Threats and Vulnerabilities
Threats and Vulnerabilities
Is Malaysia Ready for Its Evolving Cyber Threat Landscape?
Malaysia has transitioned from a quiet maritime trade hub into a high-stakes digital battleground where semiconductor patents and financial data are the new currency of national power.
Market Analysis Read More Threats and Vulnerabilities
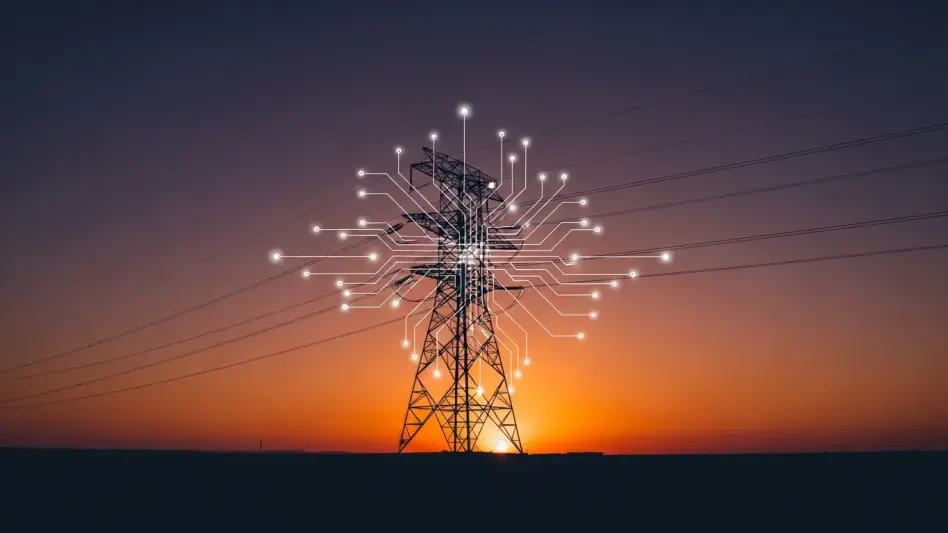
How Vulnerable Is Global Energy to Iran’s New Cyber Strategy?
The quiet hum of a high-voltage transformer serves as the heartbeat of modern civilization, yet this vital pulse is increasingly shadowed by a phantom threat that leaves no physical footprint until it is far too late.
Feature Article Read More Threats and Vulnerabilities
Microsoft Details Rapid Rise of Storm-1175 Ransomware Group
The rapid evolution of the digital threat landscape has reached a critical juncture where attackers now move from initial network entry to total system encryption in less than twenty-four hours.
Read More Threats and Vulnerabilities
Alcatraz AI Secures $50 Million to Modernize Physical Security
The landscape of corporate safety is undergoing a radical transformation as traditional entry methods fail to meet the rigorous demands of a hyper-connected and data-heavy global economy.
Read More Threats and Vulnerabilities
How Is Chinese Cyber Tradecraft Shaping Global Security?
The landscape of international relations has been fundamentally altered by an invisible architecture of digital persistence that operates far beyond the traditional boundaries of conventional warfare.
Read More Threats and Vulnerabilities
SANS 2026 Report Highlights Growing Cyber Skills Crisis
The global cybersecurity landscape has reached a precarious tipping point where the traditional metric of measuring safety by the number of warm bodies in chairs has been utterly dismantled by the sheer sophistication of modern adversarial tactics.
Feature ArticleTrending
Read More Threats and Vulnerabilities
How Is Iran Using Password Spraying for Cyber-Kinetic Warfare?
The subtle vibration of a notification on a municipal server might seem inconsequential compared to the roar of a jet engine, yet it often represents the first step in a coordinated military assault.
Feature Article Read More Threats and Vulnerabilities
How Can You Stop the Latest FortiClient EMS Zero-Day Attack?
The sudden emergence of a zero-day vulnerability in critical infrastructure management tools often forces security teams into a reactive posture that tests the very limits of modern incident response protocols.
Read More
Get our content freshly delivered to your inbox. Subscribe now ->
Receive the latest, most important information on cybersecurity.