Zero-Day Vulnerabilities
Threats and Vulnerabilities
US Agencies Pull Out of RSAC Over New CEO Hire
In a move that sent shockwaves through the global cybersecurity community, the digital guardians of the United States have abruptly vanished from the speaker list of the world's most influential cybersecurity gathering, the RSA Conference.
Feature Article Read More Threats and Vulnerabilities
Brakeman Finds Security Flaws in Rails Apps
The rapid pace of modern software development often creates a hidden tension between delivering features quickly and ensuring the underlying code is secure, a reality that is especially pertinent for applications built with popular frameworks like Ru...
Read More Threats and Vulnerabilities
Critical vm2 Flaw Allows Node.js Sandbox Escape
A newly discovered critical vulnerability in the widely implemented vm2 sandboxing library for Node.
Read More Threats and Vulnerabilities
CISA Details Path to Post-Quantum Cryptography
The rapidly approaching era of quantum computing carries with it a paradigm-shifting threat to global cybersecurity, promising to render today's encryption standards obsolete. In response, the U.S.
Market Analysis Read More Threats and Vulnerabilities
ISC BIND Vulnerability – Review
The intricate system of domain name resolution that underpins the entire digital world often operates invisibly, yet a single flaw within its core software can have cascading effects that bring essential services to a halt.
Technology Review Read More Threats and Vulnerabilities
Is Your LastPass Master Password at Risk?
The security of your entire digital life could hinge on a single, well-crafted email designed to manipulate your trust in the very service meant to protect you.
How-To Guide Read More Threats and Vulnerabilities
Trend Analysis: Exposed Testing Environments
The very tools designed to sharpen a company's cybersecurity defenses are ironically becoming the unguarded, publicly accessible entry points for sophisticated attackers.
Trend AnalysisTrending
Read More Threats and Vulnerabilities
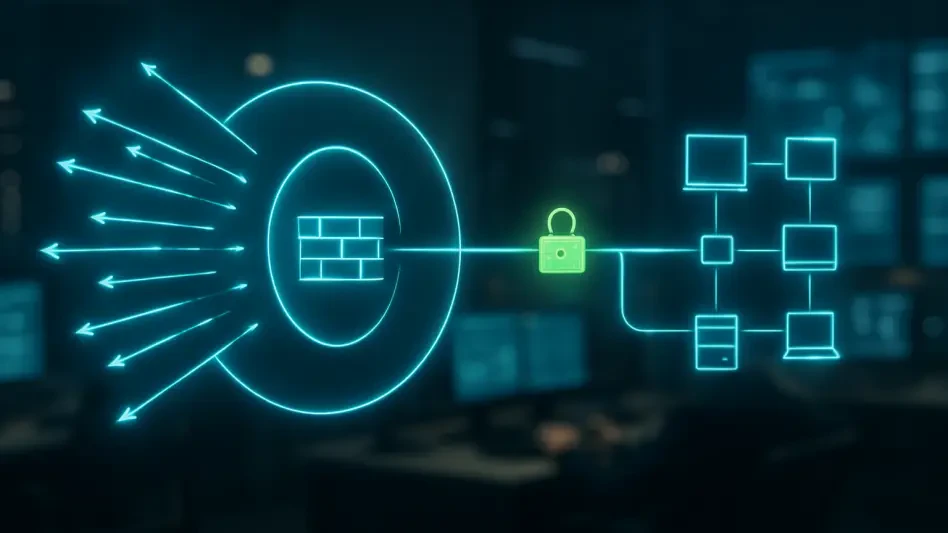
How Did a WAF Flaw Expose Cloudflare Customer Servers?
Web Application Firewalls stand as the digital sentinels for countless online services, meticulously inspecting incoming traffic to filter out malicious requests before they can reach vulnerable servers.
Read More
Get our content freshly delivered to your inbox. Subscribe now ->
Receive the latest, most important information on cybersecurity.