Configuration Security

Threats and Vulnerabilities
What Is the Hidden Power of a Simple Tap?
Behind the almost magical convenience of a simple tap lies a quiet but profoundly powerful revolution that is fundamentally reshaping our daily lives in ways many have yet to fully appreciate.
Read More Threats and Vulnerabilities
Trend Analysis: Cybercrime as a Service
The modern cybercriminal no longer lurks in a dimly lit basement but instead operates from a slick digital marketplace, purchasing sophisticated attack tools with the ease of ordering office supplies.
Trend Analysis Read More Threats and Vulnerabilities
Can Your AI IDE Execute Code Without You Knowing?
The promise of artificial intelligence integrated directly into development environments has revolutionized coding workflows, offering unprecedented speed and assistance, but this tight integration may also conceal novel security vulnerabilities capa...
Read More Cyberсrime and Cyber Warfare
Global Agencies Set New Principles for OT Security
The intricate network of operational technology that powers our cities, purifies our water, and manages our energy grids is undergoing a profound and perilous transformation, creating an urgent need for a globally recognized standard of security.
Research Summary Read More Threats and Vulnerabilities
Install Windows Configuration Designer Using Winget
Deploying a fleet of Windows devices with consistent settings presents a formidable challenge for IT administrators, often involving repetitive manual configurations that are both time-consuming and prone to human error.
Read More Threats and Vulnerabilities
Password Management Is a Critical Compliance Control
Countless organizations are caught in a frustrating cycle, investing millions in sophisticated cybersecurity tools only to fail routine compliance audits because of something as elementary as a password.
Read More Threats and Vulnerabilities
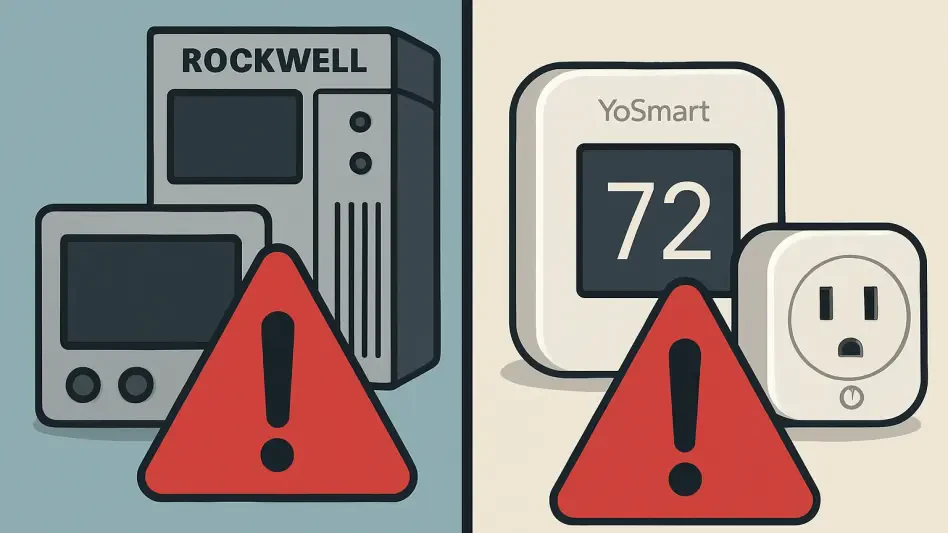
Critical Flaws Found in Rockwell and YoSmart Systems
The once-distinct lines separating industrial control systems from consumer smart home devices have blurred significantly, creating an interconnected technological landscape where a vulnerability in one domain can offer critical lessons for the secur...
Best Practices Guide Read More Threats and Vulnerabilities
Russian Spy Group BlueDelta Evolves Phishing Attacks
In the high-stakes realm of international espionage, the most potent weapons are no longer just physical; they are lines of code meticulously crafted to exploit the single greatest vulnerability in any security system: human trust.
Feature Article Read More
Get our content freshly delivered to your inbox. Subscribe now ->
Receive the latest, most important information on cybersecurity.