Configuration Security

Threats and Vulnerabilities
NVIDIA and Partners Integrate AI Into Industrial Cybersecurity
The rapid fusion of silicon intelligence with the heavy iron of industrial machinery has fundamentally transformed the global threat landscape into a digital battlefield where every sensor and motor represents a potential entry point for disruption.
Roundup ArticleTrending
Read More Threats and Vulnerabilities
How Is the Global Cyber Threat Landscape Evolving in 2026?
The modern digital ecosystem has reached a point where the distinction between a legitimate administrative action and a malicious intrusion is almost impossible to discern without deep behavioral analytics.
Read More Threats and Vulnerabilities
EU Launches New Toolbox to Secure ICT Supply Chains
The European Commission has officially unveiled a comprehensive security infrastructure known as the ICT Supply Chain Security Toolbox, which provides a standardized framework for Member States to identify and mitigate risks across complex digital ne...
Read More Threats and Vulnerabilities
Why Is the BeyondTrust RCE Flaw a Critical Ransomware Risk?
The recent addition of CVE-2026-1731 to the Known Exploited Vulnerabilities catalog by the Cybersecurity and Infrastructure Security Agency signifies a shift from theoretical risk to active digital warfare.
Read More Threats and Vulnerabilities
Is a Flaw Letting Hackers Eavesdrop on Your VoIP Phone?
A recently patched critical security vulnerability in a widely used series of Voice over Internet Protocol (VoIP) phones could allow unauthenticated attackers to remotely execute code with the highest level of privileges, ultimately enabling them to...
Read More Threats and Vulnerabilities
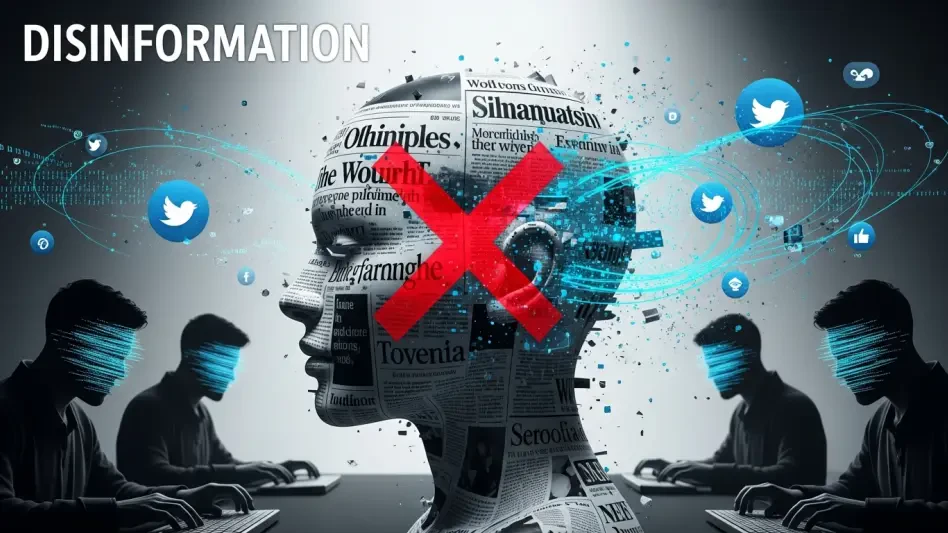
How to Build Resilience Against Disinformation
The deliberate manufacturing and rapid propagation of false information have become a structural feature of the modern digital landscape, challenging organizational stability and public trust on an unprecedented scale.
Industry Report Read More Threats and Vulnerabilities
Trend Analysis: Backup Infrastructure Attacks
The long-held belief that an organization's last line of defense, its backup systems, remained a secure sanctuary from cyber threats has been decisively and dangerously proven false.
Trend Analysis Read More Threats and Vulnerabilities
Could North Korean Spies Be on Your Payroll?
The unassuming remote IT contractor who just fixed a critical bug in your system could be funneling their entire salary to a sanctioned nuclear weapons program without anyone in the company suspecting a thing.
How-To Guide Read More
Get our content freshly delivered to your inbox. Subscribe now ->
Receive the latest, most important information on cybersecurity.