Exploitation Techniques

Threats and Vulnerabilities
Trend Analysis: Cyber Exposure Management
The first critical alert of a breach ignites a frantic race against time within the Security Operations Center, a disorganized scramble where context is the most valuable and elusive commodity.
Trend Analysis Read More Threats and Vulnerabilities
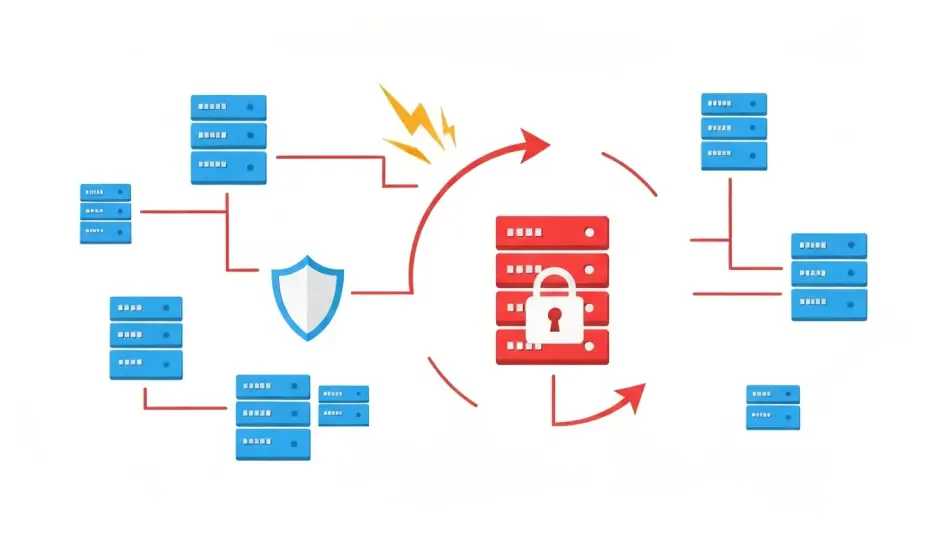
Internal Blind Spots Are a Critical Cybersecurity Risk
Most organizations meticulously fortify their digital walls, building what they believe to be an impenetrable fortress against external threats, yet remain completely oblivious to the sophisticated adversaries already operating freely within their tr...
Feature Article Read More Threats and Vulnerabilities
Critical Fortinet Flaw From 2020 Is Actively Exploited
A security vulnerability that first surfaced years ago has dramatically re-emerged, serving as a stark reminder that in the world of cybersecurity, old threats never truly die; they simply wait for an unpatched system to provide an opportunity.
Best Practices Guide Read More Threats and Vulnerabilities
Arcane Werewolf's Evolving Malware Hits Russian Industry
A sophisticated cyber threat actor has been methodically targeting Russia's industrial base with a persistent and continuously refined campaign, underscoring the growing danger of tailored malware in corporate espionage and disruption.
Read More Threats and Vulnerabilities
Could a Capital Letter Break Your Fortinet MFA?
The complex architecture of modern cybersecurity often hinges on deceptively simple points of failure, where something as mundane as a single character's case can dismantle carefully constructed defenses.
Feature Article Read More Threats and Vulnerabilities
Can Hackers Steal Your M365 Account With MFA?
Multi-Factor Authentication (MFA) has long been championed as a critical defense against account takeovers, but a sophisticated phishing technique is now demonstrating that even this robust security layer can be circumvented by manipulating legitimat...
Read More Threats and Vulnerabilities
Is Your n8n Server Vulnerable to Critical RCE?
A critical remote code execution vulnerability has been uncovered within the popular n8n open-source workflow automation platform, posing an immediate and severe threat to a vast number of installations.
Read More Threats and Vulnerabilities
Trend Analysis: React2Shell Vulnerability Exploits
The digital alarm bells that rang with the disclosure of the critical React2Shell vulnerability have now escalated into a full-blown siren as threat actors pivot from stealthy intrusion to high-stakes ransomware.
Trend Analysis Read More
Get our content freshly delivered to your inbox. Subscribe now ->
Receive the latest, most important information on cybersecurity.