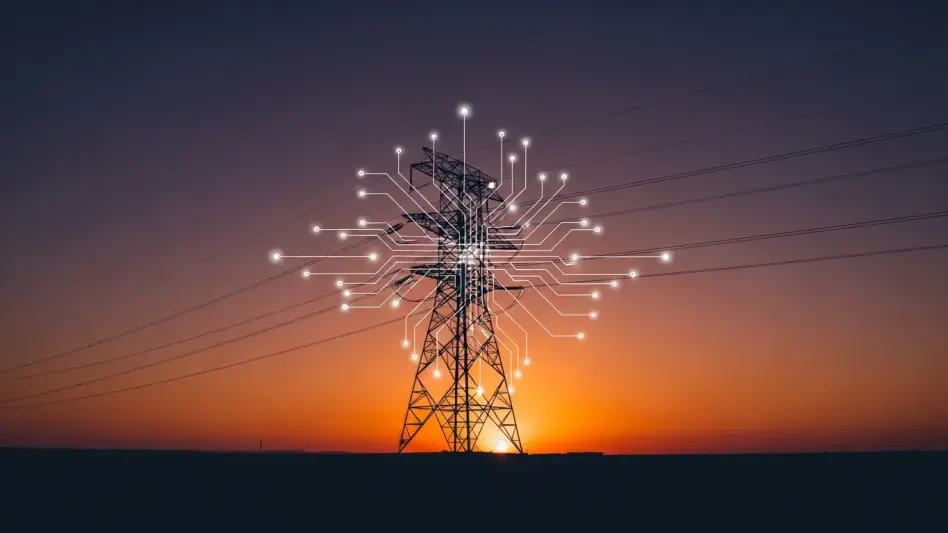
The convergence of kinetic warfare and digital sabotage has fundamentally altered the modern paradigm of national security, as demonstrated by the unprecedented resilience of Ukrainian networks under relentless pressure. Since the onset of the full-scale invasion in early 2022, the world has witnessed a dual-front conflict where missile strikes are often synchronized with distributed denial-of-service attacks and data-wiping malware. To counter this, a sophisticated ecosystem of international support has emerged, blending the financial power of foreign governments with the rapid-response capabilities of the global tech industry. According to a recent white paper by the Cyber Defense Assistance Collaborative (CDAC), this cooperation has been the cornerstone of Ukraine’s digital survival. While the headlines often focus on tanks and artillery, the quiet battle for control over state registries, energy grids, and communication channels has proven that a nation’s sovereignty is now as much a matter of code as it is of territory.
The sheer scale of this digital assistance is both impressive and surprisingly efficient when viewed alongside traditional military expenditures. Between 2022 and 2025, approximately $2.29 billion was committed to cyber defense, with about $1.29 billion successfully implemented on the ground. When compared to the staggering $190.7 billion provided in overall military aid during the same timeframe, cyber assistance accounts for a mere 1.2 percent of the total package. This statistic reveals a critical insight for future strategic planning: cybersecurity is an exceptionally high-impact, low-cost component of modern defense. By investing a fraction of the cost of a modern fighter jet fleet into firewalls, threat intelligence, and cloud migration, Ukraine has managed to keep its government operational and its citizens connected, even as traditional infrastructure faced physical destruction. This dynamic underscores a fundamental shift in how global powers perceive the value of digital readiness in a prolonged state of high-intensity conflict.
Analyzing Stakeholder Contributions: Speed vs. Scale
Private Sector Agility: Immediate Digital Reinforcements
In the chaotic early months following the 2022 invasion, the private sector demonstrated a level of speed and adaptability that traditional state bureaucracies simply could not match. As Russian state actors attempted to dismantle Ukrainian communication networks, global technology firms stepped in with massive injections of software, satellite connectivity, and real-time threat intelligence. This phase of the conflict saw a peak in corporate activity during the fourth quarter of 2022, as firms prioritized the rapid deployment of cloud-based protections to safeguard sensitive state data. These companies operated with a sense of urgency that bypassed the standard procurement cycles, providing Ukrainian defenders with the tools needed to identify and neutralize intrusions before they could cause catastrophic damage to the power grid or banking systems. This early intervention was characterized by the donation of thousands of software licenses and the provision of 24/7 incident response support, which essentially served as a digital “first aid” for the country’s besieged infrastructure.
However, the nature of this private assistance has evolved from emergency patches to a more complex, ongoing partnership that highlights both the strengths and the limitations of corporate charity. While the initial wave of support was invaluable, much of it was delivered as short-term donations or trial software that eventually required renewal or sustainable funding. This created a unique administrative challenge for Ukrainian officials, who found themselves managing a patchwork of different platforms and expiring agreements. Despite these hurdles, the contribution of the tech industry cannot be overstated; it provided the critical “software-first” approach that allowed Ukraine to remain agile. The ability of private firms to deploy updates in real-time and share anonymized threat data across borders created a collective defense shield that is now being studied as a blueprint for future public-private cooperation in times of crisis. The relationship proved that in the digital age, a company’s technical expertise can be just as influential as a nation’s diplomatic weight.
Government Stability: Building the Hardware Foundation
While the private sector provided the initial digital shield, foreign governments eventually took the lead in providing the massive scale and physical infrastructure necessary for long-term endurance. By 2025, government commitments for cyber defense reached approximately $1.7 billion, representing the largest portion of the total aid package. Unlike the software-heavy focus of corporate partners, government aid has been heavily skewed toward hardware, with physical equipment appearing in nearly 80 percent of all state-led assistance packages. This includes everything from secure servers and ruggedized laptops to specialized networking hardware and encrypted communication devices. This focus on “metal and wires” is a strategic necessity; advanced cybersecurity tools like endpoint detection and response (EDR) systems cannot operate effectively on outdated or compromised legacy hardware. Foreign governments recognized that for software-based defenses to work, the underlying physical layer of the Ukrainian network had to be modernized and secured against physical tampering.
This transition toward government-led hardware procurement also reflected a shift toward more formal, long-term defense planning. Between 2022 and 2025, over $930 million was dedicated specifically to standalone hardware procurement, ensuring that Ukraine’s cyber defenders had the tools to maintain a persistent presence across their networks. These government packages often came with more rigorous vetting and integration processes, which, although slower than private-sector initiatives, provided a level of standardization that was missing in the early days of the war. By investing in the physical foundation of the digital state, international partners helped Ukraine move away from a reactive “firefighting” mode and toward a structured, resilient defense posture. This hardware-centric approach also facilitated better interoperability between Ukrainian forces and their international allies, creating a common technical language that has become essential for ongoing intelligence sharing and joint defensive operations.
Systemic Coordination: Navigating the Bureaucratic Landscape
Multilateral Frameworks: The Rise of European Leadership
As the conflict matured, the initial “ad hoc” nature of international aid gave way to structured, multilateral coordination mechanisms that have significantly improved the efficiency of resource delivery. Key initiatives such as the IT Coalition, spearheaded by Estonia and Luxembourg, and the Tallinn Mechanism have become the primary conduits for both civilian and military digital assistance. These frameworks have allowed donor nations to pool their resources, share technical expertise, and ensure that Ukraine’s most urgent needs are prioritized without redundant efforts. Estonia, in particular, has emerged as a digital powerhouse in this regard, leveraging its own advanced cybersecurity experience to provide millions of dollars in critical infrastructure support and satellite communication systems. This collective approach has not only streamlined the flow of aid but has also provided a unified front against state-sponsored digital aggression, signaling that an attack on one partner’s digital sovereignty is met with a coordinated response from many.
Furthermore, a notable shift in the leadership of these efforts occurred as the war progressed into 2025. While the United States was a dominant force in the early stages, European nations and the European Union have increasingly stepped up to fill the void as American domestic political dynamics led to fluctuations in aid levels. The EU has played a central role by deploying cyber rapid-response teams and establishing military cyber labs that provide hands-on training for Ukrainian personnel. This regional leadership shift is significant because it reflects a growing realization among European capitals that Ukraine’s digital security is inextricably linked to the broader security of the continent. By professionalizing the delivery of aid through established diplomatic and military channels, these multilateral frameworks have transformed what was once a series of disjointed donations into a coherent, strategic alliance that is capable of sustaining a multi-year defense effort.
Operational Friction: Bridging the Gap Between Pledges and Reality
Despite the success of coordinated frameworks, the delivery of cyber defense assistance is still plagued by significant administrative and logistical friction. The CDAC report highlights a persistent “commitment-to-delivery” gap, where billions of dollars in pledged aid often take months or even years to reach the front lines. This delay is largely attributed to the complex procurement procedures inherent in government bureaucracies, which are designed for peacetime oversight rather than wartime urgency. For example, a pledge made in late 2024 might not result in actual hardware delivery until mid-2025 due to the time required for contract bidding, security vetting, and shipping logistics. In a domain where threat actors can change their tactics in hours, these bureaucratic bottlenecks represent a major vulnerability. The friction is further compounded by the need to ensure that new equipment is compatible with existing Ukrainian systems, which often requires additional layers of technical assessment and customization.
Moreover, the “administrative fatigue” experienced by Ukrainian officials cannot be ignored, as they must navigate the differing reporting requirements and technical standards of dozens of donor nations. Each assistance package, whether it consists of a few dozen laptops or a comprehensive cloud migration project, comes with its own set of paperwork and oversight demands. This burden often diverts the attention of highly skilled Ukrainian cybersecurity experts away from the actual defense of their networks and toward the management of international relationships. To address this, some donors have begun to implement more flexible funding models, but the fundamental tension between the need for speed and the requirement for accountability remains a central challenge. Reducing this friction will be critical for the continued success of the mission, as the ability to rapidly integrate new technologies is often the deciding factor in whether a cyberattack is successfully repelled or leads to a widespread system failure.
The Path Forward: From Crisis Response to National Sustainability
Information Scarcity: Understanding the Reporting Paradox
Tracking the true scale and impact of cyber assistance remains an exercise in navigating a fog of information, where operational security often takes precedence over public transparency. Because cyber warfare involves sensitive technologies and intelligence-gathering methods, both donors and recipients are often reluctant to disclose the full details of their collaboration. Many private-sector firms, for instance, provide support under non-disclosure agreements to protect their proprietary algorithms or to prevent their employees from becoming targets of retaliatory attacks. This lack of detailed reporting means that the $2.29 billion figure identified in current datasets is almost certainly a conservative estimate. Voluntary reporting mechanisms, while helpful, capture only a fraction of the total activity, leaving analysts to piece together a fragmented picture of how resources are actually being utilized on the digital battlefield.
This transparency gap is a double-edged sword; while it protects the tactical advantages of the defenders, it also makes it difficult to assess the long-term effectiveness of different aid models. Without granular data on which specific tools or training programs are yielding the best results, donor nations risk misallocating resources or repeating the mistakes of previous years. The CDAC analysis suggests that many assistance packages go entirely unrecorded because they are bundled with larger military or humanitarian programs, further obscuring the true cost of digital defense. As the international community looks to refine its support strategies, there is a growing call for better, more standardized reporting methods that can provide accountability without compromising security. Understanding the nuances of this “reporting paradox” is essential for building a more transparent and effective aid ecosystem that can withstand the scrutiny of taxpayers and policymakers alike.
Educational Sovereignty: Prioritizing Skills and Long-Term Defense
As the conflict moves forward, the focus of international assistance is undergoing a profound transformation, shifting from the provision of “black box” technologies to the development of domestic human capital. Ukrainian officials have increasingly prioritized requests for training and professional development, recognizing that hardware and software are only as effective as the people who operate them. This shift toward educational sovereignty aims to create a self-sustaining cybersecurity workforce that can defend the nation’s digital borders with less reliance on external experts. By the current period, training initiatives have expanded from basic technical skills to advanced digital forensics, threat hunting, and strategic policy development. This focus on “brain power” ensures that even if international aid levels fluctuate, Ukraine will possess the internal expertise necessary to maintain its defenses and innovate in response to new threats.
This long-term vision for capacity building is not just about survival; it is about preparing for a post-war landscape where Ukraine can emerge as a global leader in cybersecurity. The experience gained on the front lines of the world’s first full-scale cyber war has created a generation of Ukrainian professionals with unparalleled expertise in countering state-sponsored threats. International partners are now focusing on integrating these experts into global security networks, creating a two-way exchange of knowledge that benefits the entire democratic world. By moving away from a model of dependency on short-term donations and toward a partnership based on mutual growth and permanent skill development, the international community is helping Ukraine build a digital fortress that is resilient, independent, and capable of withstanding the evolving challenges of the future. This emphasis on human potential represents the ultimate evolution of international aid, turning a crisis into an opportunity for lasting national strength.
In the final analysis, the international effort to bolster Ukraine’s cyber defense demonstrated that the most effective response to digital aggression was a blend of private-sector agility and government-led infrastructure. While the early years of the conflict were defined by emergency software injections and ad hoc coordination, the focus transitioned into a structured, hardware-heavy defense posture supported by multilateral frameworks. Moving forward, stakeholders should prioritize the reduction of administrative bottlenecks and the standardization of reporting to ensure that aid reached its destination with maximum speed. The most sustainable path for the future involves a continued shift toward domestic capacity building and specialized training, allowing Ukraine to transition from a recipient of aid to a self-reliant hub of cybersecurity expertise. This evolution not only secured the immediate digital sovereignty of a nation under fire but also provided a durable template for global cooperation in an increasingly interconnected and volatile world.