Password Forensics & Identity Compromise Recovery

Incident Response and Forensics
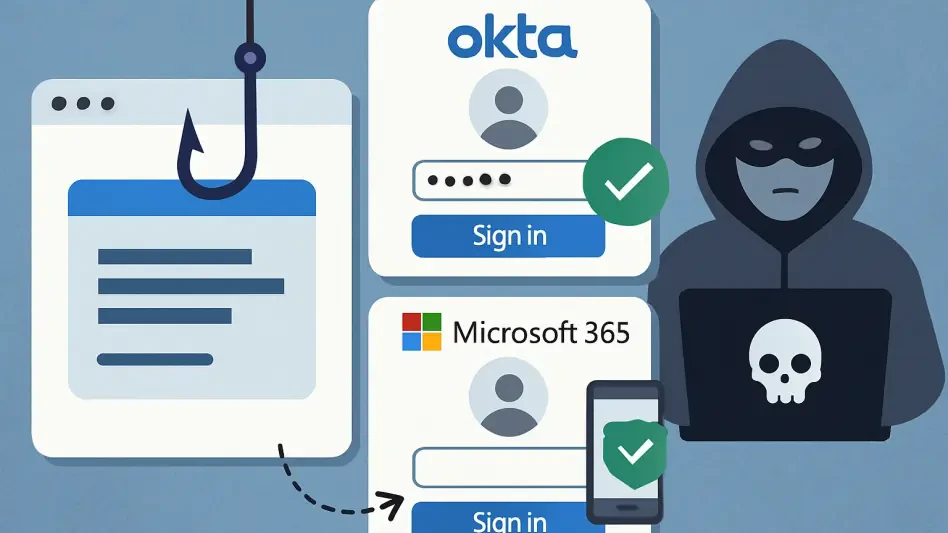
Phishing Attack Bypasses Okta and Microsoft 365 MFA
A recently uncovered and highly sophisticated Adversary-in-the-Middle phishing campaign is actively targeting organizations utilizing Microsoft 365 and Okta, successfully circumventing the multi-factor authentication protections that many businesses...
Read More Incident Response and Forensics
Is Your Mac at Risk From Malicious AI Chats?
The increasing integration of artificial intelligence into daily digital life has created a landscape where users confidently turn to AI chatbots for quick solutions, from drafting emails to troubleshooting technical issues on their computers.
Read More Incident Response and Forensics
AI Identity Theft Fears Grow Among UK Homebuyers
The already fraught process of purchasing a home in the United Kingdom has become burdened by a new and growing anxiety, as a recent survey reveals that 62 percent of consumers now fear their identity could be compromised by fraudsters using sophisti...
Trending
Read More Incident Response and Forensics
Is a 2FA Flaw Bypassing Your Cal.com Password?
In an era where two-factor authentication (2FA) is widely regarded as a fundamental layer of digital security, the discovery of a flaw that renders it ineffective can be particularly jarring for users who believe their accounts are adequately protect...
Read More Incident Response and Forensics
How Did One Stolen Car Unravel a Fraud Empire?
An unexpected letter arriving in a Bexar County mailbox set in motion a chain of events that would expose a sprawling and sophisticated identity theft ring operating in the heart of Texas.
Read More Incident Response and Forensics
NCRB 2025: Cybercrime Surges, Forensic Infrastructure Expands
What happens when a single tap on a smartphone screen can unravel your entire financial life? In India, this chilling scenario is no longer just a fear but a stark reality for thousands.
Feature Article Read More Incident Response and Forensics
Fake ChatGPT Browser Used in ClickFix Attack to Steal Passwords
Imagine stumbling upon a sleek, promising browser download that claims to integrate the power of advanced AI, only to discover too late that it’s a trap designed to snatch your most sensitive information.
Read More Incident Response and Forensics
1.3 Billion Passwords Exposed on Dark Web—Check Yours Now
Imagine logging into your favorite online account only to discover that your password, the one you’ve used across multiple platforms for years, is floating around on the dark web for any cybercriminal to snatch up.
Read More
Get our content freshly delivered to your inbox. Subscribe now ->
Receive the latest, most important information on cybersecurity.