Human Factors in CyberSecurity
Human Factors in CyberSecurity
Germany Probes Russia-Linked Signal Phishing of Officials
A single QR code, framed as emergency support inside a trusted app, quietly unlocked weeks of sensitive conversation as German federal prosecutors opened an espionage probe into a sweeping Signal account hijacking that hit the political establishment...
Read More Human Factors in CyberSecurity
Fake CAPTCHA Triggers Costly International SMS Fraud
A single tap on a fake puzzle page can quietly convert casual browsing into dozens of pricey international texts that land as delayed charges, weaponizing a harmless click into a billing trap that drains money and patience alike.
Best Practices Guide Read More Human Factors in CyberSecurity
Can ClickFix Prompts Turn Trusted Windows Tools Against You?
A single keystroke sequence urged by a counterfeit CAPTCHA and a chirpy “not a robot” note quietly hijacked routine habits, turning built‑in Windows helpers into stealthy launchpads for code execution that looked manual, benign, and therefore unremar...
Read More Human Factors in CyberSecurity
Microsoft-Signed Tool Abused to Spy on India’s Banks
Banks that spent years hardening their networks against noisy malware suddenly faced a quieter adversary that moved with the ease of a trusted guest, riding a Microsoft-signed developer binary to slip into sensitive systems and exfiltrate data withou...
Read More Human Factors in CyberSecurity
Phishing Reclaims Lead as AI Tools Exploit MFA Gaps
Email inboxes again opened the door for intrusions as phishing surged back to the top initial-access vector in the first quarter, propelled by AI-fueled kits and no-code tooling that collapsed setup time and raised the quality bar of fake login pages...
Read More Human Factors in CyberSecurity
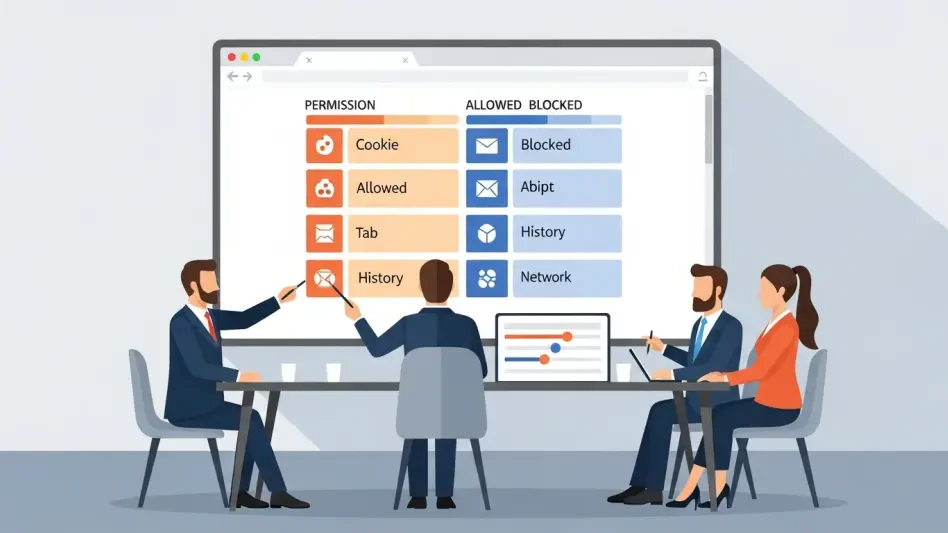
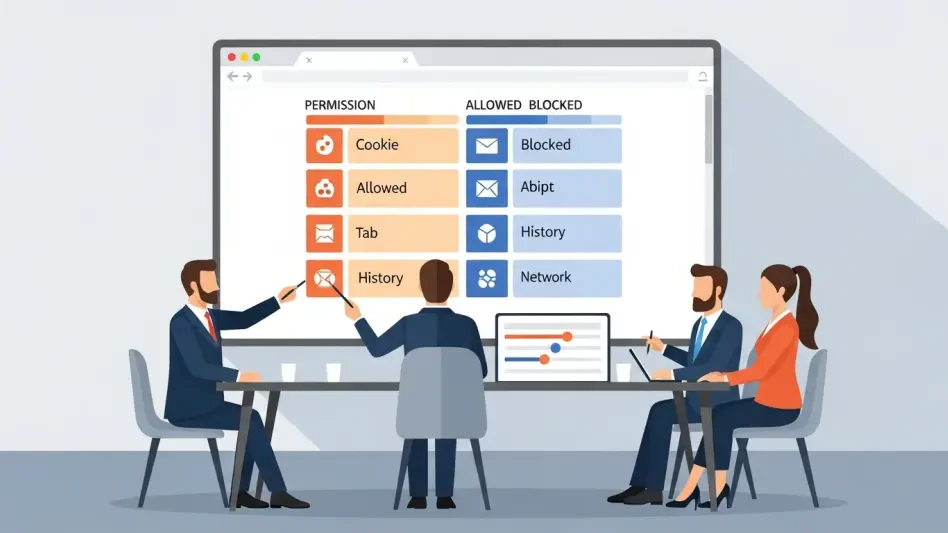
Why Is Identity Governance the New Cybersecurity Perimeter?
The traditional concept of a fortress protected by high walls and deep moats has vanished from the modern corporate landscape as digital assets migrate to the cloud.
Roundup Article Read More Human Factors in CyberSecurity
PiNetDEX Enhances Security With New Two-Factor Authentication
Digital asset management has reached a critical juncture where the convenience of mobile interfaces must harmonize with the unyielding security requirements of blockchain technology to protect global users.
Read More Human Factors in CyberSecurity
How Did Scattered Spider Steal $8 Million in Crypto?
The realization that a small group of young, native English-speaking hackers could systematically dismantle the security of multi-billion dollar corporations serves as a stark reminder of the inherent vulnerabilities in modern digital infrastructure.
Trending
Read More 
Get our content freshly delivered to your inbox. Subscribe now ->
Receive the latest, most important information on cybersecurity.