospects for security administrators who believe their servers are safe simply because they are offline.
Feature Article Read More
Get our content freshly delivered to your inbox. Subscribe now ->
Receive the latest, most important information on cybersecurity.