The rapid fusion of silicon intelligence with the heavy iron of industrial machinery has fundamentally transformed the global threat landscape into a digital battlefield where every sensor and motor represents a potential entry point for disruption. As Operational Technology (OT) converges with Information Technology (IT), the air-gapped isolation that once protected power plants and manufacturing floors has evaporated. This intersection creates a new frontier of industrial vulnerability, where the software governing a facility is as critical as the hardware it controls.
When critical systems like global power grids and pharmaceutical production lines become interconnected, the stakes of a cybersecurity breach shift dramatically. A successful infiltration is no longer limited to the theft of intellectual property or personal data; it now carries the risk of physical catastrophe. In this high-stakes environment, the failure of a single valve or the overheating of a turbine due to malicious code can have devastating real-world consequences for public safety and regional stability.
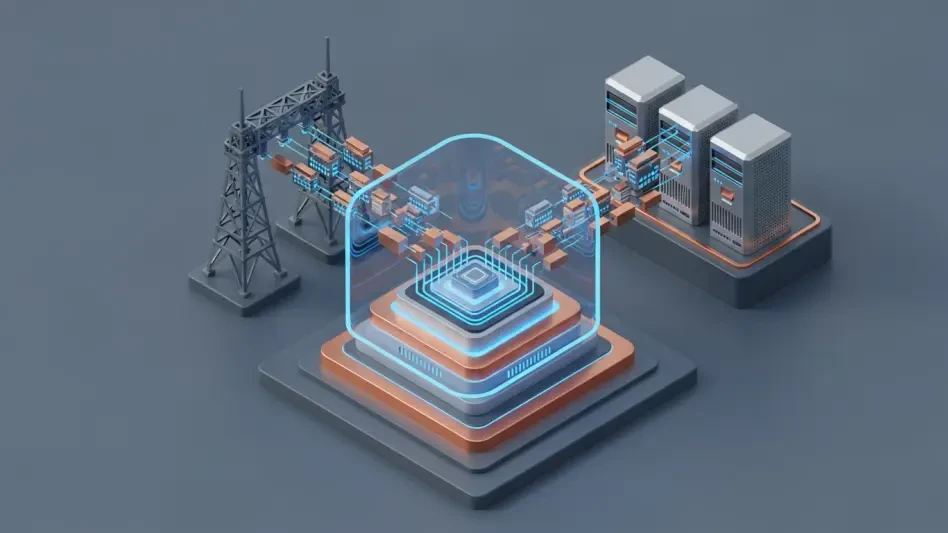
To counter these emerging risks, NVIDIA is collaborating with a broad ecosystem of industry leaders to redefine how physical infrastructure is protected. By integrating high-speed artificial intelligence and accelerated computing at the industrial edge, these partnerships aim to create a defensive shield that operates at the speed of the attacks it faces. This approach moves beyond traditional software patches, favoring a robust framework where security is baked into the very hardware that powers modern industry.
The Evolution of Defense in the Era of Connected Industry
The transition toward a connected industrial landscape necessitates a departure from the reactive security models of the past. As factories and utility providers adopt the “AI Factory” model, the volume of data generated at the edge exceeds the capacity of human operators to monitor effectively. Consequently, the defense of these assets must evolve into an autonomous, intelligent system capable of identifying and neutralizing threats before they can impact the physical world.
Addressing the Vulnerability Gap in Aging Legacy Assets
Many Industrial Control Systems (ICS) currently in operation were engineered decades ago with a focus on mechanical longevity and reliability rather than digital resilience. These legacy assets often lack the computational resources to run modern encryption or security agents, creating a significant mismatch with the sophisticated tools used by contemporary cyber adversaries. This gap represents a systemic weakness in the foundation of global infrastructure that cannot be ignored.
Traditional methods of securing IT environments, such as frequent “patching” and software updates, are often impossible in high-availability OT environments where even a few minutes of downtime can cost millions of dollars. As a result, industrial operators require a fundamental re-architecture of security that provides protection without requiring constant modifications to the underlying control logic. Experts advocate for a shift toward hardware-isolated security layers that can wrap around legacy devices, providing a modern defense perimeter for ancient components.
Industry leaders are increasingly moving away from static, perimeter-based defenses that assume anything inside the network is safe. Instead, the focus has shifted toward embedded security solutions that can adapt in real-time to the specific protocols and behaviors of industrial hardware. By implementing these intelligence-driven layers, organizations can extend the secure lifespan of their existing investments while significantly reducing the attack surface available to hackers.
Offloading Security Complexity to Dedicated Hardware
The introduction of the NVIDIA BlueField Data Processing Unit (DPU) provides a critical solution to the challenge of securing time-sensitive industrial automation. By serving as a dedicated isolation layer, the DPU ensures that intensive security processing—such as deep packet inspection and encrypted traffic analysis—does not consume the CPU cycles needed for machine control. This separation is vital for maintaining the millisecond-level precision required in modern manufacturing and energy distribution.
Decoupling threat detection from the primary operational workload allows facilities to maintain maximum uptime while simultaneously running rigorous security protocols. Historically, industrial operators faced a difficult “latency vs. security” dilemma, where adding protection often meant sacrificing the performance of the system. Accelerated hardware eliminates this compromise, enabling deep visibility into network traffic without introducing the lag that could lead to physical mechanical failures.
Furthermore, this hardware-centric approach provides a secure enclave that is physically separate from the host operating system. Even if an industrial application is compromised, the security logic running on the DPU remains isolated and functional, allowing it to detect the breach and take corrective action. This level of resilience is becoming the standard for critical infrastructure projects that demand the highest levels of reliability and trust.
Deciphering the Logic of AI-Driven Zero Trust at the Edge
Implementing a “Never Trust, Always Verify” philosophy in OT environments requires innovative strategies to handle agentless legacy devices and proprietary industrial protocols. Unlike standard office computers, many industrial controllers cannot have security software installed directly on them. Therefore, the enforcement of Zero Trust must occur at the network level, utilizing AI to recognize and validate the identity of every device attempting to communicate across the factory floor.
Strategic innovations from partners like Forescout and Akamai demonstrate how micro-segmentation can be applied to prevent the lateral movement of threats within a network. By using AI to analyze traffic patterns at the edge, these systems can automatically isolate a suspicious device before it can spread malware to other parts of the facility. This proactive containment is far more effective than traditional models that rely on a centralized, reactive response from a remote cloud server.
Comparative analysis of recent security deployments shows that edge-enforced policies are significantly more successful at stopping zero-day exploits than older, centralized models. Because the intelligence resides locally, the system can make split-second decisions to shut down unauthorized communication paths. This localized enforcement ensures that even if one segment of a power grid is targeted, the rest of the infrastructure remains functional and secure.
Strengthening Critical Supply Chains Through Strategic Alliances
The collaboration between Siemens and Palo Alto Networks is pioneering the development of “AI-ready” data centers designed specifically for the industrial sector. these facilities consolidate critical functions such as disaster recovery, long-term data archiving, and real-time threat mitigation into a unified, high-performance architecture. By standardizing these security frameworks, large-scale industrial operators can ensure a consistent level of protection across global supply chains.
In the energy sector, the shift toward identity-based protection is becoming particularly pronounced. Xage Security is applying these advanced protections to midstream pipeline infrastructures and the massive AI factories that support energy optimization. This ensures that the digital nervous system of the energy grid is protected by the same level of sophisticated encryption and verification used in the world’s most secure financial institutions.
These specific industry applications illustrate how standardized AI frameworks can be customized to meet the unique safety and regulatory requirements of different sectors. Whether it is the rigorous safety standards of a chemical plant or the high-volume data needs of a modern automotive factory, the integration of AI-driven security provides a flexible foundation. These alliances ensure that as industries modernize, they do so with a defensive posture that is built for the complexities of the future.
Navigating the Shift Toward Proactive Industrial Resilience
The move toward an AI-integrated security model allows for the creation of a global intelligence network fueled by local enforcement. As individual “AI Factories” detect new types of anomalies or attack vectors, those insights can be shared across entire industrial networks almost instantly. This collective defense mechanism means that a threat identified at a single site can result in the automatic strengthening of defenses for thousands of other facilities worldwide.
Organizations looking to adopt these technologies should prioritize agentless visibility and hardware-accelerated segmentation. This focus allows them to protect critical assets that are too fragile or too old to support traditional software updates. By adopting international standards like IEC 62443, leadership teams can create a roadmap for integrating AI into existing operational workflows without disrupting the core mission of their organization.
Securing the Digital Nervous System of Modern Society
The expansive collaboration between NVIDIA and its global partners marked a permanent departure from the era of reactive, perimeter-based cybersecurity. By embedding intelligence directly into the hardware of our critical infrastructure, these organizations established a proactive defense posture that proved capable of adapting to the most sophisticated digital threats. This transition ensured that the physical systems governing modern life remained resilient even as they became more complex and interconnected.
Industry leaders successfully demonstrated that the historical trade-off between operational performance and robust security was no longer a necessity. Through the use of dedicated processing units and edge-based AI, facilities achieved unprecedented levels of visibility and control without compromising the precision of their mechanical processes. The implementation of these technologies provided a blueprint for how other sectors could modernize their legacy assets while maintaining the highest standards of safety and uptime.
The ultimate vision of a future where industrial productivity and cybersecurity were inextricably linked became a reality through these strategic alliances. By creating a secure foundation for the digital nervous system of society, these efforts ensured that global progress remained on a stable and safe path. This proactive approach to defense ultimately redefined the relationship between man, machine, and the digital intelligence that protects them both.