Threats and Vulnerabilities

Threats and Vulnerabilities
UEFI Secure Boot Configuration – Review
The silent, split-second process that verifies a computer’s integrity before the operating system even loads has become one of the most critical yet misunderstood battlegrounds in modern cybersecurity.
Technology Review Read More Threats and Vulnerabilities
700Credit Data Breach Exposes 5.6 Million
A routine application for an auto loan has become the key that unlocked the private financial lives of millions of Americans, exposing a critical vulnerability deep within the automotive industry.
Roundup Article Read More Threats and Vulnerabilities
Oyster Malware Strikes Finance Firms via Fake Downloads
The search for everyday business software has become the newest and most deceptive battleground for financial institutions facing a relentless wave of sophisticated cyberattacks.
Roundup Article Read More Threats and Vulnerabilities
Empire 6.3.0 Advances Post-Exploitation for Red Teams
In the ever-evolving landscape of cybersecurity, the advantage often goes to the side that can most accurately replicate and anticipate real-world threats, making advanced adversary emulation a cornerstone of a proactive defense strategy.
Read More Threats and Vulnerabilities
New Tool Exposes Snap Store Security Flaws
In an era where digital storefronts serve as the primary gateway for software, the underlying security of the applications they host has become a paramount concern for users and developers alike.
Read More Threats and Vulnerabilities
Is Your Browser Vulnerable to an Active Zero-Day Threat?
In an increasingly connected digital world, the web browser serves as the primary gateway to the internet for billions of users, yet this ubiquity also makes it a prime target for malicious actors seeking to compromise systems on a massive scale.
Read More Threats and Vulnerabilities
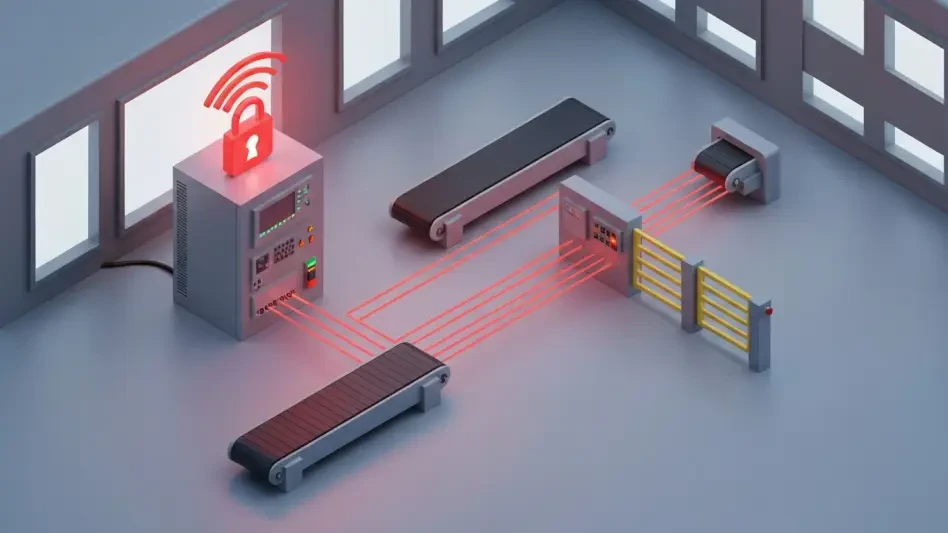
Programmable Logic Controller Security – Review
The convergence of operational technology with modern networking capabilities has created unprecedented efficiency in industrial environments, but it has also quietly introduced a new generation of security risks that threaten the very foundation of...
Technology Review Read More Threats and Vulnerabilities
Industrial Routers Become Key Targets for OT Attacks
In the sprawling digital ecosystems that power modern industry, the most significant security threats are no longer aimed at the core machinery but are instead knocking relentlessly at the digital front door, targeting the very devices that connect o...
Feature Article Read More
Get our content freshly delivered to your inbox. Subscribe now ->
Receive the latest, most important information on cybersecurity.