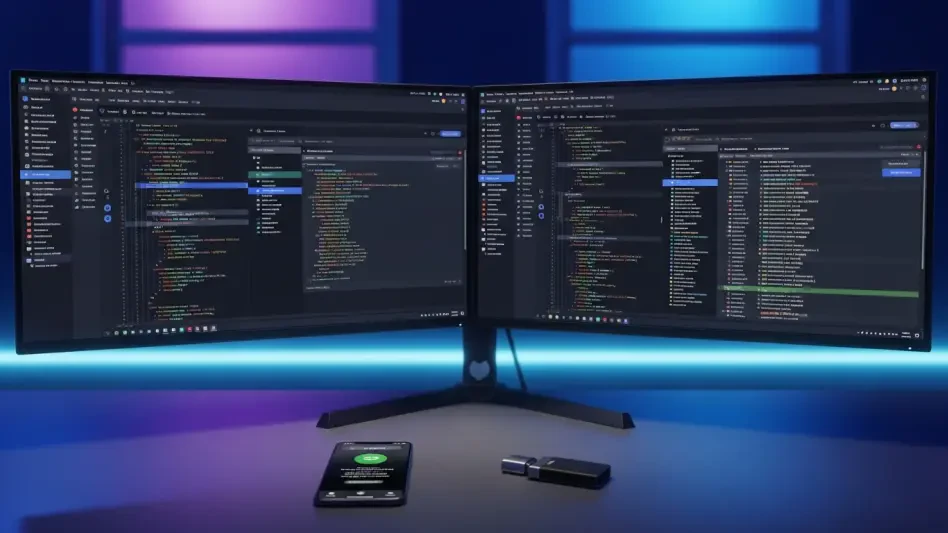
Best Practices Guide Human Factors in CyberSecurity
The rapid integration of generative artificial intelligence into cloud infrastructure has created a complex landscape where autonomous agents are often granted significant power to execute code and manage data without direct human oversight.
Read MoreYour meticulously curated collection of digital achievements and rare in-game skins now functions as a high-stakes vault attracting the attention of sophisticated global criminal syndicates looking to exploit your trust.
Trend AnalysisModern cybercriminals are currently abandoning the predictable methods of the past in favor of sophisticated, high-stakes deception that leverages the very customer service tools we have grown to trust for daily problem-solving.
Feature Article Read MoreCybercriminals are now weaponizing legitimate human-verification tools like Cloudflare Turnstile to create a sophisticated "gatekeeper" effect that masks malicious login pages.
Best Practices GuideThe rapid proliferation of unregulated gambling machines in small retail environments has fundamentally transformed neighborhood corner stores from simple community hubs into high-stakes targets for violent criminal enterprises.
Read MoreThe sophisticated convergence of generative artificial intelligence and traditional social engineering has fundamentally altered the digital threat landscape, making the identification of malicious intent more difficult than ever before.
Read MoreThis threat, known as BlackSanta, demonstrates how modern adversaries have moved beyond simple phishing to create complex, multi-stage attacks that exploit the professional obligations of administrative staff.
Feature Article Read MoreThe devastating speed of modern digital theft means a family's entire life savings can vanish into a criminal's encrypted wallet in the time it takes to brew a morning cup of coffee.
Feature Article Read More
Get our content freshly delivered to your inbox. Subscribe now ->
Receive the latest, most important information on cybersecurity.
