Cyber Espionage Techniques

Cyberсrime and Cyber Warfare
What Are Your First Steps After a Cyber Incident?
The phrase "exploited in the wild" instills a unique sense of dread in security practitioners because it signifies that the clock didn't just start ticking—it began days, weeks, or even months ago, and the alarm is only now sounding.
Read More Cyberсrime and Cyber Warfare
Are Chinese Spies Listening to Your Calls?
The privacy of your phone calls and text messages may not be as secure as you think, especially in light of recent revelations about a widespread and highly sophisticated cyber-espionage campaign.
Read More Cyberсrime and Cyber Warfare
How Do You Catch a Killer With a Fake Website?
The darkest corners of the internet often promise anonymity for illicit activities, but a sophisticated international operation has revealed how these same platforms can become intricate traps for those with genuine criminal intent.
Read More Cyberсrime and Cyber Warfare
Why Is the Pentagon Embracing Offensive Cyber War?
The United States Department of Defense is undergoing a profound and aggressive strategic transformation, shifting from a historically reactive digital posture to a proactive doctrine of "persistent engagement.
Read More Cyberсrime and Cyber Warfare
Is Downing Street Safe From Chinese Spies?
A significant cybersecurity failure has laid bare the acute vulnerabilities at the highest levels of the UK government, following revelations that a Chinese state-sponsored hacking group methodically compromised the mobile devices of senior officials...
Read More Cyberсrime and Cyber Warfare
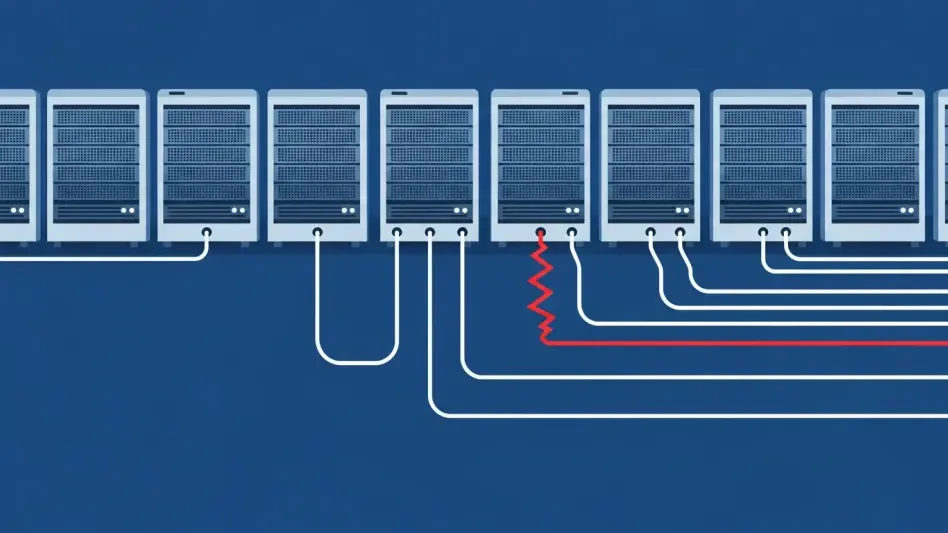
Hackers Widely Exploit Patched WinRAR Vulnerability
A critical vulnerability within the widely used WinRAR file compression software continues to be a potent weapon for a diverse array of threat actors, even though a security patch was issued more than six months ago.
Read More Cyberсrime and Cyber Warfare
Asymmetric Security Raises $4.2M for AI Cyber Defense
As the digital landscape becomes increasingly fraught with sophisticated threats, the critical window for responding to a security breach is shrinking, placing immense pressure on cyber defense teams to act with unprecedented speed and precision.
Read More Cyberсrime and Cyber Warfare
BreachForums Hacked, Exposing 324,000 Members
In a move that sent shockwaves through the digital underground, the very marketplace designed for trading stolen data found itself gutted and exposed, its secrets laid bare for the world to see.
Feature Article Read More
Get our content freshly delivered to your inbox. Subscribe now ->
Receive the latest, most important information on cybersecurity.