Fraud & Financial Cybercrime

Cyberсrime and Cyber Warfare
How Did UNC3886 Breach Singapore's Telecoms?
A highly sophisticated cyber espionage campaign, which remained undetected for nearly a full year, successfully infiltrated the core of Singapore's telecommunications sector by exploiting a series of previously unknown vulnerabilities in widely used...
Read More Cyberсrime and Cyber Warfare
Trend Analysis: African Cybersecurity Maturity
The catastrophic data breach in Senegal, which laid bare the biometric and personal information of a vast portion of the nation's adult populace, serves as a powerful and troubling signal for the entire continent.
Trend Analysis Read More Cyberсrime and Cyber Warfare
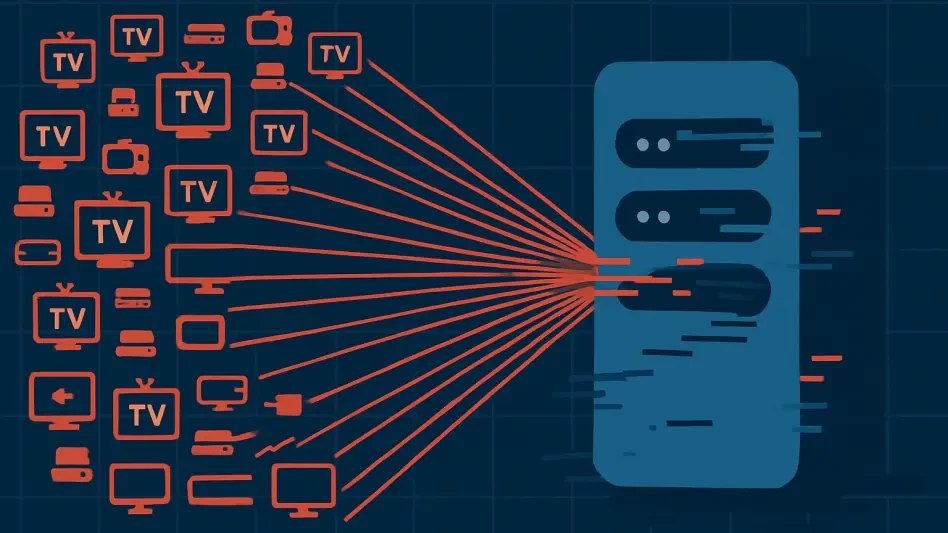
Streaming Boxes Used in Largest Ever Cyberattack
The seemingly innocuous streaming boxes that have become a common fixture in living rooms around the world have been unmasked as unwitting soldiers in a digital army, contributing to the largest distributed denial of service attack ever recorded.
Read More Cyberсrime and Cyber Warfare
Is 0APT Ransomware a Real Threat or an Elaborate Hoax?
In the ever-shifting landscape of cybercrime, the emergence of a new ransomware group is hardly unusual. However, the recent debut of a syndicate known as 0APT has sent ripples of both skepticism and concern throughout the cybersecurity community.
Market Analysis Read More Cyberсrime and Cyber Warfare
Could a Default Password Take Down a Power Grid?
A recent cyberattack that brought Poland's energy grid to the brink of a widespread blackout serves as a stark reminder that the security of national infrastructure can hinge on something as simple as a factory-set password.
Industry Report Read More Cyberсrime and Cyber Warfare
Was Card Data Safe in BridgePay's Ransomware Attack?
The confirmation of a cyberattack against a major payment processor instantly triggers widespread concern, focusing public attention squarely on the security of personal financial information.
FAQ Read More Cyberсrime and Cyber Warfare
How Did a Software Flaw Expose the EU Commission?
The very software designed to fortify thousands of government mobile devices against intrusion became the unlocked door through which attackers compromised the European Commission’s central command, revealing a critical vulnerability at the heart of...
Feature Article Read More Cyberсrime and Cyber Warfare
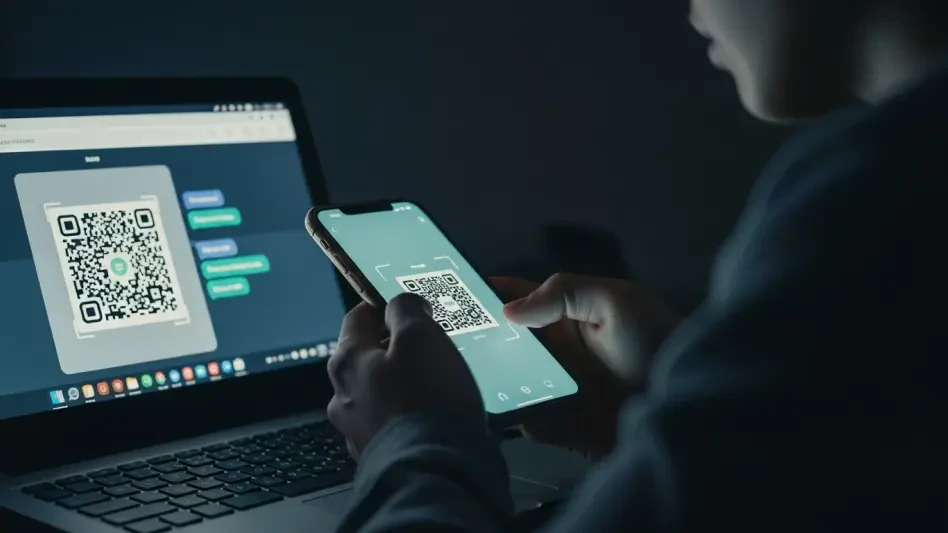
Trend Analysis: QR Code Social Engineering
That seemingly harmless black-and-white square you scan for a restaurant menu or a quick payment now serves as a potential gateway for sophisticated cybercriminals.
Trend Analysis Read More
Get our content freshly delivered to your inbox. Subscribe now ->
Receive the latest, most important information on cybersecurity.