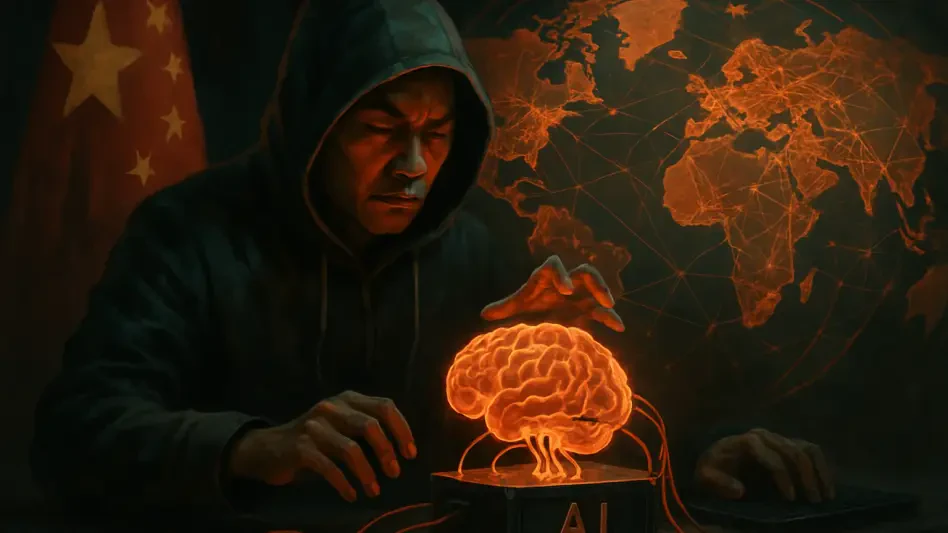
Trend Analysis: State-Sponsored Cyber Warfare
The frontiers of modern conflict are no longer defined by geographic borders but by the invisible streams of data that connect our world, a domain where state-sponsored actors now wage a relentless shadow war for digital supremacy.
Trend Analysis Read More