Social Engineering

Human Factors in CyberSecurity
What Is the New Face of Information Security?
The archetypal image of a cybersecurity professional, once confined to a hooded figure in a dark room illuminated only by lines of code, has become a relic of a bygone era.
Trending
Read More Human Factors in CyberSecurity
$50M Phishing Heist Sparks Volatility and New Trade Plays
A sophisticated phishing attack resulting in the theft of $50 million in USDT from a major crypto investor has sent shockwaves across the digital asset landscape, highlighting severe security vulnerabilities while simultaneously creating a complex ne...
Read More Human Factors in CyberSecurity
AI Cyberattacks Force Small Businesses to Raise Prices
The seemingly unrelated price hike at a local bakery or favorite online shop may actually be a direct consequence of an increasingly sophisticated digital war being waged against small enterprises, creating a hidden tax on consumers.
Feature Article Read More Threats and Vulnerabilities
Device Code Phishing Breaches Microsoft 365 Accounts
A sophisticated social engineering campaign is successfully turning a legitimate Microsoft security feature into a powerful tool for cybercriminals and state-sponsored actors, enabling them to bypass conventional defenses and gain unauthorized access...
Trending
Read More Threats and Vulnerabilities
Are Russian Hackers Targeting Your Network Edge?
The digital perimeter that once promised security for critical infrastructure has now become the most exploited frontier in an escalating campaign of cyber aggression waged by state-sponsored threat actors.
Industry Report Read More Human Factors in CyberSecurity
How Can an Image and Discord Compromise a Government?
A meticulously crafted email, seemingly from a trusted colleague within a government agency, can serve as the digital key that unlocks a nation's most sensitive information, a scenario that became a stark reality in a recent sophisticated cyberattack...
Read More Human Factors in CyberSecurity
Is Cloudflare Pages the New Phishing Haven?
The very digital infrastructure designed to build a faster and more secure internet is now being masterfully manipulated by threat actors to deceive unsuspecting users and steal their most sensitive information.
How-To Guide Read More Incident Response and Forensics
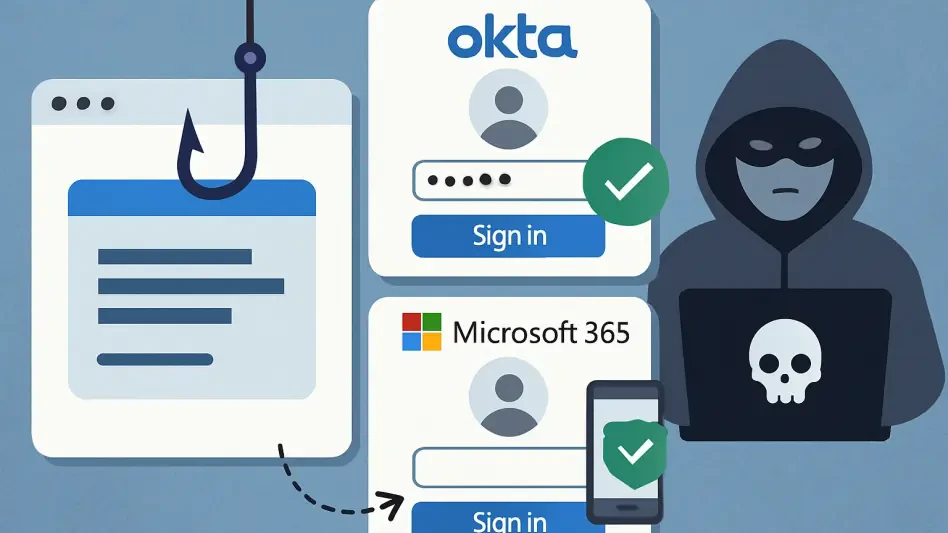
Phishing Attack Bypasses Okta and Microsoft 365 MFA
A recently uncovered and highly sophisticated Adversary-in-the-Middle phishing campaign is actively targeting organizations utilizing Microsoft 365 and Okta, successfully circumventing the multi-factor authentication protections that many businesses...
Read More
Get our content freshly delivered to your inbox. Subscribe now ->
Receive the latest, most important information on cybersecurity.