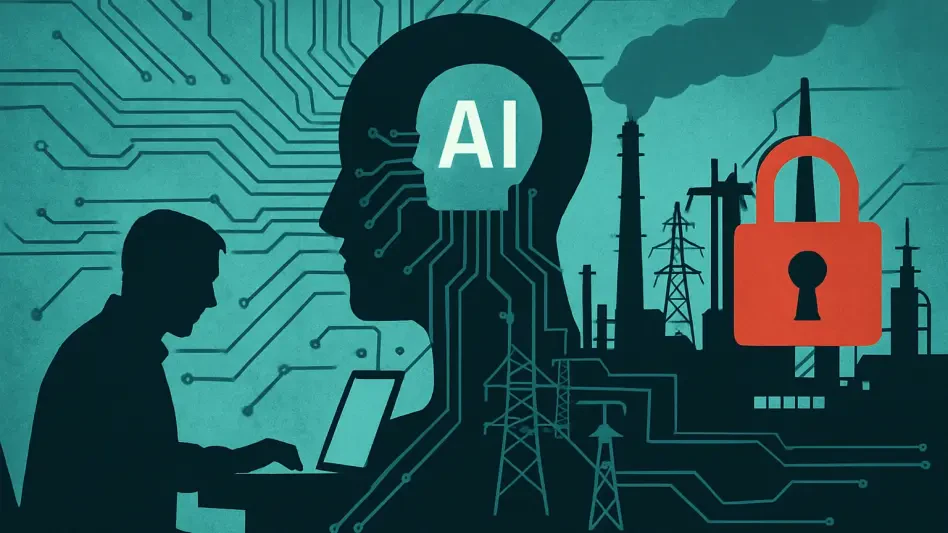
Modern software development relies heavily on the seamless integration of external libraries, yet this convenience often masks the sophisticated dangers lurking within the digital supply chain. When a developer pulls a package like NCryptYo or DOMOAut##_ into an ASP.NET project, they are not just adding functionality; they are potentially inviting a silent adversary into their production environment. Recent investigations into malicious packages published by an actor known as hamzazaheer highlight a disturbing trend where trust is weaponized against the very people building the modern web. These libraries, which have already seen thousands of downloads, represent a surgical strike against the .NET ecosystem, targeting everything from sensitive login credentials to the structural integrity of ASP.NET Identity data. This shift demonstrates that threat actors are no longer content with just disrupting service; they are now focused on long-term persistence and the systematic harvesting of user roles and permission mappings within live applications, creating a scenario where a single package update can compromise an entire enterprise.
Deceptive Architecture: Sophisticated Mimicry and Obfuscation
The primary strength of these malicious libraries lies in their ability to blend into the professional environment by utilizing deceptive naming conventions and structural mimicry to bypass developer scrutiny. For example, the NCryptYo package utilizes typosquatting to impersonate the widely used NCrypto library, a tactic that exploits the fast-paced nature of modern coding where small spelling errors often go unnoticed. Once integrated, the internal DLL within the package further disguises itself by mimicking legitimate Microsoft Windows cryptography providers, making it appear as a standard component of the operating system’s security stack. To ensure immediate execution, the malware is designed to trigger as soon as the assembly loads via a static constructor, a technique that effectively silences standard security alerts. This constructor then initializes a local proxy on port 7152, which acts as a hidden bridge designed to relay sensitive data from the local environment to external, attacker-controlled servers without alerting the network administrators or monitoring tools.
Technical sophistication in these attacks is further evidenced by the implementation of Just-In-Time compiler hijacking, a method that hooks directly into the .NET runtime to manage how code is executed. By utilizing this advanced technique, the malware ensures that its primary malicious payload remains fully encrypted within the application’s memory until the exact moment of execution, rendering static analysis tools virtually useless. This level of obfuscation is why research from security platforms initially showed that only one out of seventy-two security vendors flagged the malicious DLL as a threat. Furthermore, the packages utilize .NET Reactor obfuscation alongside various anti-debugging checks and encrypted resources to hide their true functionality from even the most seasoned security analysts. This multi-layered approach to defense-evasion ensures that the malware can operate undetected for extended periods, allowing it to harvest data and establish backdoors while the developers remain under the impression that their application is functioning within safe parameters.
Execution and Impact: Beyond the Developer Workstation
The overarching trend highlighted by these incidents is the increasing vulnerability of the software supply chain as threat actors move beyond the developer’s workstation to target production users. While libraries like SimpleWriter_ focus on executing hidden processes and writing malicious files directly to the disk, packages such as DOMOAut##_ and IRAOAut##.0 specifically target the underlying identity infrastructure. By infiltrating the authentication layers of an ASP.NET application, these malicious components can intercept OAuth tokens and harvest sensitive user data, effectively compromising the trust relationship between a service and its customers. This shift in strategy indicates that the goal is no longer just simple data theft but the complete subversion of the application’s security model from the inside out. As these packages integrate themselves into the deployment pipeline, they become a permanent part of the software, allowing attackers to maintain access even if the initial vulnerability that allowed the package’s inclusion is later patched or updated.
Mitigating these risks required a shift toward a more proactive security posture that emphasized the rigorous verification of package origins and historical download patterns. Organizations moved toward integrating automated CI/CD pipeline scanning that specifically looked for indicators of obfuscation, static constructor abuse, and unusual localhost traffic patterns. It was determined that simply relying on the reputation of a repository was insufficient; instead, security teams began implementing sandboxed environments to analyze the behavior of new dependencies before they reached production. The consensus among security experts evolved to prioritize the use of allow-lists and internal mirrors of trusted packages to prevent the accidental introduction of typosquatted or malicious libraries. This incident served as a critical reminder that the integrity of an ASP.NET application is only as strong as its weakest dependency. Moving forward, the industry adopted more robust binary analysis and runtime protection measures to detect the subtle anomalies associated with JIT hijacking and local proxy creation.