Modern network security environments increasingly rely on a single point of failure that simultaneously acts as their most sophisticated defense mechanism. The Cisco Secure Firewall Management Center (FMC) has positioned itself as this indispensable hub, providing the centralized intelligence required to govern sprawling enterprise architectures. However, as organizations consolidate their security stacks, the trade-off between administrative ease and systemic risk becomes a defining narrative in contemporary infrastructure management.
An Introduction to Cisco Secure Firewall Management Center
The FMC functions as the primary administrative engine for the Cisco security ecosystem, offering a unified platform to manage intrusion prevention, application control, and malware defense. In a landscape where edge devices are frequently distributed across global locations, this center provides the “single pane of glass” visibility that security teams require to maintain consistency. It translates complex security intents into actionable rules across multiple physical and virtual firewall instances.
Beyond simple rule orchestration, the platform serves as a massive telemetry aggregator. By pulling data from every corner of the network, it allows administrators to visualize threat patterns that might appear isolated if viewed on individual devices. This macro-level perspective is what distinguishes the FMC from basic management tools, turning it into a proactive monitoring suite that informs broader organizational risk assessments.
Key Architecture and Management Capabilities
Centralized Security Administration and Policy Control
The core strength of the FMC lies in its ability to synchronize global security policies with granular precision. When a threat is identified at one edge of the network, the management center can propagate updated signatures and blocking rules to every connected gateway in real time. This capability is essential for mitigating lateral movement within internal networks, as it ensures that no single firewall remains an island of outdated information.
Furthermore, the integration of advanced malware protection and intrusion prevention systems into a unified workflow reduces the cognitive load on security analysts. Instead of toggling between disparate interfaces, users can manage file sandboxing and deep packet inspection settings from a single dashboard. This architectural cohesion allows for more rapid response times during active incidents, which is a critical metric for enterprise resilience.
Web-Based Interface and Underlying Operating System
The software utilizes a sophisticated web-based management interface designed to handle the complexity of modern administrative scripts and Java-based objects. This layer is responsible for translating user commands into low-level configuration changes on the firewall sensors. While the interface is designed for accessibility, the underlying system architecture must manage intense computational tasks, such as generating detailed compliance reports and processing historical event logs.
This reliance on a complex web stack, however, introduces specific technical dependencies. The management of these Java-based objects requires a robust execution environment to prevent memory leaks or processing delays during high-traffic periods. The effectiveness of the FMC is therefore inextricably linked to how well the underlying operating system handles these administrative demands without compromising the stability of the security services it oversees.
Latest Developments in Network Security and Vulnerability Research
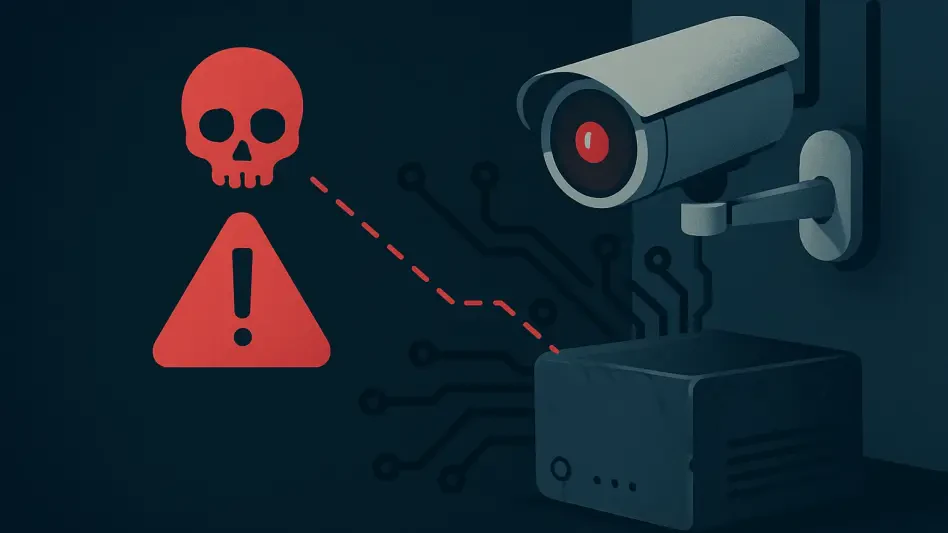
The recent disclosure of high-severity vulnerabilities, specifically CVE-2026-20079 and CVE-2026-20131, has cast a spotlight on the inherent risks of centralized management. These flaws represent a significant threat because they allow unauthenticated, remote attackers to bypass traditional security gates and gain root-level access. In the world of network defense, root access to a management console is the equivalent of handing over the keys to the entire kingdom.
Industry behavior has shifted toward a more skeptical analysis of edge technology, especially after reports surfaced regarding long-term undetected exploits in similar hardware. Cisco’s Public Security Incident Response Team (PSIRT) has responded by increasing the transparency of their biannual security cycles. This shift suggests that the era of “set and forget” security infrastructure is over, replaced by a need for constant vigilance and proactive vulnerability hunting by both vendors and clients.
Real-World Applications and Deployment Scenarios
In large-scale enterprise environments, the FMC is typically deployed to manage complex clusters of firewalls that protect data centers and cloud gateways. These organizations rely on the platform’s ability to handle high-volume logging and real-time threat intelligence feeds. The capacity to group devices into logical containers based on geography or function allows for tailored security postures that reflect the specific needs of different business units.
Industries such as finance and healthcare use the FMC as a cornerstone of their compliance strategies. By centralizing all security events, these organizations can generate audit-ready reports that prove the efficacy of their malware protection and access controls. This centralized logging is not merely a convenience; it is a structural requirement for meeting modern data sovereignty and protection regulations in a globally connected market.
Technical Hurdles and Systemic Security Challenges
The most pressing challenge currently facing the FMC is the management of unauthenticated access risks. When a vulnerability like a Java deserialization flaw occurs, it targets the very mechanism used to communicate with the management interface. These flaws are particularly insidious because they can be triggered before a user even logs in, turning the management portal itself into a vector for remote code execution.
Moreover, the absence of manual workarounds for these critical defects highlights a rigid dependency on official patching. Unlike traditional software where a feature can be disabled to mitigate a bug, the FMC’s integrated nature often means that the vulnerability resides in a core system process. This creates a high-pressure environment for IT departments who must balance the need for immediate patching with the risk of service disruption during an upgrade cycle.
The Future of Edge Infrastructure Management
Looking forward, the integration of automated patch management will likely become a non-negotiable feature for management consoles. The current manual cycle is too slow to counter the speed of automated exploitation tools. We are moving toward an era where the management center must not only detect threats but also self-heal by applying micro-patches to its own interface without requiring a full system reboot or lengthy downtime.
There is also a growing push for more resilient administrative platforms that utilize containerized microservices instead of a monolithic architecture. By isolating the web-based management interface from the core policy engine, vendors can ensure that a breach in the front end does not lead to a total system compromise. This structural evolution will be essential for maintaining the integrity of the network edge against increasingly sophisticated state-sponsored actors.
Final Assessment of Cisco Secure Firewall Management
The evaluation of the Cisco Secure Firewall Management Center revealed a platform that remains at the top of its class for orchestration and visibility, yet faces unprecedented scrutiny due to its role as a high-value target. Security professionals recognized that the very features making the FMC powerful—its centralized control and deep integration—also created a concentrated risk profile. The necessity of rapid response became clear as the industry grappled with defects that bypassed authentication entirely, proving that even the strongest defenses require constant maintenance.
Moving forward, the focus shifted toward a more modular approach to security management, where the “nerve center” is treated as a dynamic entity rather than a static appliance. Organizations began prioritizing platforms that offered not just visibility, but also architectural resilience against lateral movement within the management layer itself. The ultimate takeaway was that while centralized management is essential for scale, its success depends on a culture of aggressive patching and a refusal to trust the perimeter of the management interface.