Threats and Vulnerabilities

Threats and Vulnerabilities
CISA Warns of New Evasive Brickstorm Malware Variant
A newly identified malware variant, sophisticated enough to erase its own digital footprints by forgoing system-level dependencies, now presents an urgent and escalating threat to critical infrastructure across North America.
Industry Report Read More Threats and Vulnerabilities
Old Microsoft Flaw Is Now Under Active Attack
A security vulnerability, long since patched and relegated to the digital archives, has explosively re-entered the spotlight, demonstrating that in cybersecurity, the past is never truly gone.
Roundup Article Read More Threats and Vulnerabilities
Is Your Apple Device Vulnerable to a New Zero-Day Attack?
Apple has issued an urgent and comprehensive series of security updates across its entire product ecosystem to address a critical zero-day vulnerability that has been actively exploited in highly targeted cyberattacks.
Trending
Read More Threats and Vulnerabilities
Microsoft Patches Critical Notepad Code Execution Flaw
The humble text editor, a fixture on Windows desktops for decades, recently became the unlikely focus of a critical security alert that revealed how even the simplest applications can be transformed into potent attack vectors.
Feature Article Read More Threats and Vulnerabilities
How Serious Is Apple's Latest Zero-Day Flaw?
The recent discovery of a critical vulnerability actively being used to compromise iPhones, Macs, and other devices serves as a stark reminder that even the most fortified digital ecosystems are not impenetrable.
Industry Report Read More Threats and Vulnerabilities
Trend Analysis: Defense Industry Cyber Threats
The digital blueprints for tomorrow's military hardware are now the primary targets in a relentless, undeclared war being waged in cyberspace against the global defense industrial base.
Trend Analysis Read More Threats and Vulnerabilities
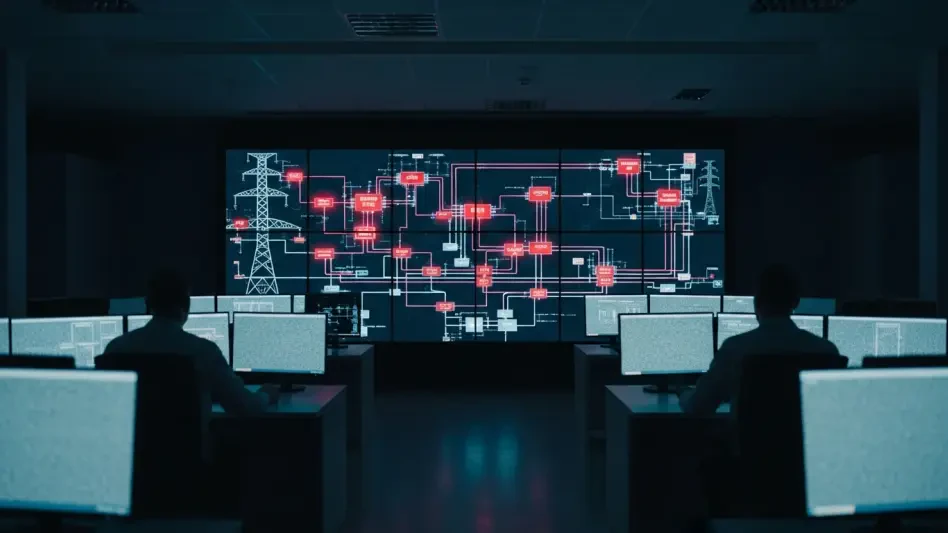
CISA Warns of Critical OT Flaws After Poland Cyberattack
A targeted and destructive cyberattack against Poland’s energy infrastructure has offered a chilling real-world demonstration of how easily theoretical vulnerabilities in operational technology can be weaponized.
Roundup Article Read More Threats and Vulnerabilities
Why Is Crypto Investment Fraud Skyrocketing?
The recent sentencing of a key figure in a massive international cryptocurrency scam that swindled victims out of over $73 million serves as a stark reminder of the escalating dangers lurking within the digital asset landscape.
FAQ Read More
Get our content freshly delivered to your inbox. Subscribe now ->
Receive the latest, most important information on cybersecurity.