Global Cyberattacks & Response
Cyberсrime and Cyber Warfare
U.S. Sanctions Cambodian Senator in SE Asia Scam Crackdown
A sprawling online grift that siphoned nearly $21 billion from Americans in 2025 collided with reports of forced labor in Myanmar and Cambodia, turning a crime problem into a human-rights and national security fight overnight. The result was a U.S.
Roundup Article Read More Human Factors in CyberSecurity
Germany Probes Russia-Linked Signal Phishing of Officials
A single QR code, framed as emergency support inside a trusted app, quietly unlocked weeks of sensitive conversation as German federal prosecutors opened an espionage probe into a sweeping Signal account hijacking that hit the political establishment...
Read More Threats and Vulnerabilities
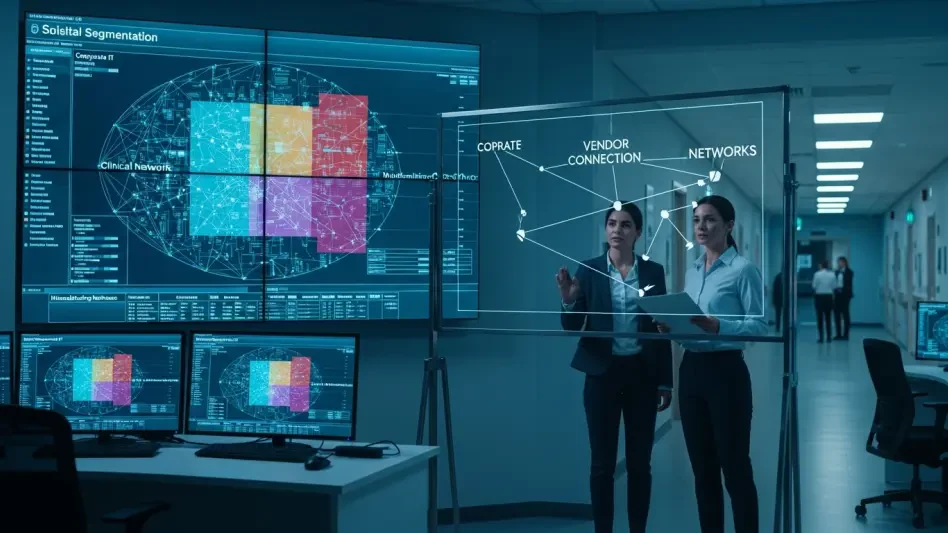
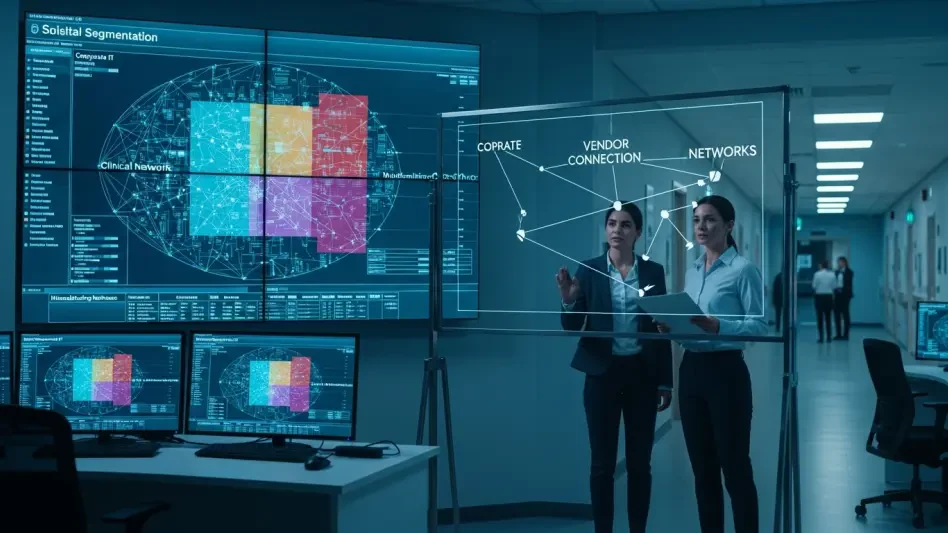
Can Defenders Outpace China's Covert SOHO Botnets?
Household routers and office gadgets now quietly double as stepping stones for state-backed hackers, turning familiar networks into cover for espionage at a scale few organizations are prepared to confront.
FAQ Read More Cyberсrime and Cyber Warfare
How Did Indonesia's Police Dismantle a Global Phishing Hub?
Phishingoperationsonceburrowedintotinycornersofthewebbutretooledintocommercialserviceswithbrandedstores, scripted toolkits, and instant bots that promised plug‑and‑play access to stolen credentials for a paying crowd.
Read More Cyberсrime and Cyber Warfare
Why Is Pay2Key Shifting From Profit to Pure Disruption?
A sudden silence often follows a digital breach, but when a United States healthcare provider recently found its entire network frozen with no demand for data, the quiet signaled a fundamental shift in the cybercrime landscape.
Feature Article Read More Human Factors in CyberSecurity
Why Is Identity Governance the New Cybersecurity Perimeter?
The traditional concept of a fortress protected by high walls and deep moats has vanished from the modern corporate landscape as digital assets migrate to the cloud.
Roundup Article Read More Cyberсrime and Cyber Warfare
Why Is Harvester Now Targeting Linux Systems in South Asia?
The landscape of regional cyber espionage has undergone a fundamental transformation as state-sponsored actors pivot their focus toward the open-source infrastructure that powers modern government and corporate backend systems.
Read More Incident Response and Forensics
How Does the Vercel Breach Impact Your Cloud Security?
When a developer discovers that their highly secure cloud environment was accessed through a seemingly benign third-party productivity tool, the illusion of perimeter security evaporates instantly.
Read More
Get our content freshly delivered to your inbox. Subscribe now ->
Receive the latest, most important information on cybersecurity.