The quiet hum of a high-voltage transformer serves as the heartbeat of modern civilization, yet this vital pulse is increasingly shadowed by a phantom threat that leaves no physical footprint until it is far too late. While the world has grown accustomed to the digital graffiti of “hacktivists” defacing websites or leaking emails, the focus of cyber warfare has undergone a chilling metamorphosis. Today, the most dangerous actors are no longer seeking to embarrass their targets; they are meticulously mapping the internal nervous systems of power grids and water treatment plants. This transition represents a shift from temporary disruption to the terrifying reality of “pre-positioning,” where an adversary gains clandestine access to critical switches and valves, waiting for the precise geopolitical moment to trigger a systemic collapse.
The Invisible Frontline: Why the Flick of a Switch Is the New Weapon of War
The energy sector has emerged as the primary theater for asymmetric conflict, a space where a single technician at a keyboard can project more power than a traditional infantry battalion. In this new doctrine, the goal is not immediate destruction but the establishment of a “dormant threat.” By infiltrating industrial control systems (ICS), state-backed actors create a scenario where they hold the keys to a nation’s stability. This strategy allows an aggressor to exert pressure without ever firing a shot, using the threat of a darkened city or a dry reservoir as a bargaining chip in international negotiations. The subtlety of these operations means that the most dangerous attack is the one that has already happened but remains undetected, lying in wait behind a firewall that was supposed to be impenetrable.
As the lines between digital and physical infrastructure blur, the vulnerability of the grid becomes a matter of national survival rather than just technical security. The energy industry is particularly susceptible because its operations rely on real-time synchronization; even a momentary interruption in the flow of electricity can cause physical damage to generators and transformers. Moreover, the psychological impact of a domestic blackout is a force multiplier for an adversary. When a population loses access to heating, lighting, and clean water, the social contract begins to fray, creating a level of domestic chaos that conventional military strikes rarely achieve. This invisible frontline is where the next major conflict will likely be decided, long before the first boots hit the ground.
From Disruption to Strategic Presence: Understanding the Shift in Tehran’s Doctrine
Tehran has fundamentally recalibrated its digital strategy, moving away from episodic harassment toward a more sophisticated, sustained campaign of state-backed operations. This evolution is driven by the necessity of asymmetric warfare, where Iran seeks to offset its conventional military limitations by exploiting the digital dependencies of its adversaries. By utilizing a network of “proxy hacktivists,” the state maintains a layer of plausible deniability that complicates international attribution. These groups often masquerade as independent entities or ideological collectives, making it difficult for targeted nations to justify a direct state-level response. This ambiguity is a core component of the Iranian doctrine, allowing for aggressive probing of foreign networks while minimizing the risk of immediate retaliation.
The strategic logic behind this shift is centered on gaining long-term geopolitical leverage through a clandestine presence. Rather than executing loud, disruptive strikes that would trigger an immediate investigation, Iranian actors are increasingly focused on maintaining access to sensitive environments within the energy and utility sectors. This “force multiplier” effect ensures that if a kinetic conflict were to break out in the Middle East, Iran would possess the capability to retaliate across the globe. By holding critical infrastructure hostage through latent malware and compromised credentials, the state creates a digital deterrent that forces its rivals to weigh the costs of escalation against the potential for widespread domestic infrastructure failure.
The Global Energy Grid Under Siege: A Convergence of Risks
While Iran’s tactics have become more aggressive, they exist within a broader context of global instability where the energy grid is the second most targeted industry worldwide. The threat landscape is crowded with persistent actors, most notably from China and Russia, each pursuing their own strategic objectives. The Chinese “Volt Typhoon” campaign, for instance, has set a high bar for sophisticated pre-positioning, demonstrating how deep and persistent an intrusion can become. Iran has adapted its methods to mirror these high-level threats, focusing on the specialized hardware that governs the flow of oil, gas, and electricity. This convergence of hostile interests means that grid operators are defending against a multifaceted assault that never truly ceases.
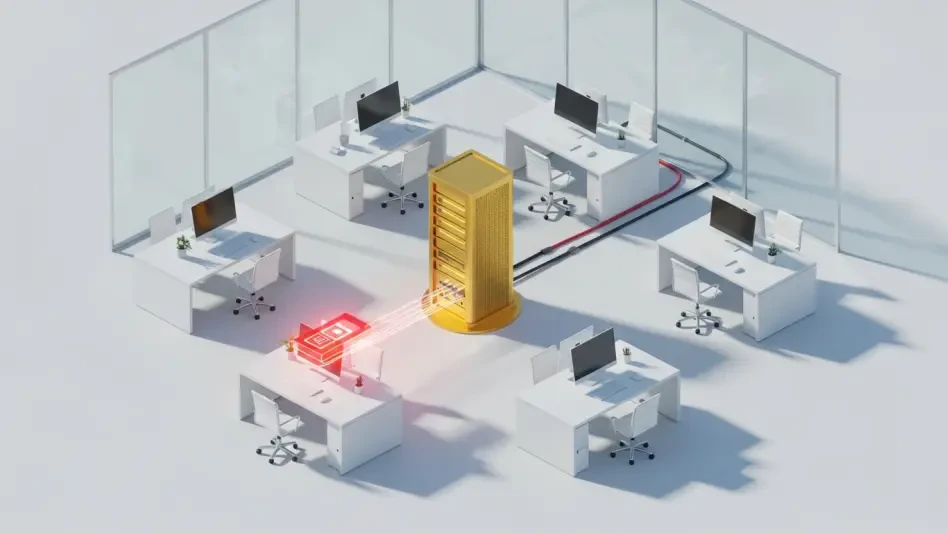
The disappearance of “air-gapping”—the practice of keeping industrial systems entirely disconnected from the internet—has opened a Pandora’s box of new entry points. Modernization efforts aimed at increasing efficiency through internet-connected sensors and remote monitoring have inadvertently created a massive attack surface. Furthermore, the “Weakest Link” problem continues to plague national defenses. While large-scale utilities often invest heavily in cybersecurity, smaller municipal providers and rural cooperatives frequently lack the budget or expertise to fend off state-sponsored actors. These smaller entities serve as vulnerable gateways; once an attacker compromises a minor node, they can often pivot through interconnected networks to reach the core of the national energy grid.
The High Cost of Failure: Economic Cascades and Real-World Consequences
The financial repercussions of a successful infrastructure breach are not merely theoretical; they are catastrophic. The historical precedent set by the Colonial Pipeline incident showed how a relatively straightforward ransomware attack could trigger billion-dollar losses across supply chains and induce regional panic. However, a coordinated state-sponsored strike on the grid would be far more severe than a criminal ransom demand. Experts warn of “cascading failure” scenarios, where the disabling of a small fraction of regional power generators could lead to a systemic blackout across several states. In such a case, the economic hit could exceed $1 trillion, as businesses shutter, transportation halts, and health services are compromised.
Beyond the immediate financial loss, the physical recovery from such an attack poses a unique challenge. Replacing specialized infrastructure, such as high-voltage transformers, is not a simple task; these components often have lead times of several months or even years. Iranian “password-spraying” campaigns have recently targeted global energy organizations and cloud environments, suggesting a focus on the logistical and administrative backbones that manage these physical assets. If an attacker can delete the configuration data or corrupt the software that manages the grid’s balance, the process of “black starting” a dead system becomes an engineering nightmare. The time required to restore power could stretch into weeks, causing irreversible damage to the national economy and public safety.
Building a Resilient Shield: Practical Strategies for Defending Critical Infrastructure
Defending the grid requires a shift from voluntary industry guidelines to mandatory, uniform cybersecurity standards. Currently, the fragmented nature of energy ownership means that security levels vary wildly between different providers. Implementing a “Cybersecurity by Design” approach is essential, ensuring that every piece of hardware and software added to the grid is vetted for vulnerabilities at the manufacturing stage. This must include a rigorous audit of the global supply chain to prevent the introduction of backdoors or malicious code before a component even reaches an American utility company. Strengthening the digital perimeter is a collective responsibility that requires the same level of federal oversight as physical aviation safety or nuclear regulation.
Bridging the resource gap between major utility giants and smaller cooperatives is another critical step toward a resilient shield. Federal technical assistance programs should be expanded to provide real-time monitoring and incident response capabilities to under-resourced providers. Additionally, enhancing data-sharing protocols between government intelligence agencies and private sector infrastructure owners will allow for faster detection of “quiet” intrusions. Perhaps most importantly, the industry must address the acute shortage of specialized workers who understand both traditional cybersecurity and the unique requirements of industrial control systems. By training a new generation of defenders and mandating transparency in incident reporting, the energy sector could finally move toward a proactive stance that prioritizes systemic resilience over reactive firefighting.
The evolution of Iranian cyber operations demonstrated that the digital integrity of the physical world was no longer a secondary concern. Policymakers and industry leaders recognized that the transition from symbolic disruption to strategic pre-positioning required a fundamental rewrite of the national security playbook. By moving toward mandatory standards and fostering a more integrated defense network, the energy sector began to address the systemic vulnerabilities that had been ignored during the rapid push for digitalization. The focus shifted away from simply preventing intrusions and toward ensuring that, even in the event of a breach, the critical functions of the grid remained operational. These actions helped secure a future where the flick of a switch remained a convenience rather than a potential casualty of an invisible war.