Global Cyberattacks & Response

Cyberсrime and Cyber Warfare
How Is Iranian Cyber Warfare Reshaping Global Security?
The rapid transformation of Iranian cyber operations from localized digital disruptions into a cohesive instrument of global power projection has fundamentally altered the calculus of modern international security.
Industry ReportTrending
Read More Cyberсrime and Cyber Warfare
Iranian State Actors Target Stryker in Major Cyberattack
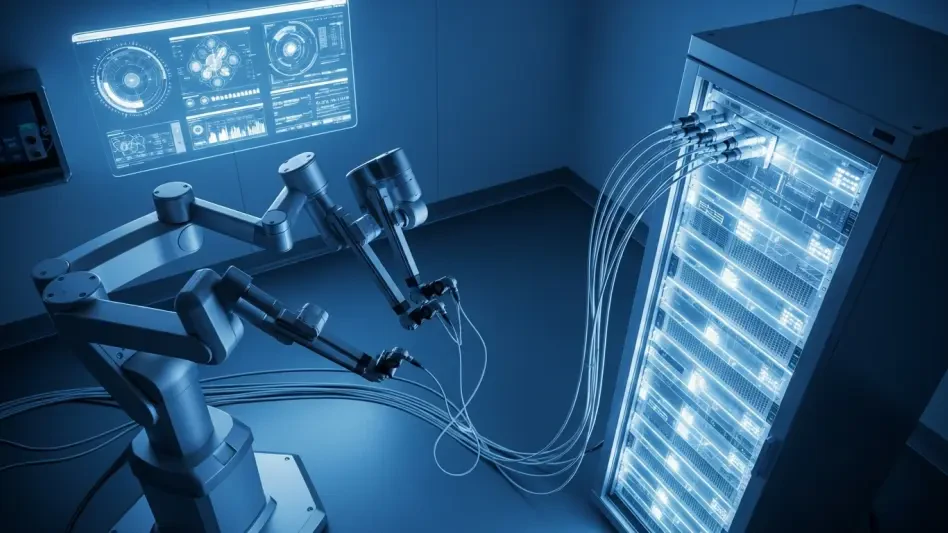
The vulnerability of the global healthcare supply chain became painfully evident this week as Stryker, a titan in the medical technology sector, grappled with a sophisticated cyberattack that disrupted critical life-saving operations across several c...
Read More Cyberсrime and Cyber Warfare
Is the Global Fight Against Commercial Spyware Faltering?
The global market for high-end digital surveillance has reached a volatile equilibrium where state-sanctioned crackdowns and lucrative private acquisitions are simultaneously reshaping the industry's future.
Market Analysis Read More Cyberсrime and Cyber Warfare
Is Your Business Prepared for a Total Digital Wipeout?
The flickering glow of a single smartphone screen became the only source of light for thousands of employees as their workstations simultaneously dissolved into blackness during a coordinated digital execution.
Feature Article Read More Cyberсrime and Cyber Warfare
Operation Lightning Dismantles Massive SocksEscort Botnet
Digital invisibility has long served as the primary currency for cybercriminals who exploit residential connections to mask their malicious footprints from the watchful eyes of global security agencies.
Research Summary Read More Threats and Vulnerabilities
Finland Identifies Russia and China as Primary Cyber Threats
The geopolitical stability of Northern Europe currently faces an unprecedented challenge as digital borders become the primary battleground for state-sponsored actors seeking to undermine national sovereignty through silent, persistent, and highly so...
Read More Threats and Vulnerabilities
New Zombie ZIP Exploit Bypasses 98% of Antivirus Engines
A single structural anomaly in a standard ZIP file can currently render 50 out of 51 top-tier security scanners completely blind to the presence of malicious code.
Feature Article Read More Cyberсrime and Cyber Warfare
Medical Technology Cybersecurity – Review
The systematic dismantling of a global medical giant’s digital footprint within hours has redefined the stakes of digital safety in the healthcare sector.
Technology Review Read More
Get our content freshly delivered to your inbox. Subscribe now ->
Receive the latest, most important information on cybersecurity.