Social Engineering

Incident Response and Forensics
How Does Microsoft Device Code Phishing Bypass MFA?
Security professionals have spent years drilling the importance of checking URLs and verifying certificates into the minds of everyday users, yet a modern class of cyberattack is rendering these traditional defenses almost entirely obsolete.
Read More Human Factors in CyberSecurity
SLH Hackers Recruit Women to Enhance Vishing Operations
The sophistication of voice-phishing has reached a critical threshold as organized cybercriminal syndicates move away from brute-force methods toward refined psychological manipulation.
Read More Cyberсrime and Cyber Warfare
How Did the US Seize $61 Million From a Pig Butchering Scam?
The recent execution of a federal seizure involving over sixty-one million dollars in Tether serves as a stark reminder of the sophisticated nature of modern cryptocurrency investment fraud.
Read More Human Factors in CyberSecurity
How Is AI Fueling the Global Surge in Phishing Attacks?
The rapid evolution of generative artificial intelligence has fundamentally altered the digital threat landscape, enabling cybercriminals to launch more sophisticated and convincing phishing campaigns than ever before.
Read More Human Factors in CyberSecurity
How Is AI Personalizing Modern Phishing Scams?
The digital landscape is currently witnessing a paradigm shift in the methodology of cybercrime as traditional "spray and pray" tactics give way to sophisticated, data-driven operations.
Read More Human Factors in CyberSecurity
XWorm Remote Access Trojan – Review
The boundary between amateur script-kiddie tools and state-sponsored espionage kits has blurred into a gray zone where modularity and stealth are now accessible for a mere subscription fee.
Technology Review Read More Human Factors in CyberSecurity
GitHub Fund Secures the AI Software Supply Chain
The rapid evolution of artificial intelligence and modern cloud infrastructure is built upon a vast, interconnected web of open source software, a foundational layer that often operates as the unseen engine driving global technology.
Read More Human Factors in CyberSecurity
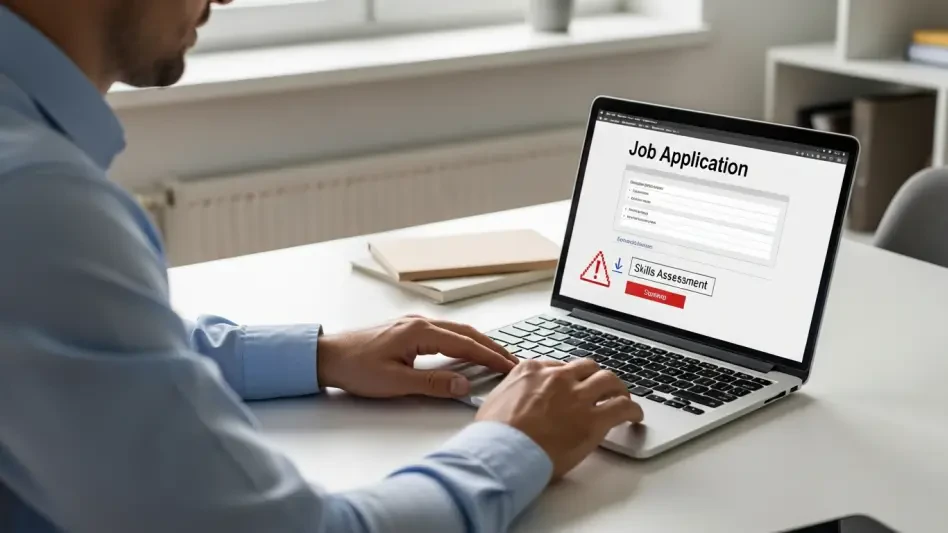
Noodlophile Malware Pivots to Target Job Seekers
A highly deceptive information-stealing malware campaign has undergone a significant transformation, now leveraging the anxieties and aspirations of job seekers to distribute its malicious payload.
Trending
Read More 
Get our content freshly delivered to your inbox. Subscribe now ->
Receive the latest, most important information on cybersecurity.