Best Practices Guide Threats and Vulnerabilities
In the high-stakes realm of international espionage, the most potent weapons are no longer just physical; they are lines of code meticulously crafted to exploit the single greatest vulnerability in any security system: human trust.
Feature Article Read MoreBeneath the surface of global geopolitics, a relentless and largely unseen conflict is being waged across digital networks, systematically chipping away at the foundations of American critical infrastructure.
Roundup Article Read MoreA fundamental transformation is reshaping the aviation industry’s technological core as the long-standing paradigm of hardware-centric flight decks gives way to a dynamic, software-defined avionics (SDA) architecture.
Read MoreA ticking clock of unpatched vulnerabilities silently counts down within the digital infrastructure of nearly every organization, creating a persistent and often invisible threat to business continuity.
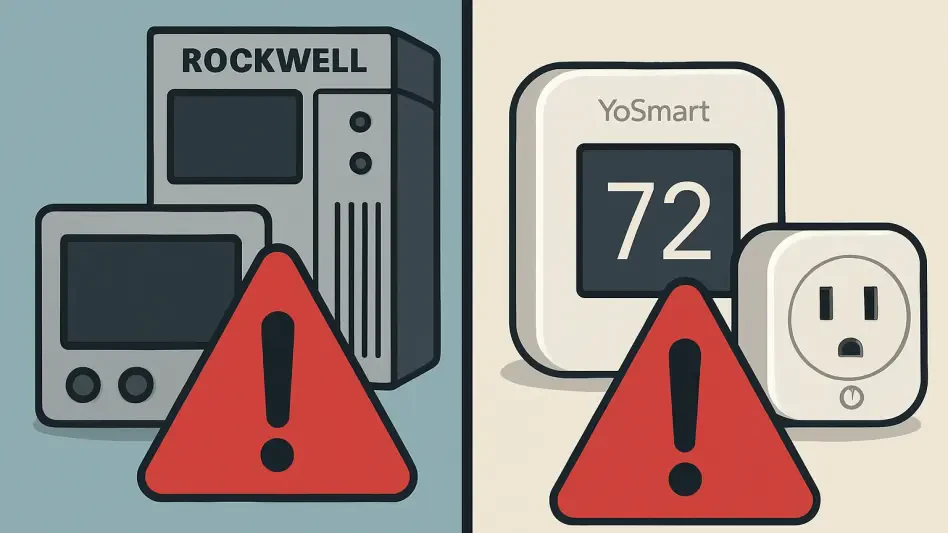
Trend Analysis Read MoreThe public release of a sophisticated proof-of-concept exploit has sent a significant alert across the cybersecurity landscape, highlighting a critical vulnerability that disproportionately affects a massive number of older but still widely used 32-b...
Read MoreIn the hyper-digitized landscape of modern security, the most profound lessons about protecting critical data come not from the latest malware strain but from the dusty case files of Cold War-era traitors.
Feature Article Read MoreThe silent hum of a nation's power grid has become the new frontline in digital warfare, where the algorithms designed to optimize energy flow are now the very vulnerabilities targeted by sophisticated state-sponsored adversaries.
Industry Report Read MoreA sophisticated ransomware strain is systematically dismantling the digital defenses of healthcare organizations by turning their own administrative tools into weapons of cyber warfare, marking a dangerous evolution in extortion tactics.
Research Summary Read More
Get our content freshly delivered to your inbox. Subscribe now ->
Receive the latest, most important information on cybersecurity.
