The silent hum of a modern hospital ward now resonates with the invisible transmission of data, where every heartbeat captured by a medical monitor represents a potential entry point for a sophisticated digital adversary. As healthcare systems transition into fully integrated digital ecosystems, the security of medical hardware has moved from a secondary IT concern to a primary pillar of national security. This review examines the current state of medical device cybersecurity, specifically focusing on the vulnerabilities inherent in globalized supply chains and the proactive measures required to protect patient lives from remote exploitation.
Evolution and Fundamentals of Medical Device Connectivity
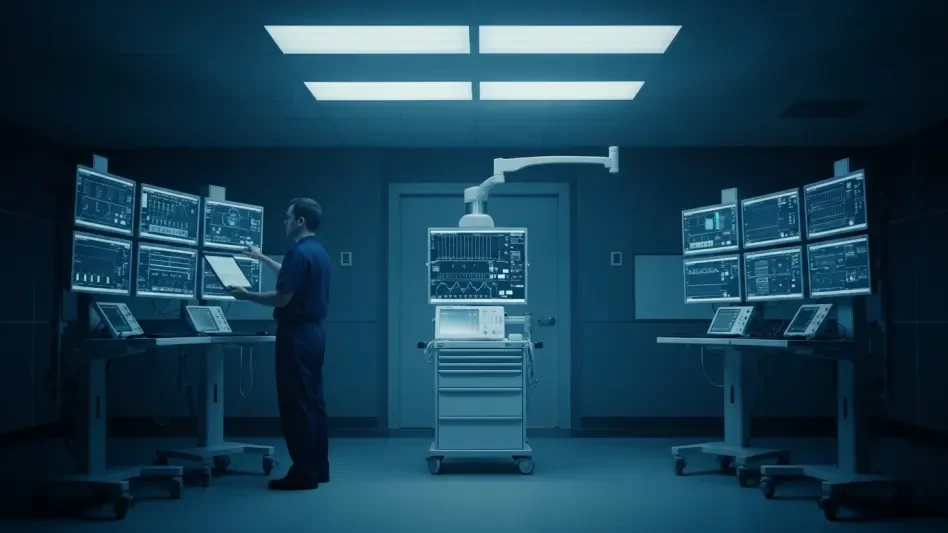
The transformation of medical technology from isolated bedside tools to interconnected nodes within the Internet of Medical Things (IoMT) has fundamentally altered the healthcare landscape. Historically, a patient monitor was a standalone unit, but today, these devices function as sophisticated data hubs that communicate across hospital networks to update electronic health records in real time. This evolution was driven by the need for clinical efficiency and the desire for data-driven diagnostic precision, yet it frequently outpaced the development of robust defensive architectures.
The core principles of this connectivity rely on standardized protocols that allow diverse machines to talk to one another. However, many of these devices were designed with clinical reliability as the priority, often leaving security as an afterthought. This context is vital because the very features that enable a doctor to view a patient’s vitals from a remote office also provide a pathway for unauthorized actors to intercept that same data. Consequently, the technology has reached a critical juncture where its utility must be balanced against the systemic risks of its inherent openness.
Core Technical Components and Security Frameworks
Internet of Medical Things and Network Integration
The Internet of Medical Things represents a vast web of sensors, wearables, and clinical devices that form the backbone of modern diagnostics. These components function by collecting sensitive biological data and transmitting it through a series of local gateways to centralized servers. The performance of these systems is measured by their latency and data fidelity, which are crucial for life-critical applications. However, the integration process often creates a “flat” network structure where a single compromised device allows an attacker to move laterally across an entire hospital’s digital infrastructure.
Significance in the overall system lies in the fact that these devices are no longer just tools but are now actual endpoints on a massive, distributed network. When a device like a smart infusion pump or a patient monitor is integrated, it carries its own firmware and operating system, which may contain undocumented vulnerabilities. If these components lack localized firewalls or segmented communication paths, they become the weakest link in a chain that includes sensitive financial data and personal medical histories.
Authentication Protocols and Remote Access Management
Technical frameworks for securing these devices have traditionally relied on simple password protections, which have proven woefully inadequate in the face of modern cyber threats. Advanced authentication protocols now emphasize multi-factor verification and the elimination of “hardcoded” credentials that are often baked into device firmware by manufacturers. Remote access management has become a focal point because it allows technicians to perform maintenance from afar, but it also creates “backdoors” that can be exploited by foreign entities or independent hackers.
Real-world usage of these security features involves the implementation of zero-trust architectures, where no device is granted access to the network without continuous verification. This is a significant shift from older models that assumed any device behind the hospital’s main firewall was safe. By analyzing the technical performance of these protocols, it becomes clear that the most effective systems are those that can identify anomalous behavior at the device level, such as a monitor attempting to send data to an unrecognized international IP address.
Current Trends and Emerging Threat Landscapes
The current trajectory of medical cybersecurity is defined by an increasing focus on supply chain integrity and the risks posed by foreign-manufactured hardware. Regulatory bodies like the Cybersecurity and Infrastructure Security Agency have begun flagging specific devices that contain hidden vulnerabilities, signaling a shift toward more aggressive state-level oversight. There is a growing trend of “active defense,” where healthcare providers no longer wait for a breach to occur but instead engage in continuous vulnerability scanning and hardware auditing.
Moreover, the rise of nation-state espionage has changed the nature of the threat from simple data theft to potential kinetic sabotage. As geopolitical tensions influence the technological landscape, the origin of a device’s components has become as important as its clinical performance. Industry behavior is moving toward a preference for “trusted” hardware sources, even if it comes at a higher procurement cost. This shift reflects a realization that the long-term liability of a security breach far outweighs the initial savings of cheaper, unvetted equipment.
Real-World Applications and Sector Deployments
A prominent example of this technology in action can be seen in the recent defensive mandates issued across the state of Texas. Publicly owned medical facilities and state agencies have been tasked with conducting exhaustive reviews of their device inventories to identify equipment produced by high-risk foreign manufacturers. This deployment of cybersecurity policy is not just an administrative exercise; it is a direct response to documented cases where patient monitors were found to have unauthorized remote access capabilities.
In these sectors, the implementation of cybersecurity reviews serves as a first line of defense for critical infrastructure. By cataloging every device capable of network transmission, these institutions are creating a comprehensive map of their digital vulnerabilities. This use case highlights a broader movement where the healthcare sector is adopting the same rigorous standards found in the defense and aerospace industries, treating every internet-connected medical device as a sensitive asset that must be guarded against foreign interference.
Technical Hurdles and Regulatory Obstacles
One of the most persistent technical hurdles is the presence of legacy hardware that was never intended to be secured against modern cyber attacks. Many hospitals operate on tight budgets and continue to use equipment that is a decade old, which cannot support the latest encryption standards or authentication protocols. Replacing this entire fleet of hardware is a massive financial and logistical undertaking that slows the adoption of more secure systems.
Furthermore, regulatory obstacles often create friction between innovation and safety. While the Food and Drug Administration provides guidelines for device security, these standards are frequently criticized for being too slow to adapt to the rapidly evolving threat landscape. Manufacturers also face the challenge of navigating a patchwork of state and federal laws that may have conflicting requirements for data privacy and reporting. Mitigating these limitations requires a unified approach that combines legislative action with technical standardization across the industry.
Future Outlook and Strategic Development
Looking ahead, the development of “security-by-design” will likely become the mandatory standard for all new medical devices entering the market. This involves building defensive layers into the hardware itself, such as tamper-resistant chips and automated update mechanisms that do not require manual intervention from hospital staff. Potential breakthroughs in artificial intelligence may also allow for real-time threat detection, where the device itself can recognize and block a cyber attack before it reaches the hospital network.
The long-term impact of these developments will be a more resilient healthcare system that can withstand both localized attacks and broader geopolitical disruptions. Strategic development will likely focus on creating “prohibited technology” lists that are updated in real time, ensuring that healthcare providers are always aware of which manufacturers pose a risk. As the industry matures, the distinction between a medical device and a secure computing device will continue to blur, leading to a new era of high-integrity clinical technology.
Final Assessment and Industry Impact
The comprehensive review of medical device cybersecurity revealed that the industry reached a critical turning point where digital defense became inseparable from patient care. Stakeholders realized that the convenience of remote monitoring and network integration carried hidden costs that demanded a radical shift in procurement and oversight. The Texas directives served as a catalyst for this change, forcing a move away from passive trust toward a model of active, verified security across all public health infrastructures.
This transition demonstrated that the protection of sensitive health data was as much a matter of national sovereignty as it was a clinical necessity. The analysis indicated that while technical hurdles remained, the commitment to refining security frameworks provided a necessary blueprint for future technological deployments. Ultimately, the industry moved toward a more cautious and resilient posture, ensuring that the life-saving potential of connected medical technology was no longer compromised by the silent threat of unauthorized access.