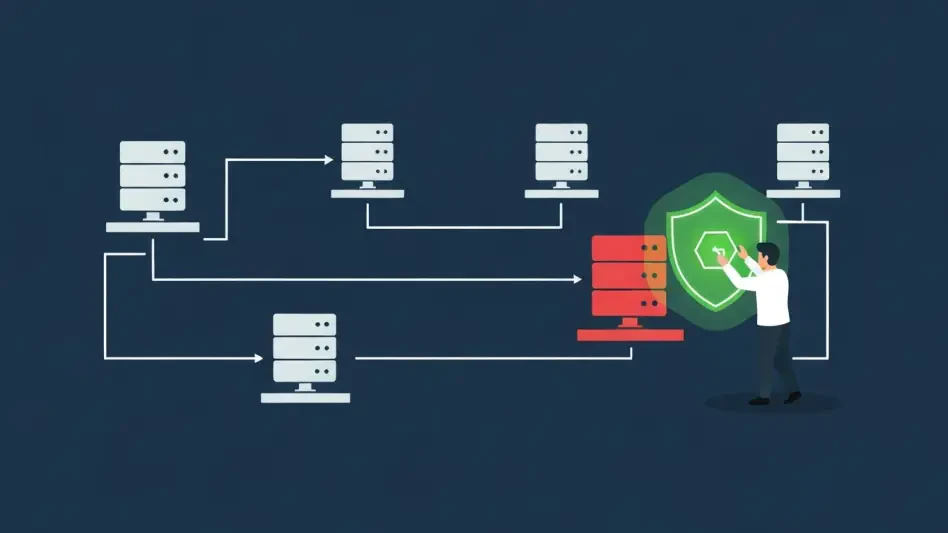
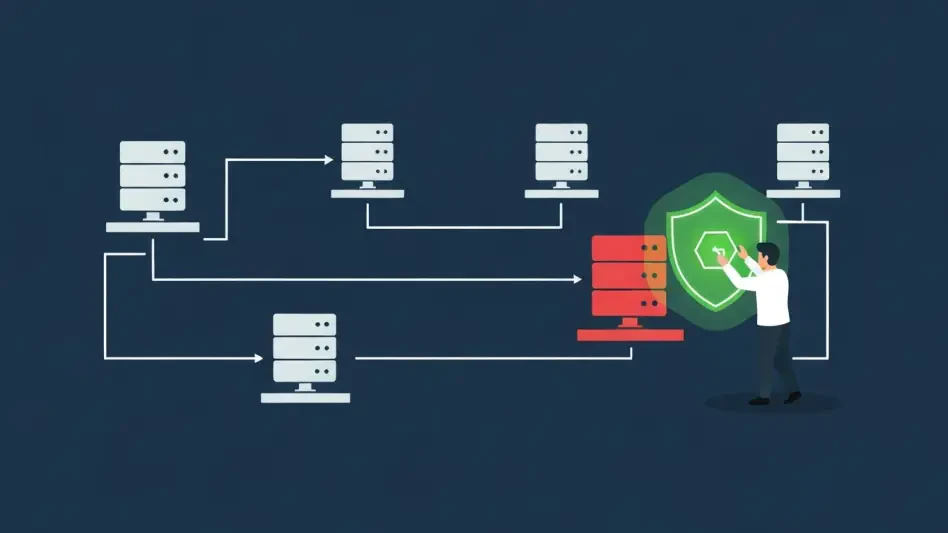
Denial of Service (DoS/DDoS) Attacks
Threats and Vulnerabilities
CISA Flags Flaws in Siemens and Schneider Electric Systems
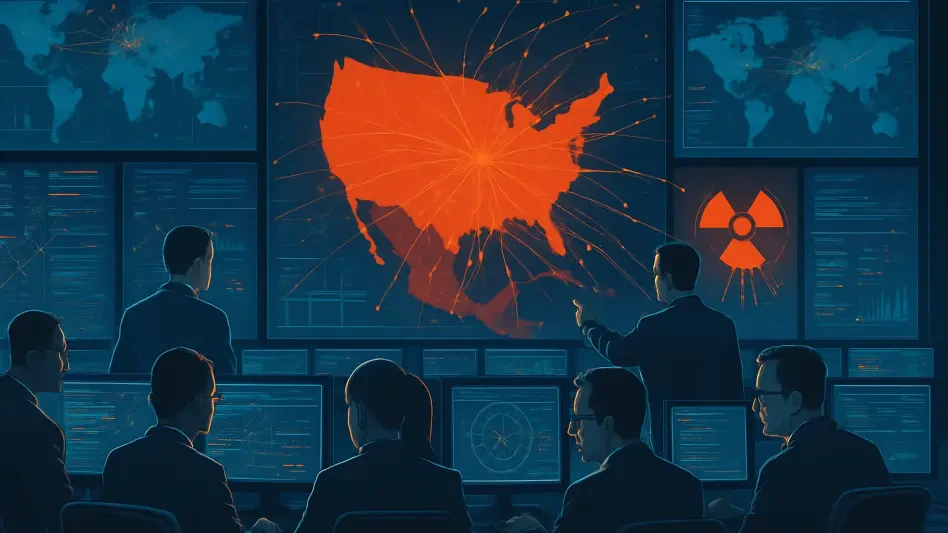
The digital transformation of critical infrastructure has unlocked unprecedented efficiency, but it has simultaneously exposed the operational core of entire nations to sophisticated digital threats that can manifest in the physical world. The U.S.
Best Practices Guide Read More Threats and Vulnerabilities
Microsoft Issues Urgent Fix for Its Own Faulty Update
The very tool designed to protect enterprise servers from external threats became the source of their sudden, widespread collapse, leaving system administrators scrambling for answers.
Feature Article Read More Threats and Vulnerabilities
Programmable Logic Controller Security – Review
The convergence of operational technology with modern networking capabilities has created unprecedented efficiency in industrial environments, but it has also quietly introduced a new generation of security risks that threaten the very foundation of...
Technology Review Read More Threats and Vulnerabilities
Agencies Sound Alarm on Pro-Russia OT Attacks
The seamless flow of clean water from a tap or the steady hum of electricity powering communities relies on a complex and often vulnerable network of industrial controls, a reality that has been brought into sharp focus by a recent wave of cyber intr...
FAQ Read More Threats and Vulnerabilities
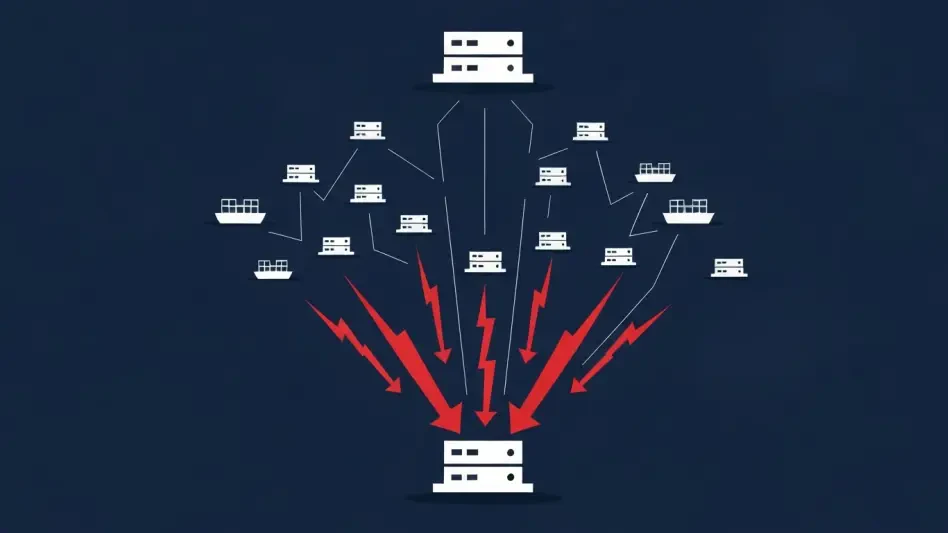
Mirai Botnet Variant Broadside Targets Maritime DVRs
A new and sophisticated variant of the notorious Mirai botnet has been identified actively targeting the maritime logistics sector, exploiting vulnerabilities in digital video recorder (DVR) systems commonly used on commercial vessels.
Read More Threats and Vulnerabilities
Trend Analysis: Nation-State Cyber Operations
The once-clear line separating digital skirmishes from tangible geopolitical conflict has effectively vanished, ushering in a new and more volatile era of strategic competition where the keyboard has become as mighty as the sword.
Trend AnalysisTrending
Read More Threats and Vulnerabilities
Cyber Deterrence Act Aims to Punish Foreign Hackers
What happens when invisible enemies can shut down power grids, steal sensitive data, or manipulate elections with a few keystrokes from halfway across the globe? This chilling reality drives a pressing need for robust countermeasures against foreign...
Feature Article Read More Threats and Vulnerabilities
GridEx VIII Bolsters Grid Resilience Against Rising Threats
In a world increasingly reliant on electricity, what happens when the power grid—the backbone of modern life—becomes a prime target for cyberattacks and physical sabotage, leaving hospitals in darkness, businesses at a standstill, and entire communit...
Feature Article Read More
Get our content freshly delivered to your inbox. Subscribe now ->
Receive the latest, most important information on cybersecurity.