Cybercrime Legislation

Cyberсrime and Cyber Warfare
From Checklists to Control: Cyber Sovereignty in OT
A routine vendor patch that fanned out across turbines, substations, and treatment plants before sunrise forced a sharper question than any audit checklist ever had the nerve to ask: who truly owns the off switch when code crosses borders and remote...
Feature ArticleTrending
Read More Cyberсrime and Cyber Warfare
Inside the Zero-Day Economy: From State Secrets to Crimeware
A quiet marketplace now sets the tempo of digital conflict by turning obscure software flaws into time-sensitive leverage, where a single zero-click iPhone chain can fetch millions precisely because it offers covert access before a patch closes the d...
Trending
Read More Cyberсrime and Cyber Warfare
Anthropic’s Mythos Model Redefines Global Cybersecurity
The traditional boundaries of network security have effectively dissolved under the weight of machine-learning systems that operate with a level of autonomy previously reserved for speculative fiction.
Market Analysis Read More Cyberсrime and Cyber Warfare
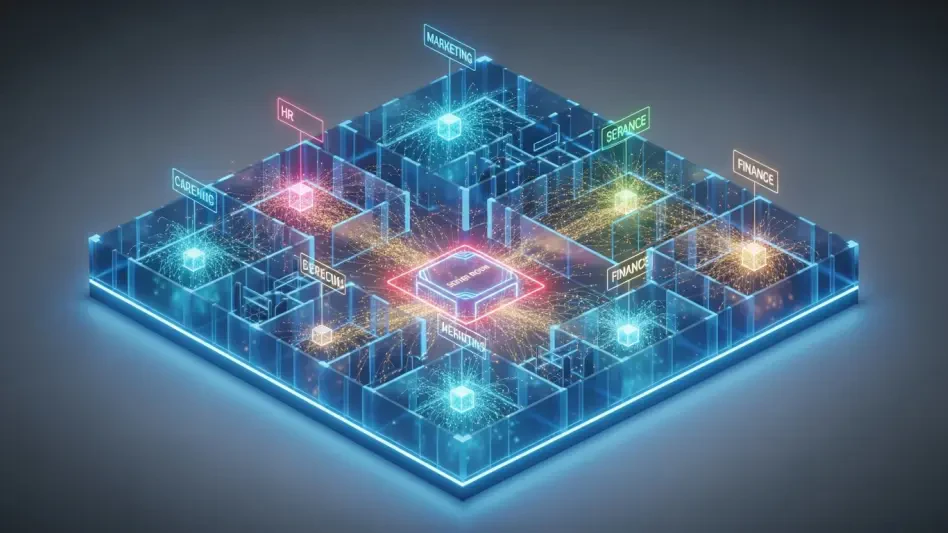
Is Fragmentation the Weakest Link in US Cyber Power?
The realization that the most sophisticated digital arsenal on the planet can be neutralized by internal bureaucracy represents the most significant strategic challenge facing American national security today, especially as traditional concepts of de...
Read More Cyberсrime and Cyber Warfare
Is Recovery Enough to Stop Modern Ransomware Extortion?
The realization that a robust backup strategy no longer serves as a comprehensive shield against the sophisticated extortion tactics employed by modern cybercriminal syndicates has sent shockwaves through boardrooms across the global enterprise lands...
Read More Human Factors in CyberSecurity
How Did Scattered Spider Steal $8 Million in Crypto?
The realization that a small group of young, native English-speaking hackers could systematically dismantle the security of multi-billion dollar corporations serves as a stark reminder of the inherent vulnerabilities in modern digital infrastructure.
Trending
Read More Cyberсrime and Cyber Warfare
Is Poland Entering a New Era of Destructive Cyber Warfare?
The silent hum of the national power grid became a terrifying omen on a frigid winter night when digital code nearly paralyzed the warmth of half a million homes across the Polish landscape.
Feature Article Read More Human Factors in CyberSecurity
Is Cybersecurity a Technical Issue or a Strategic Risk?
The digital landscape of 2026 has transformed the quiet hum of server rooms into the high-stakes heartbeat of corporate boardrooms, where a single oversight can now trigger a multimillion-dollar regulatory collapse.
Feature Article Read More
Get our content freshly delivered to your inbox. Subscribe now ->
Receive the latest, most important information on cybersecurity.